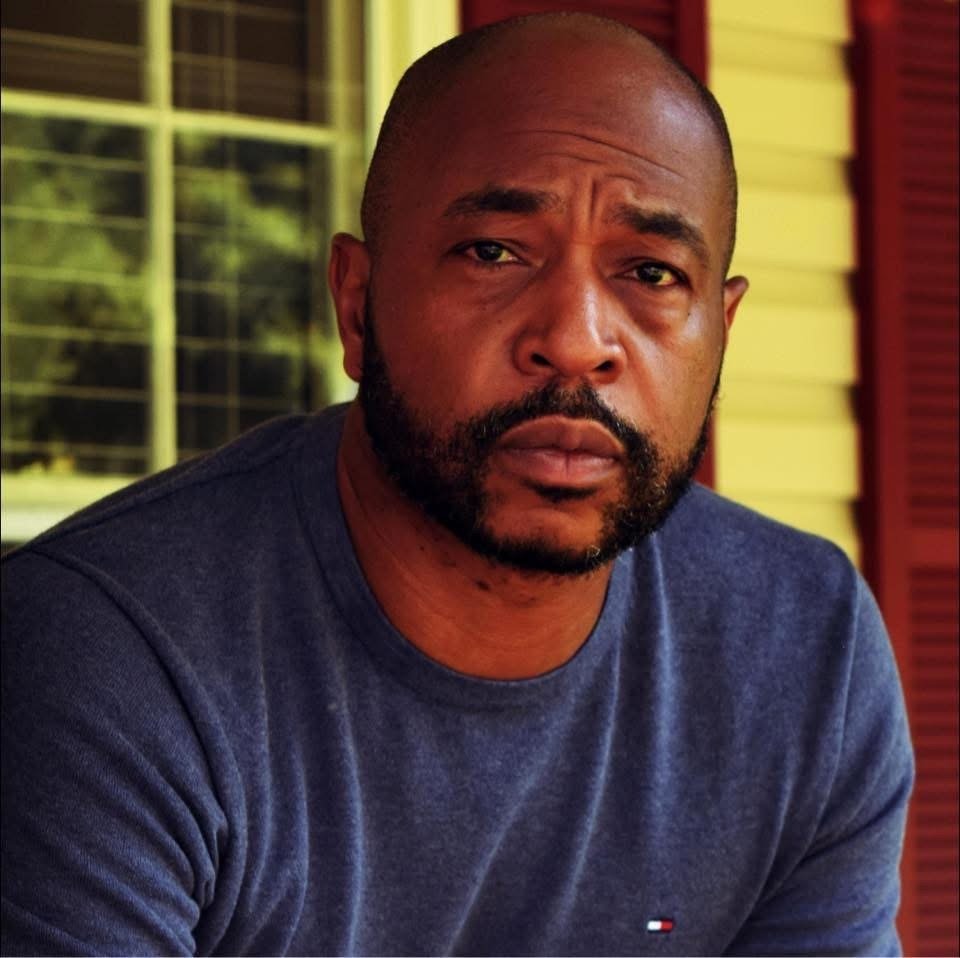
Theodore Johnson
Senior Advisor, Executive Office

For months
now, there’s been a blur of speculation and information suggesting Russia was
interfering in our presidential election. Early on, officials in the Obama
administration figured that the objective was simply to undermine faith and
confidence
in the electoral process. But over the weekend, a new CIA assessment brought it
all into focus: Russia turned to cyberspace to help Donald Trump win the election.
But
Russia’s cyberventionism—its apparent proclivity for conducting interventionism
via cyberspace—didn’t take the form of an attack we’d typically expect to see.
There were no denial-of-service attacks on state election systems or website
defacements like it conducted against Estonian and Georgian governments and
political parties in 2007 and 2008, respectively. And despite a number of pre-election reports citing voting-machine vulnerabilities,
anyone going in search of hacked precinct electoral computers is likely to come
up empty-handed.
So how
exactly did Russia hack the election? Well, it didn’t. It hacked us—the voters.
Why screw
around with inefficient, resource-intensive brute force hacks on voting
machines to flip ballots when you can simply convince voters to do it for you? In
other words, by targeting voters’ decision-making processes instead of the
machines that record their decisions, Russia could influence the election
without breaking into a single electoral computer.
This isn’t
new thinking. Hackers learned long ago that the most efficient way to break
into a computer wasn’t to try to outsmart firewalls and other network security
measures. It’s far easier to trick users into giving up their credentials or
unknowingly installing malware. Computer engineering turned to good
old-fashioned social engineering, in the form of phishing. (As you probably
know, phishing is when a hacker tries to dupe a user into giving up personal
information or credentials that can be used to compromise computers and
networks.) And it worked. Allan Paller, the director of research at the SANS
Institute, estimated in 2013 that 95 percent of all successful cyberattacks on
enterprise networks are the result of phishing, and cybersecurity firm
FireEye found in a report issued this year that phishing is the most
prevalent delivery method for advanced persistent threats.
In
cybersecurity circles, this is a well-known dilemma. So much so that network problems
are often traced to a phenomenon called PEBCAK, or “Problem Exists Between
Chair and Keyboard”—that is, a user. Russia aimed between the campaign and the
ballot box, and it targeted voters.
No one
familiar with Russian operations is particularly surprised by this approach. It’s
called information warfare, and its goal is to employ disinformation to
manipulate a target population into making choices it might not otherwise make.
I spent two decades as an information-warfare officer in the United States Navy,
and it’s common knowledge in military and intelligence circles that deception,
propaganda, and psychological operations are hallmarks of Russian doctrine. So on
Sunday when Sen. Claire McCaskill called Russia’s intervention in the election
“a form of warfare,” this is exactly what
she meant.
How’d they
do it? Basically, by doxxing the Democrats and unleashing fake news. Russia was
behind the stories that dominated our headlines, both real and fabricated, for
several weeks leading up to the election. In doing so, it bet that casting
further doubt on Clinton’s honesty and character while also polluting the
information environment with false stories would affect the decisions of enough
voters to increase Trump’s chances. It wagered that in a close election,
perhaps it could be the difference
We now
know that two Russian intelligence groups hacked into the Democratic National
Committee’s email server in the spring and, over time, stole tens of thousands
of emails and documents. Then in July, just before the start of the Democratic
National Convention, WikiLeaks released nearly 30,000 of them, revealing the
DNC’s inner workings, private conversations between staffers, and campaign
tactics. In October, it made publicly available the text of some of Hillary
Clinton’s high-paid speeches to Wall Street, which she’d refused to discuss at
length. Shortly thereafter, nearly a full month before the election, the Clinton campaign accused
WikiLeaks
of being “nothing but a propaganda arm of the Kremlin with a political agenda
doing Putin’s dirty work to help elect Donald Trump.” Welp.
These
leaks seemed to further the narrative that Clinton was untrustworthy,
disingenuous, unfairly favored, and allowed to play by a different set of
rules. They also fueled the heat she took for separate issues, like classified
emails on her private server or questions about the Clinton Foundation, which only
added to the sense that she wasn’t being straight with the American people.
This perception of her contributed to strikingly high unfavorability ratings
and helps explain why nearly half of registered voters who supported Trump
proclaimed that they were actually voting against Clinton.
Then there
was the fake news. These fabricated stories ranged from purported admissions
that Clinton was paying people $3,500 to protest at Trump rallies to a supposed
declaration by the pope that he supported Donald Trump. These stories
questioned Clinton’s health, reported a murder-suicide of an FBI agent involved
in the Clinton email leaks, and placed a Trump-Pence campaign sign in the yard
of FBI Director James Comey.
Reporting
has shown that Russian propaganda is likely behind the intentional spread of such
stories,
even when it wasn’t the originator. These stories showed up at the top of
search engine results and were shared on social media sites, which have
increasingly become echo chambers for our personal politics. Trump campaign
officials amplified some of these stories on social media, and even traditional
media outlets were fooled on occasion. Analysis since the election has shown
that fake news stories
outperformed real news by the end of the campaign, and most Americans, but
especially Trump voters, tended to believe the fake stories to be true.
Russia set
out to intentionally manipulate the information that voters consumed in order
to influence the decisions they made on Election Day. The goal wasn’t to change
the minds of the entire populace, but seed just enough doubt in the minds of
undecided and tentatively committed voters to improve Trump’s chances. Just
like the phishing email that appears to be an update on the status of the
Christmas gifts you ordered or warning that there’s a problem with your tax
return, disinformation only has to deceive a very small percentage of the right
people to be successful.
And we
aren’t the only targets. Russia has used fake news to influence discussions
concerning Sweden forming a
military partnership with NATO, coupled propaganda with cyberattacks on
Ukraine’s power grid, and is presently spreading disinformation
in Germany to
influence its politics. As the Institute for the Study of War astutely put it,
Russia
uses information warfare to “take advantage of pre-existing dispositions among
its enemies to choose its preferred courses of action.”
We will
never know if Russia’s prolonged hackathon of American citizens definitively
changed the outcome of the election. But what is certain is that the ballots
cast by Americans—not Russian malware—gave Trump enough electoral votes to win
the election. And voters did not make those choices in a vacuum. The media
coverage of the doxxed DNC emails and the proliferation of fake news stories
changed the information we considered when making our electoral choices.
That is the
art of information warfare. It is misdirection. We were all on alert for how
Russia could hack election systems. And while we reeled in that red herring,
Russia phished the voting public.
This article was originally published in Future Tense, a collaboration among Arizona State University, New America, and Slate.