The Technology That Matters
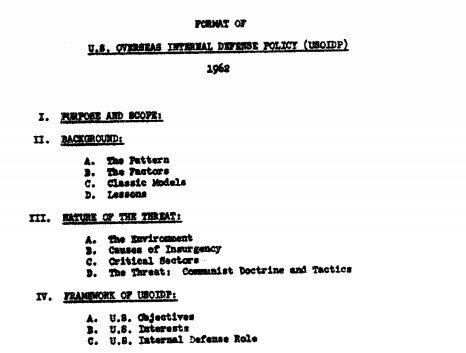
When modern U.S. counterinsurgency strategy was first codified in 1962 under the idea of “Overseas Internal Defense Policy,”1 it was typed out on a machine that had no digital components. Computers were just used as massive calculators for a small number of government agencies and businesses. Personal communications devices were little-changed versions of the telephone developed by Alexander Graham Bell almost a century earlier—hard wired into your office or home. The internet wouldn’t even be conceived for another year (in a memo written by J.C.R. Licklider and Robert W. Taylor, who first described it as the “Intergalactic Computer Network”),2 while the first mobile telephone wouldn’t be invented until 1973 (and even then, the three-pound Motorola monstrosity wouldn’t go on sale for another decade, for the modest price, in today’s dollars, of $10,000).3 As we see in everything from the fictional training at Dara Lam to ISIS’s all too real rise and recruiting through its deft use of social media, these technologies have since proven crucial to the story of modern insurgency.4
Central Intelligence Agency
In weighing the potential impact of technology on insurgency moving forward, we should similarly seek to identify the technologies that will truly matter in a manner like the computer and its networking. That is, our focus should not be on mere evolutionary improvements, such as a gun that shoots a bit faster or a missile that goes slightly further, but the technologies that truly change the game. These go by various catchphrases. A generation ago in the Pentagon, “revolutionary” was the popular term.5 Today, the buzzword is “disruptive.” Ironically, outside the military, the descriptor is “killer app.” Whatever the term, think of these next important technologies as akin to the steam engine in 1820s or the airplane in 1920s or the computer in 1980s. They are real, and will change the world, but haven’t yet.
There is an important warning, however. What make them revolutionary, is not the mistaken belief they somehow magically will solve all our problems or lift the fog of war.6 Thinking like that is exactly what can lead one to absurd optimism and terrible errors, especially about war and insurgency.7
Rather, it is the opposite. What truly defines the revolutionary game-changers is that they are technologies that present new questions, for which we don’t have the answers to. These are questions of two types: First, they introduce issues of “What is possible that wasn’t possible just a generation before?” And, secondly, they raise new issues of “What is proper, in issues of right and wrong, that we weren’t wrestling with before?” These may be new questions of the proper way to recruit, organize, or train. Or, they might be new issues of law and ethics that were recently the stuff of science fiction.
A few years back, I helped develop a project for the Pentagon called NeXTech,8 where we conducted research to answer just what were the pending technologies that might have this effect? That is, what were the technologies of today that were in that potential parallel position to the computer in 1980?
We interviewed a diverse set of subject matter experts, who ranged from people working at places like DARPA and ONR, to university research labs, to experts in industry, ranging from defense contractors to Silicon Valley firms like Apple, Google, and Facebook. They helped us identify that the looming change was not about any single one technology, but rather a cluster of new technology areas. From the hardware of robotics to the wetware of human performance enhancements, these technology clusters are poised to change the landscape of both what is viewed as possible and proper, including for war and insurgency.
Hardware
In our lifetime, robots, arguably the most celebrated of science fiction technologies, have finally become reality. The U.S. military force that went into Afghanistan after the 2001 attacks used zero robotic systems; now the force has over 22,000 in its inventory, while civilian drones are being used everywhere from agriculture to real estate.9
Moving forward, we will see even more automation. Increasingly autonomous robotics will come in two primary forms, each of which mimics intelligence in nature. The first are where the intelligence is centralized, such that the task is done directly. In robotics, these tend to be large-scale systems that mimic or directly replace human tasks, such as driverless cars, planes, etc. And then there are systems where the intelligence and resulting tasks are decentralized. They work via networks, akin to insects, allowing the tasks to be disaggregated into parts, but also operating via “swarms” in mass scale.10
The changes brought on by both types will be incredibly disruptive to both war and work. An Oxford University examination of 702 different jobs found that 47 percent of total U.S. employment is at risk for replacement or reduction by automation within our lifetime.11 It will hit developing world economies, which support often fragile politics, even harder. As just one illustration, according to International Labour Organization estimates, over 137 million salaried workers in just the five states of Cambodia, Indonesia, the Philippines, Thailand, and Vietnam are “at high risk of being replaced by machines.”12

KUKA Roboter GmbH, courtesy of Wikimedia Commons
This points to an important impact of a true technology change: It affects society on multiple levels and issue areas. Relevant to robotics, we should thus expect a double effect. Technology that simulates and replaces humans will alter not just the various roles that humans play in insurgency, but will maybe even spark the kind of anger and unrest that festers into it.13
Software
There are also major changes in what runs and connects our technology, software, and internet it is now bound within. The rise of the “network of networks” has so shaped insurgency that a group like ISIS is literally a creature of the modern internet,14 both recruiting through it and operating on it.
Yet, the internet itself is changing as it moves into its second half-century of life, and not just by bringing the second half of the world’s population online (importantly in many of the areas most fragile and susceptible to mass violence). The internet is shifting from being about communications between human beings (already disruptive enough to everything from our wars to our economy to our dating lives) to running the systems of our increasingly digital world. Roughly 10 billion devices are online now. In the next five years, the number of networked devices is estimated to reach 64 billion, reflecting over $3 trillion in annual spending.15 But most of these new contact points will shift from being computers on our desks and smart phones in our pockets to “things” like cars, thermostats, power plants, etc.
This massive growth won’t just empower the internet economy to new spaces, but also massively grow the attack surface—the potential points of vulnerability that cyber threats will go after. However, it will also be a bit like traveling back in time, in that the new growth in the “Internet of Things” (IoT) is replicating all the old cyber security problems. With responsibilities for security unclear, and almost no regulation or even basic liability, all too often these devices lack even basic security features, while customers are largely unaware of what they can and should do. The result is that up to 70 percent of IoT devices have known vulnerabilities,16 and they have already become a key part of botnets.17
The shift to the things connecting and run by the internet will play out simultaneous to another core shift: How the sharing of files, records, and knowledge on it works. This emergent wave is of distributed ledgers using blockchain and other such technologies. Already, its impact has been felt in areas like finance, where cryptocurrencies like bitcoin have created a new form of money and the transfer of value. Yet, the model of peer-to-peer distribution may lead to even greater change as it is applied across fields and into recordkeeping. It may even lead to a fundamental reorder of the web, as Chris Meserole and Alina Polyakova put it in Foreign Policy magazine, “outside the control of major corporations and states,”18 thus empowering weaker and nonstate actors. Or, like in other spaces of the web, it may prove to be another means for authoritarian states to exert control, such as through China’s recent efforts targeting blockchain developers.19 The very fact that both are in the potential future illustrates the shift at hand.
Yet, the shift in the internet itself might be minuscule in its impact compared to what is about to play out in the intelligence of the software that runs through all of it. In Chinese military thinking, the significance is described as the shift in societies—and their wars—from industrialization of the last century to informatization of the turn of this century to a looming “intelligentization.”20

Wikimedia Commons
The field of “Artificial Intelligence” encompasses work on everything from machine learning to neural networks. Arguably no other technology area is seeing as much energy and investment. At this time, there is roughly $153 billion in spending in this space, “with an estimated annual creative disruption impact of $14-33 Trillion.”21 Its participants include all the leading governments of the world, who are engaged in what is increasingly referred to as an “AI arms race.”
This arms race, though, is unlike those in the past in that its participants go beyond competing nations. AI is the focus of a massive scale of industrial spending, poised to hit $79.2 billion by 2022 at a compound annual growth rate of 38 percent.22 Its participants include not just tech firms, but also more traditional business corporations looking to survive the next generation. For example, both John Deere and McDonalds have each respectively spent over $300 million buying AI startups to weave into their business.23
Indeed, of companies listed on the stock market, 244 list AI24 as a centerpiece of their future business plans (a figure gathered by an algorithm sifting through earnings calls). This field is also the obsession of the majority of new entrants to the marketplace, who hope to make the next great fortunes. The founder of Wired magazine described today’s boom in Silicon Valley start-up companies, who will shape tomorrow, as follows: “AI is already here, it’s real, it’s quickening … I think the formula for the next 10,000 start-ups is to take something that already exists and add AI to it.”25
As thought leaders and business luminaries from around the world wrestle with how important this development will be, it seems as if they cannot overstate its significance. Masayoshi Son, the founder of the mega-conglomerate Softbank, frames it this way:
"Every industry that mankind created will be redefined. The medical industry, automobile industry, the information industry of course. Every industry that mankind ever defined and created, even agriculture, will be redefined. Because the tools that we created were inferior to mankind's brain in the past. Now the tools become smarter than mankind ourselves. The definition of whatever the industry, will be redefined."26
Baratunde Thurston, a Director’s Fellow at MIT’s Media Lab, thinks even this massive claim is actually an understatement, in that it just focuses on business: “Every area of life will be affected. Every. Single. One.”27 Insurgency, of course, falls within this categorization.
Wetware
Yet there is another historic change afoot in technology. Software and Hardware are technology that we use. “Wetware,” or, more technically, “human performance modification,” is about using technology to change us. Think of this as akin to the science fiction of Iron Man and Captain America crossed with the Russian Olympic athlete program.
We are seeing revolutions in a field that extends from medicine to synthetic biology—a new field that encompasses revolutions ranging from genome editing like CRISPR to biologic computers.28 In this space, discoveries and breakthroughs are outpacing the IT field standard of “Moore’s Law.” They are rewriting what has been possible or not in the literal history of our species, altering everything from susceptibility to disease to body endurance to the workings of the brain itself.29
In turn, new technologies in brain machine interface will rewrite the entire history of how humans have connected to their tools.
In turn, new technologies in brain machine interface will rewrite the entire history of how humans have connected to their tools. From the first stone to the drone and iPhone, we have used our monkey fingers. This is already being challenged by technologies that have allowed test subjects to thought-control advanced technologies like aircrafts30 to conduct database queries and process product orders without ever writing or vocalizing it, which is known as “telepathy tech.”31
Synergy
There are a variety of other technology areas that could bode to be as disruptive as the above three. For instance, we are seeing both new forms of energy generation and storage come onto line or become distributed in new ways. These could shift everything from geopolitics (how much we care about insurgencies is often determined by their proximity to key energy resources that we’ve become dependent on due to technology changes) to battlefield logistics. They could redefine the roles and purpose of already revolutionary systems. For instance, an autonomous drone is game-changing enough as a plane; an autonomous drone that uses a mix of solar and hydrogen to stay in the air for 12 months32 perhaps ought to be understood as something else, as it now has attributes more like a space satellite than a plane.
Indeed, the fact that so many of these new technologies cross and shape each other is maybe what is the most exciting and game-changing of their prospects (in military terms, the parallel would be how the German blitzkrieg derived from the operational blending together of tanks, planes, and radio). For example, Direct Digital Manufacturing, popularly known as “3D printing,” turns a bit, a computer design, into an atom, a created thing. It is a story of both hardware and software. It also holds the promise of potentially altering fundamental business models. It could do to defense firms what the iPod did to the music industry, absolutely changing not just profit margins, but profit model itself, as anyone can make their own systems and spare parts. 3D printing’s rise, as a result, also means that major aspects of sanction regimes or weapon embargos might become outdated. Indeed, in a nation where gun sales are effectively banned, British police have already had to deal with 3D printed guns,33 while ISIS used fairly advanced injection molding techniques in making its own drones.
Citations
- “Format of U.S. Overseas Internal Defense Policy (USOIDP)” (CIA, January 1, 1962), source.
- J.C.R. Licklider, “Licklider Describes the ‘Intergalatic Computer Network,’” April 25, 1963, source.
- “From Brick to Slick: A history of Mobile Phones,” Wired, March 20019. source
- P. W. Singer and Emerson T. Brooking, “Terror on Twitter,” Popular Science, December 11, 2015, source.
- Donald Rumsfeld, “Transforming the Military,” Foreign Affairs, June 2002, source.
- Arthur K. Cebrowski and John H. Garstka, “Network-Centric Warfare – Its Origin and Future,” Proceedings 124, no. 1/1,139 (January 1998), source.
- Judd Legum, “Rumsfeld Lies About Pre-War Predictions: ‘You Can Take That To The Bank,’” ThinkProgress, December 9, 2005, source.
- Patrick Lin, “Pain Rays and Robot Swarms: The Radical New War Games the DOD Plays,” The Atlantic, April 15, 2013, source.
- P.W. Singer, Wired for War (HMH, 2009); April Glaser and Rani Molla, “The Number of Robots Sold in the U.S. Will Jump Nearly 300 Percent in Nine Years,” ReCode, April 3, 2017, source.
- Oriana Pawlyk, “Pentagon Still Questioning How Smart to Make Its Drone Swarms,” Military.Com, February 7, 2019.
- Henry Conrad, “Here’s What Jobs Robots Will Be Taking over in the near Future,” ZME Science, September 15, 2015, source.
- Molly Kinder, “Learning to Work WIth Robots,” Foreign Policy, July 11, 2018, source.
- Steve LeVine, “Robots May Have given Trump an Edge in 2016,” Axios, July 8, 2018, source.
- Abdel Bari Atwan, Islamic State: The Digital Caliphate (Oakland, California: University of California Press, 2015).
- Peter Newman, “IoT Report: How Internet of Things technology growth is reaching mainstream companies and consumers,” Business Insider, Jan. 28, 2019source
- Bradley Boughton, “2017 Cyber Security Threats, Predictions, Funding & Trends,” Glocomms, February 22, 2017, source.
- Michelle Drolet, “Botnets: Is Your Network Really Protected?,” CSO, March 13, 2017, source.
- Chris Meserole and Alina Polyakova, “Disinformation Wars,” Foreign Policy, May 25, 2018, source.
- David Canellis, “China Is Forcing Blockchain Devs to Dox Users, Censor Content,” TNW, January 10, 2019, source.
- Elsa B. Kania, “数字化 – 网络化 – 智能化: China’s Quest for an AI Revolution in Warfare,” The Strategy Bridge, June 8, 2017, source.
- “Artificial Intelligence (AI) Trends,” Mad Scientist Laboratory, December 14, 2017, source.
- John McCormick, “Worldwide AI Spending to Hit $35.8 Billion in 2019,” Wall Street Journal, March 13, 2019, source.
- Brian Barrett, “McDonalds bites on Big Data with $300 million acquisition,” Wired, March 25, 2019, source; James Vincent, “John Deere is buying an AI startup to help teach its tractors how to farm,” The Verge, September 7, 2017, source; Deere and Company, “Deere to Advance Machine Learning Capabilities in Acquisition of Blue River Technology,” PR Newswire, September 6, 2017, source.
- Michael McDonough, Twitter, February 28, 2017, source.
- Jonathan Merritt, “Is AI a Threat to Christianity,” The Atlantic, February 3, 2017, source.
- Amie Tsang and Michael J. de la Merced, “Morning Agenda: Masayoshi Son Warns of the Singularity,” New York Times, September 20, 2017, source.
- Lee Rainie and Janna Anderson, “Code-Dependent: Pros and Cons of the Algorithm Age” (Pew Research Center, February 8, 2017), source.
- Feng Zhang, “Questions and Answers about CRISPR,” Broad Institute, source.
- Antonio Regalado, “China’s CRISPR Twins Might Have Had Their Brains Inadvertently Enhanced,” MIT Technology Review, February 21, 2019, source.
- Luke Dormehl, “This Scientist Can Control a Swarm of Drones with His Thoughts,” Digital Trends, July 15, 2016, source.
- Philip Perry, “New MIT Device Can Read Your ‘inside Voice’, Marking the Dawn of Telepathy Tech,” BIg Think, April 11, 2018, source.
- Rhiannon Williams, “Solar-Powered Drone Is Capable of Flying for up to a Year at a Time,” I News, May 4, 2018, source.
- Martin Evans, “‘3D Printed Gun’ Discovered by Police,” The Telegraph, October 25, 2013, source.
