OTI, Access Now Urge FCC to Face the Facts on U.S. Broadband Availability

Today, New America’s Open Technology Institute (OTI) and Access Now filed comments urging the Federal Communications Commission (FCC) to recognize the inadequate state of broadband availability in the United States. Congress requires the FCC to report annually on whether advanced telecommunications capability “is being deployed to all Americans in a reasonable and timely fashion,” and to take “immediate action” if it is not. Earlier this year, the FCC concluded broadband deployment was sufficient, despite overwhelming evidence that the agency’s data has been flawed for years, overstating broadband deployment. The ongoing COVID-19 pandemic has further revealed the millions of Americans suffering without access to the internet. People across the country have been asked to socially distance and remain at home to work and learn, making it more important than ever to get everyone connected to telecommunications service, and for the agency to ensure that they publish a report accurately reflecting advanced telecommunications capability in the United States today.
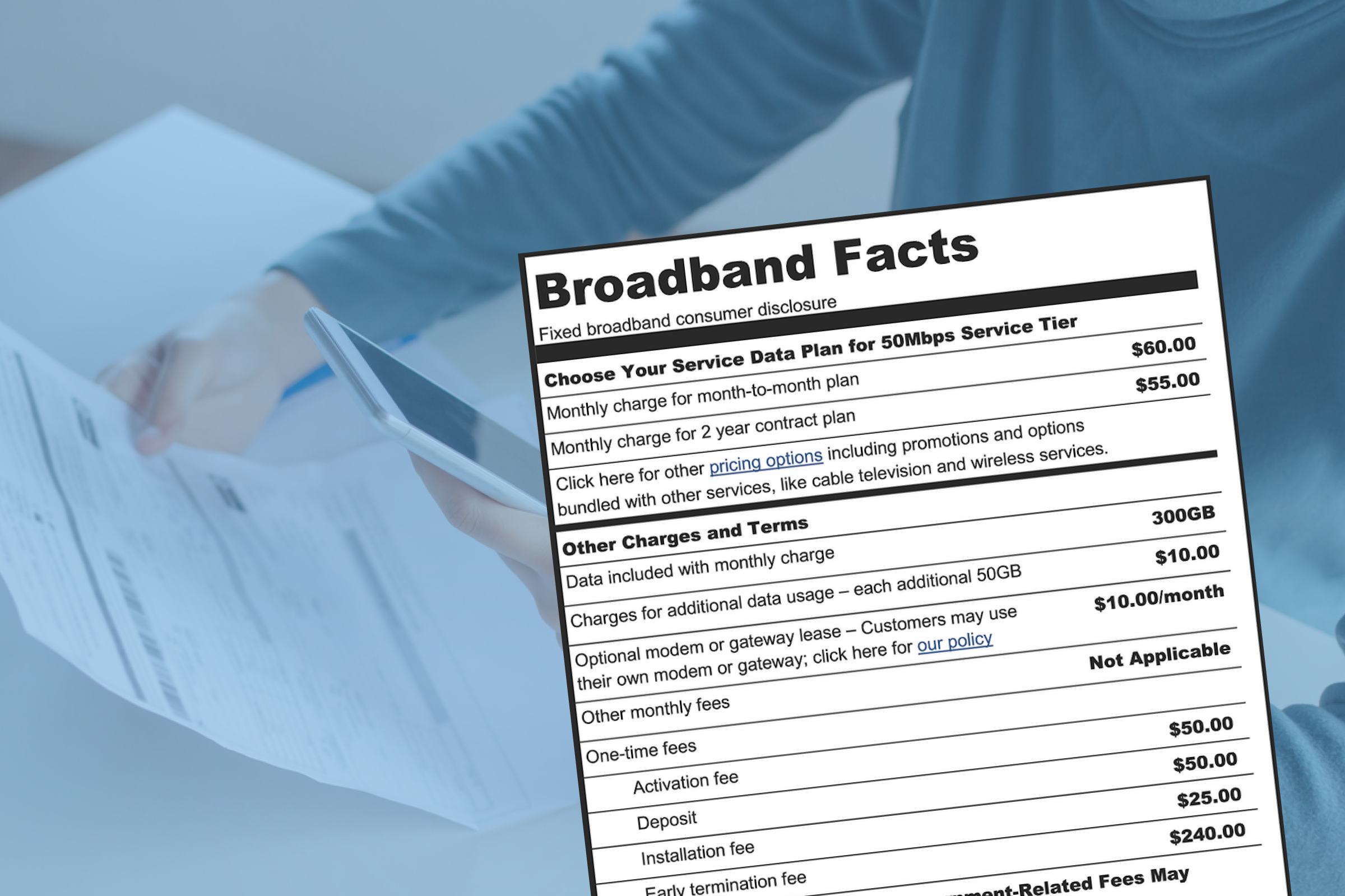
OTI and Access Now urge the FCC, specifically, to 1) increase the benchmark for broadband from 25/3 Mbps in download and upload speed; 2) determine that mobile broadband is a complement, not a substitute, to fixed broadband; 3) incorporate affordability as part of its Section 706 report, given the impact of affordability on broadband availability; and 4) ensure that its analysis of broadband availability does not depend on its flawed Form 477 data.
The following quote can be attributed to Claire Park, Program Associate at New America’s Open Technology Institute:
“This year’s annual Section 706 review must accurately represent broadband availability in the United States. With the pandemic exposing the deep and disproportionate harms of the digital divide, there is no better time than now for the FCC to identify the issues that perpetuate the digital divide. OTI urges the FCC to conduct a robust analysis of broadband availability and adopt policies that will ensure we get people connected now.”
The following quote can be attributed to Eric Null, U.S. Policy Manager at Access Now:
“Another year, another opportunity for the FCC to ignore the evidence about connectivity in the United States. Yet again we find ourselves making the same arguments to an FCC that is intent on doing anything it can to make industry look great (to justify an entirely deregulatory agenda) and to ignore the American people who continue to struggle, during a pandemic no less, to make ends meet and stay connected. Underrepresented communities, like low-income and Tribal communities, have long been left behind on the wrong side of the digital divide. This FCC’s unwillingness to help these communities will be a stain on its legacy.”