GovSCH: An Open-Source Schema for Authoring Cybersecurity and AI Governance Documents
Abstract
The increasing complexity of cybersecurity and artificial intelligence (AI) executive orders, frameworks, and policies has made translating high-level directives into actionable implementation a persistent challenge. Policymakers, framework authors, and engineering teams often lack a unified approach for interpreting and operationalizing these documents, resulting in inefficiencies, misalignment, and delayed compliance. While existing standards such as the Open Security Controls Assessment Language (OSCAL) address control-level specifications, no standardized, machine-readable format exists for authoring and structuring high-level governance documents. This gap hinders collaboration across disciplines and obscures critical directives’ underlying intent and rationale.
This report introduces Governance Schema (GovSCH), an open-source schema designed to standardize the authoring and translation of cybersecurity and AI governance documents into a consistent, machine-readable format. By analyzing prior executive orders, regulatory frameworks, and policies, GovSCH identifies common structures and authoring practices to create an interoperable model that bridges policymakers, regulatory framework authors, and engineering teams. This approach enables more precise articulation of policy intent, improves transparency, and accelerates the technical implementation of regulations. Ultimately, GovSCH aims to enhance collaboration, standardization, and efficiency in cybersecurity and AI governance. To explore the schema structure, documentation, and examples, please visit the project’s GitHub repository: newamerica/GovSCH.
Acknowledgments
Special thanks to Christina Morillo, Lauren Zabierek, Camille Stewart Gloster, Peter W. Singer, Bridget Chan, Olatunji Osunji, the 2025 #ShareTheMicInCyber cohort, and the New America teams whose guidance, feedback, and sponsorship made this work possible.
Editorial disclosure: The views expressed in this report are solely those of the author and do not reflect the views of New America, its staff, fellows, funders, or board of directors.
Downloads
Scope
This report documents the application of Governance Schema (GovSCH), an open-source, machine-readable schema for authoring and translating cybersecurity and artificial intelligence (AI) governance documents, as a valuable resource for compliance officers, regulators, engineering teams, and tech policymakers. It applies three distinct schemas, one each for (1) executive orders, (2) frameworks, and (3) regulations.
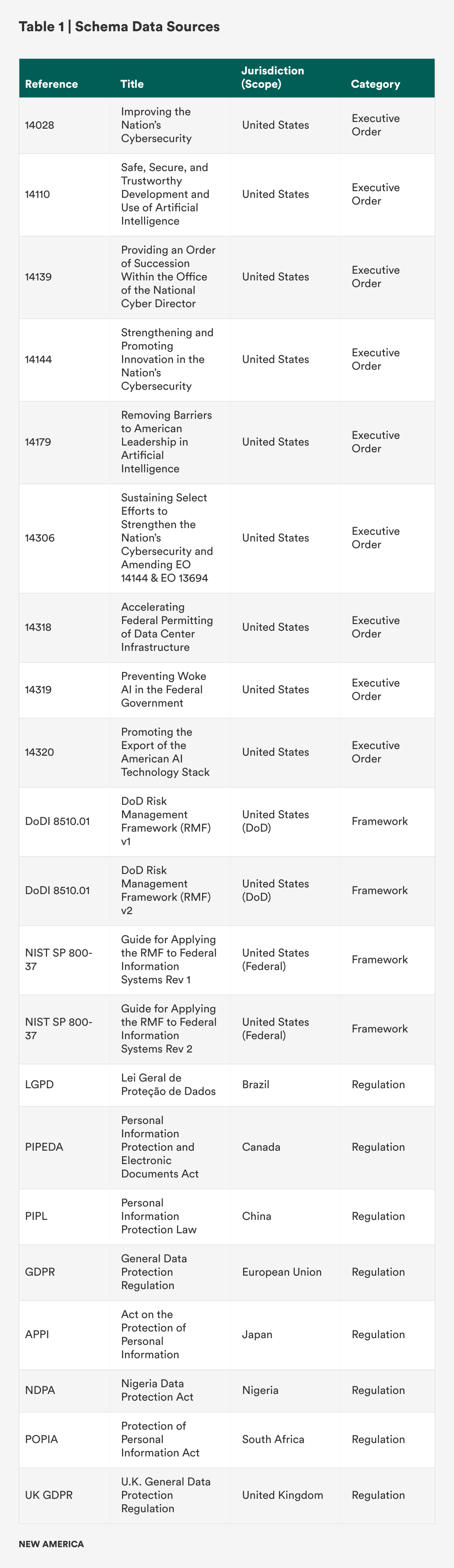
These sources (presented in Table 1 below) were deliberately selected because they collectively represent governance instruments that are high-impact—based on the scope of their coverage at national and sector levels—and shape cybersecurity, AI, and privacy policy globally. The U.S. executive orders were chosen due to their role in setting national priorities for cybersecurity and AI governance and their explicit emphasis on machine-readable policy development. The National Institute of Standards and Technology (NIST) and Department of Defense (DoD) risk management frameworks were included for their structured approach to system-level cybersecurity governance and widespread use in federal and defense contexts. The international privacy and data protection regulations, spanning jurisdictions in the Americas, Europe, Africa, and Asia, were chosen for their regulatory diversity and global influence, ensuring that the schema reflects a broad range of legal and cultural approaches to governance. Together, these instruments provide a representative sample for demonstrating the three GovSCH schemas: a U.S.-focused schema for executive orders, a U.S.-focused schema for frameworks, and an internationally focused schema for regulations.
Limitations
This report adopts a focused scope to ensure depth and manageability. It does not include all cybersecurity, AI, or data governance documents. Regulations, frameworks, or executive directives outside the abovementioned instruments are excluded from analysis. Furthermore:
- The schema is not a compliance tool and does not provide legal advice or substitute for regulatory interpretation. Instead, it is a structural model for documenting and translating governance documents.
- The analysis prioritizes structural application of GovSCH rather than detailed interpretative analysis of each instrument’s substantive legal or policy content.
- While several regulations included are international in scope, the schema design remains primarily influenced by U.S. executive orders and NIST frameworks, which may shape its orientation.
- Validation of GovSCH through live implementation or formal standardization processes is outside the scope of this report and is identified as an area for future research and collaboration.
These boundaries intentionally focus on the primary objective: documenting and demonstrating the use of three GovSCH schemas in translating diverse governance instruments into a consistent, machine-readable format, with schema documentation and examples available on the project’s GitHub repository.
Introduction
In the evolving landscape of cybersecurity and artificial intelligence (AI), executive orders, regulatory frameworks, and governance policies are proliferating and escalating in complexity. Despite their critical role in shaping national and organizational risk posture, these directives remain almost universally authored in natural-language formats, making them difficult to translate into actionable workflows for engineering teams and limiting automation in compliance systems. Governance Schema (GovSCH) is designed to address this disconnect by introducing a standardized, machine-readable schema for authoring cyber and AI governance documents.
Fragmented Policy and Manual Compliance
The United States has issued multiple major executive orders to guide cybersecurity and AI governance. For example, Executive Order (EO) 14028 set forth secure software development requirements and evidence-based compliance artifacts; EO 14144 extended the focus into AI, quantum-resistant cryptography, and the launch of rules‑as‑code pilots.1 A further amendment in EO 14306 reiterated the government’s intent to adopt rules‑as‑code, requiring agencies to publish machine-readable versions of policy guidance by mid‑2026.2 However, despite these initiatives, most executive orders and frameworks still rely on prose, making systematic automation and interpretation difficult.
This creates a triad of challenges, such as:
- Misalignment and ambiguity: Engineering teams often struggle to derive technical requirements from narrative policy documents, which delays implementation and increases risk.3
- Manual translation burden: Compliance functions frequently engage in labor-intensive interpretation to translate policies into technical artifacts and control mappings.4
- Fragmented development: Without a consistent structure across documents, frameworks authored by the National Institute of Standards and Technology (NIST), Office of Management and Budget (OMB), Cybersecurity and Infrastructure Security Agency (CISA), and others are often incompatible or duplicative.5
Government and industry have recognized policy-as-code as an essential compliance imperative; organizations that fail to adopt early will face higher costs and reduced reliability.6 For instance, Australia’s adoption of rules-as-code has shown transformative efficiency gains (such as greater transparency, version control, and auditability) in compliance and legislative interpretation.7
Case for GovSCH
GovSCH introduces a community-founded, open-source JSON (JavaScript Object Notation) schema for authoring cyber and AI governance documents. It defines key structural elements, governance intent, policy objectives, dependencies, actors, timelines, controls, and rationale in a consistent machine-readable format, and it achieves the following:
- Bridges policy and engineering: GovSCH enables frameworks and engineering teams to “read” policy directly by encoding high-level intent in structured data, similar to how Open Security Controls Assessment Language (OSCAL) encodes control-level guidance.8
- Supports rules-as-code pilots: As agencies like NIST and CISA begin to pilot rules-as-code implementations, GovSCH offers a production-ready schema that aligns with those mandates and accelerates adoption.9
- Promotes transparency and reuse: Policy authors can reuse, extend, and version GovSCH-compliant documents, improving comparability across jurisdictions, faster onboarding, and better traceability.
Potential for Scale and Adoption
GovSCH is built for broad scalability and ease of adoption for:
- Policy and regulatory agencies: Agencies drafting executive orders or regulations can author GovSCH-compliant documents from inception and integrate them into legislative and policy life cycles.
- Standards bodies: International standards organizations and regulatory bodies—including European Union legislative frameworks like Network and Information Security Directive (NIS2) and Digital Operational Resilience Act (DORA)—can adopt GovSCH for cross-jurisdictional coordination.
- Technology implementers: Tool vendors; open-source compliance platforms; governance, risk, and compliance (GRC) systems; and infrastructure-as-code frameworks can incorporate GovSCH as a policy input format.
- Global community and open source: As an open-source standard, GovSCH invites contributions from academia, industry, government, and standards groups to refine its structure and broaden its applicability, similar to open schema standards for AI incident reporting.
The concept mirrors recent academic proposals in AI governance, such as the unified control framework, which consolidates controls across risk scenarios and regulatory regimes into a structured taxonomy.10 Similarly, GovSCH can be a foundation for harmonizing how entities translate executive intent across diverse governance contexts.
Benefits for Different Stakeholders
Policymakers and Government Agencies
- Clarity of structure: GovSCH imposes a minimum, consistent authoring template as the baseline for policy creation to ensure machine readability, reduce ambiguities, and avoid misinterpretations in policy language.
- Efficient updates and batch mapping: Policy changes like updating compliance timelines and scope can be applied programmatically across GovSCH files.
- Interoperability: Policies authored in GovSCH can be tracked across versions and compared, thereby supporting auditability and iterative collaboration.
Framework Authors and Standards Developers
- Automated mapping: Framework authors can programmatically ingest GovSCH documents to derive mappings to controls (as seen in documents from NIST and International Organization for Standardization, or ISO, frameworks).
- Reduced duplication: By standardizing how intent is expressed, GovSCH enables the reuse of familiar patterns, improving consistency across frameworks.
- Dynamic rule creation: Standard tools can generate rules or guidance automatically from GovSCH definitions, accelerating development cycles.
Engineering Teams and Compliance Operations
- Acceleration of compliance workflows: Instead of manually deciphering policy documents, teams can feed GovSCH input into compliance-as-code pipelines, shipping faster and with fewer errors.
- Improved traceability: Each control, requirement, or objective can be traced back to high-level policy rationale encoded in GovSCH metadata.
- Scalability for transformation: Large organizations managing many policies and jurisdictions can programmatically scale compliance pipelines by applying GovSCH schemas.11
Recent academic studies on automating policy analysis using large language models (LLMs) showed efficiency gains (such as comprehensive coverage and reduced duplication) when structured inputs could be extracted from high-level documents.12 GovSCH builds on that principle at authoring time, not analysis time, enabling policy documents to be structurally analyzable from their inception.
Toward a Policy-as‑Code Standard
GovSCH provides a critical missing piece in the emerging policy-as-code and machine-readable governance ecosystem. Offering a scalable, open-source JSON schema for cyber and AI governance documents reduces friction between policymakers, standards developers, and technical implementers. In doing so, it:
- Supports rules-as-code mandates coming into force by mid‑2026;
- Provides a consistent foundation for cross-domain mapping, automation, and compliance; and
- Enables global collaboration around governance structures, control taxonomies, and regulatory frameworks.
GovSCH is a schema and potential standard promoting transparency, efficiency, and interoperability in cyber and AI governance. As agencies move toward machine-readable policies, GovSCH can be the foundational convention for policy authoring, translation, and implementation. Its open-source nature ensures it can evolve through community contributions, supporting emerging needs across industries and jurisdictions.
The value of GovSCH lies in its potential to reduce ambiguity and accelerate the operationalization of complex cybersecurity and AI policies. By offering standardized, machine-readable structures for EOs, frameworks, and regulations, GovSCH could enable policymakers, engineers, and compliance teams to work from a common source of truth.
For example, imagine a federal contractor tasked with implementing requirements from multiple overlapping EOs, each written in dense legal prose and open to interpretation. Today, engineering teams must manually extract responsibilities and timelines, often resulting in delays and inconsistent compliance. With GovSCH, those same orders could be instantly parsed into structured JSON/YAML formats, allowing automated compliance systems to flag deadlines, assign responsible entities, and map directives to technical tasks.
Citations
- Joseph R. Biden, Improving the Nation’s Cybersecurity: Executive Order 14028 (86 Federal Register 26633, May 17, 2021), source; Joseph R. Biden, Strenghening and Promoting Innovation in the Nation’s Cybersecurity: Executive Order 14144 (90 Federal Register 6755, January 17, 2025), source.
- Donald Trump, Sustaining Select Efforts to Strengthen the Nation’s Cybersecurity and Amending Executive Order 13694 and Executive Order 14144: Executive Order 14306 (90 Federal Register 24723, June 6, 2025), source.
- Mazaher Kianpour and Shahid Raza, “More than Malware: Unmasking the Hidden Risk of Cybersecurity Regulations,” International Cybersecurity Law Review 5 (February 2024): 169–212, source.
- David London, “The Latest Cybersecurity Executive Order: Implications and Guidance,” Chertoff Group, June 10, 2025, source.
- “OSCAL: Open Security Controls Assessment Language,” National Institute of Standards and Technology, updated May 8, 2025, source.
- Ibrahim Waziri, Jr., “New White House Cyber Executive Order Pushes Rules‑as‑Code,” CyberScoop, July 14, 2025, source.
- GovCMS, “Introducing Rules as Code,” Australian Government, source.
- “OSCAL: Open Security Controls Assessment Language,” source.
- Trump, Executive Order 14306, source.
- Ian W. Eisenberg, Lucía Gamboa, and Eli Sherman, “The Unified Control Framework: Establishing a Common Foundation for Enterprise AI Governance, Risk Management, and Regulatory Compliance,” arXiv, March 7, 2025, source.
- Nitisha Jain et al., “A Standardized Machine‑Readable Dataset Documentation Format for Responsible AI,” arXiv, July 1, 2024, source.
- Ian W. Eisenberg, Lucía Gamboa, and Eli Sherman, “The Unified Control Framework: Establishing a Common Foundation for Enterprise AI Governance, Risk Management, and Regulatory Compliance,” arXiv, March 7, 2025, source.
Literature Review: Ongoing Efforts
The need for standardized, machine-readable schemas for regulatory, governance, and policy documents has driven substantial innovation across academia, government, and industry. These initiatives have addressed different facets of the broader challenge of structured governance documentation, each providing insights and precedents relevant to GovSCH (see Table 2).
One foundational effort is the Akoma Ntoso standard, developed by OASIS Open and the United Nations in 2018, that provides an XML-based schema to structure legal, legislative, and judicial documents.1 Akoma Ntoso has enabled consistent markup and semantic clarity across documents such as bills, acts, and parliamentary records, supporting human readability and machine parsing. Similarly, the United Kingdom’s Legal Schema (UKLS)2 project of 2023 leverages structured markup through the Legal Schema Language to produce human-readable and machine-executable digital contracts simultaneously. Additionally, the Semantics of Business Vocabulary and Business Rules (SBVR) standard from the Object Management Group introduced controlled natural language approaches in 2019, transforming business rules into machine-interpretable logic.3 These foundational efforts establish key practices for the structured encoding of formal policy and legal content, setting essential precedents for GovSCH.
Recent literature has explored innovative ways of transforming policy intentions into actionable schemas in the AI compliance domain. AI Cards, developed in 2024, provides a structured framework for documenting AI systems following regulatory requirements like the EU AI Act, integrating human and machine-readable elements.4 Furthermore, the 2024 Compliance-as-Code 2.0 advances regulatory compliance automation by converting regulations into executable code through agentic AI systems.5 The 2023 Regulatory Knowledge Graphs leverage graph-based semantic representations to facilitate the automated interpretation and querying of regulatory documents.6 Complementing these efforts, the 2018 LexNLP presents a comprehensive natural language processing toolkit for extracting structured regulatory information as well as facilitating schema generation and policy automation.7 These initiatives underscore the potential for structured schemas to significantly enhance policy and regulatory compliance workflows, providing practical insights that inform GovSCH’s structural decisions.
Infrastructure-as-code (IaC) emerged in 2013 from early configuration‑management tools like CFEngine and evolved to declarative provisioning platforms like Terraform and AWS CloudFormation.8 IaC’s proven capabilities include enabling rapid rollback, immutable infrastructure, and consistent environment replication. Security extensions like Compliance‑as‑Code leverage policy engines such as Open Policy Agent to scan infrastructure manifests against rules. These successes all set the precedent for policy-as-code.
NIST’s OSCAL provides layered JSON and XML models, including Catalog, Profile, and Component for System Security Plan (SSP); Security Assessment Plan (SAP); Security Assessment Report (SAR); and Plan of Actions and Milestones (POA&M), to streamline control assessments.9 Studies report a 30-percent reduction in FedRAMP package preparation time when OSCAL is adopted; however, OSCAL still defers to external policy documents for provenance and the creation of a traceability gap.10
Further supporting governance documentation standardization, several metadata-focused initiatives exist. The National Information Exchange Model (NIEM) and NIEMOpen initiatives offer a common vocabulary and interoperable schemas for structured data exchange across government agencies.11 Similarly, the not-for-profit organization MITRE developed governance metadata standards to structure policy documents and consent forms in health and research governance. Additionally, the “Legislative Recipe: Syntax for Machine-Readable Legislation” provides a formalized approach for translating natural language legislation into semantic logic models, enhancing legislative clarity and enforceability.12 These efforts offer robust examples of governance document structuring, demonstrating methodologies that GovSCH can integrate or adapt.
Cross-domain applications of metadata schema further illustrate versatile approaches to schema design and interoperability. For example, researcher Elena Makisha explored translating construction regulations into machine-readable formats to automate compliance verification in building information modeling.13 These diverse implementations highlight schema interoperability and automation, principles central to GovSCH’s approach.
In the cybersecurity-specific domain, although not explicitly targeted at policy documents, the Open Cybersecurity Schema Framework (OCSF) has successfully developed a standardized schema for cybersecurity telemetry and event data, showing how community-driven schemas can achieve widespread adoption.14 OCSF is a practical example of schema openness, standardization, and industry-wide collaboration, which are attributes GovSCH aims to embody.
These initiatives highlight diverse ongoing efforts and provide context for understanding GovSCH’s unique position: synthesizing these varied methodologies into comprehensive schemas tailored to executive orders, structured frameworks, and international regulations.
Citations
- Monica Palmirani, Roger Sperberg, Grant Vergottini, and Fabio Vitali, eds., Akoma Ntoso Version 1.0 Part 1: XML Vocabulary (OASIS Open, 2018), source; Fabio Vitali, Monica Palmirani, Roger Sperberg, and Véronique Parisse, eds., Akoma Ntoso Version 1.0. Part 2: Specifications (OASIS Open, 2018), source.
- Peter Hunn, ed., et al., A Structured Data Format for Digital Contracts in the UK: Legal Schema (LawTech UK, 2023), source.
- Semantics of Business Vocabulary and Business Rules, Version 1.5 (Object Management Group, 2019), source.
- Delaram Golpayegani et al., “AI Cards: Towards an Applied Framework for Machine‑Readable AI and Risk Documentation Inspired by the EU AI Act,” arXiv, June 26, 2024, source.
- Aman Sardana, Swaminathan Sethuraman, and Priya Dharshini Kalyanasundaram, “Compliance‑as‑Code 2.0: Orchestrating Regulatory Operations with Agentic AI,” Artificial Intelligence General Science 5, no. 1 (2024): 546–563, source.
- Vladimir Ershov, “A Case Study for Compliance as Code with Graphs and Language Models: Public Release of the Regulatory Knowledge Graph,” arXiv, February 3, 2023, source.
- Michael J. Bommarito II, Daniel Martin Katz, and Eric M. Detterman, “LexNLP: Natural Language Processing and Information Extraction for Legal and Regulatory Texts,” arXiv, June 10, 2018, source.
- Waldemar Hummer, Florian Rosenberg, Fábio Oliveira, and Tamar Eilam, “Testing Idempotence for Infrastructure as Code,” Lecture Notes in Computer Science 8275 (2013), source
- “OSCAL: Open Security Controls Assessment Language,” source
- “The Challenges OSCAL NOW Addresses and Solves,” Pathways Consulting Group, April 9, 2024, source.
- NIEM Metamodel and Common Model Format (NIEMOpen, 2024), source.
- Megan Ma and Bryan Wilson, “The Legislative Recipe: Syntax for Machine‑Readable Legislation,” arXiv, August 19, 2021, source.
- Elena Makisha, “Features of Regulation Document Translation into a Machine‑Readable Format within the Verification of Building Information Models,” CivilEng 4, no. 2 (2023): 373–390, source.
- “Categories,” Open Cybersecurity Schema Framework, source.
Methodology: Building GovSCH
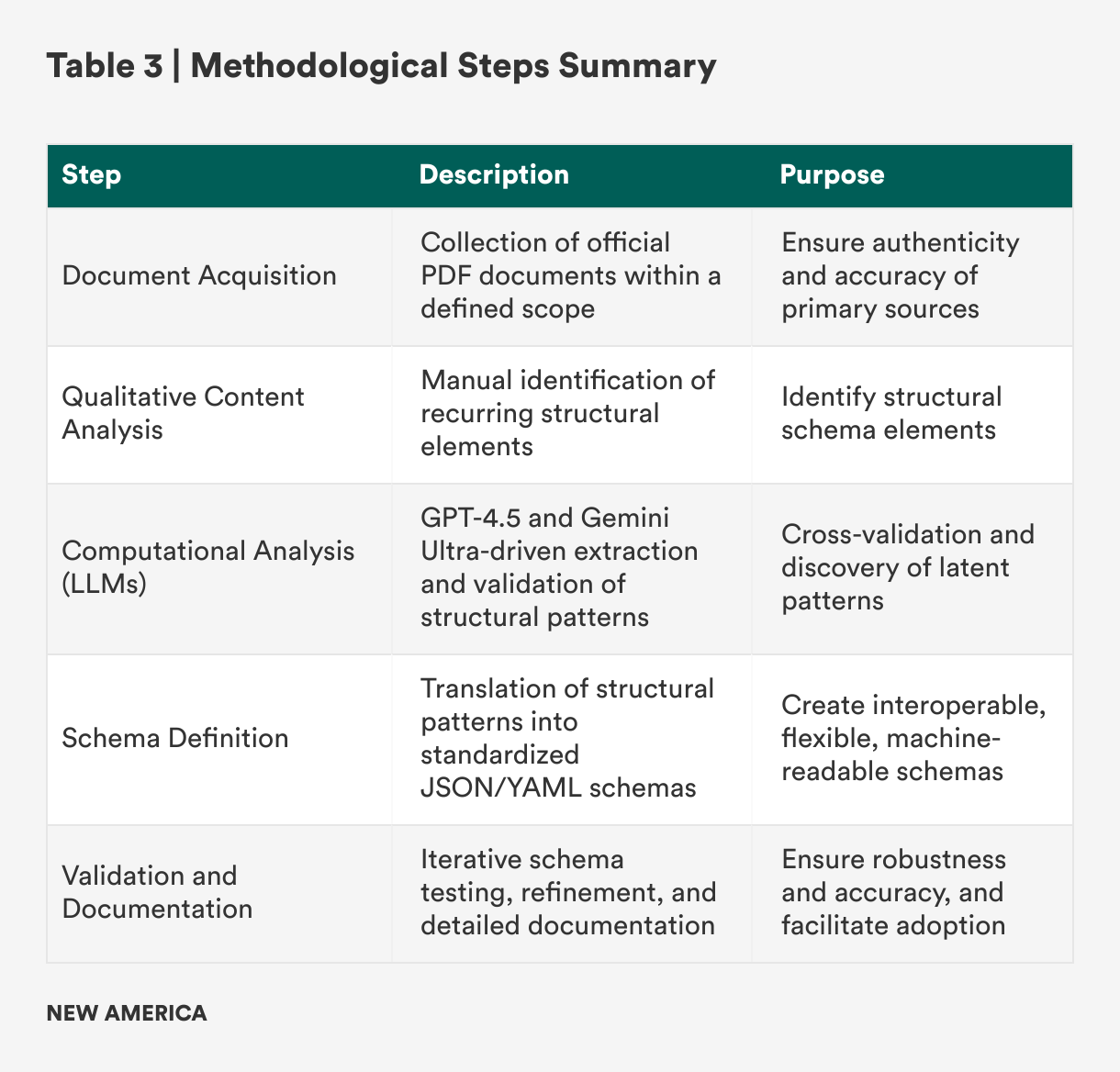
This section outlines the methodological approach taken to develop and document the three distinct GovSCH schemas, one each for (1) U.S. executive orders, (2) U.S.-centric cybersecurity frameworks, and (3) international data protection regulations. The methodology was executed through a systematic, structured process (see Table 3) involving document acquisition, qualitative content analysis, computational analysis via LLMs, and subsequent transformation into structured, machine-readable formats (JSON and YAML).
Document Acquisition
The first stage involved systematically acquiring authoritative source documents within the scope defined in the “Scope” and “Limitations” sections of this report. Official PDF documents for each governance instrument, U.S. executive orders, cybersecurity frameworks from NIST and DoD, and international regulatory frameworks were downloaded directly from official governmental, regulatory, and standards-issuing websites. This ensured the authenticity and integrity of the sources analyzed. The documents collected are listed in the scope section.
Qualitative Content Review and Analysis
Following the acquisition, each PDF document underwent an in-depth qualitative content analysis. The review involved reading, annotating, and systematically identifying structural elements common across each document type. Structural analysis focused primarily on identifying patterns. Recurring structural and semantic patterns were documented, with divergences noted to inform schema flexibility and adaptability.
Computational Analysis with LLMs
Complementing manual review, computational analysis using GPT-4.5 and Gemini-Ultra large language models systematically extracted, summarized, and validated structural components across documentation. LLM-assisted analysis served to:
- Confirm human-identified structural elements;
- Reveal additional latent patterns not immediately apparent;
- Validate semantic consistency across policy, framework, and regulatory domains; and
- Generate summaries and comparative analyses to streamline schema definition.
LLM-assisted analysis provided rigorous cross-validation, enhancing analytical accuracy, scalability, and consistency.
Schema Definition and Transformation
With structural patterns identified and validated, a standardized schema was developed for each document category: (1) executive orders, (2) frameworks, and (3) regulations. The schema design prioritized clarity, flexibility, and interoperability.
Key considerations during schema definition included:
- Standardization of structure: uniform schema elements across all three areas
- Flexibility for diversity: optional and extendable schema components
- Machine-readability: JSON and YAML formats for usability
- Semantic clarity: meaningful naming conventions and metadata definitions
Schemas underwent iterative validation (using the JSONlint and YAMLlint code quality validators) to ensure both formats can be machine-parsed, which is consistent with other JSON and YAML schemas (such as OSCAL) used by compliance automation systems.
Validation and Documentation
Schemas underwent systematic testing using representative documents. Adjustments ensured robustness, adaptability, and fidelity. Comprehensive documentation detailing schema elements, example usage, and implementation guidelines was developed and published on the project’s GitHub repository along with the complete machine-readable schema structures, supporting documentation, and illustrative examples.
GovSCH Schema Descriptions (Computed Structural Patterns)
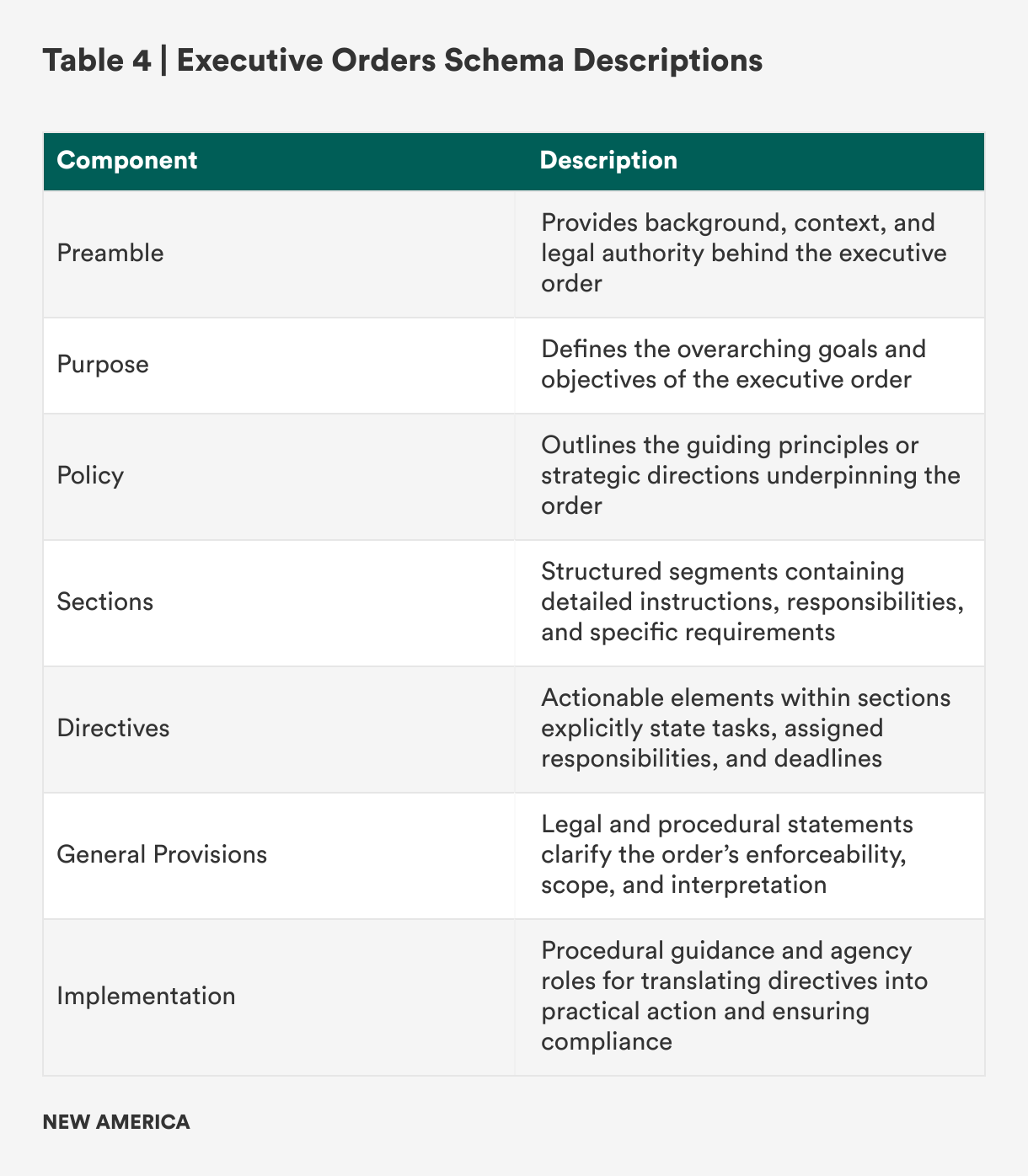
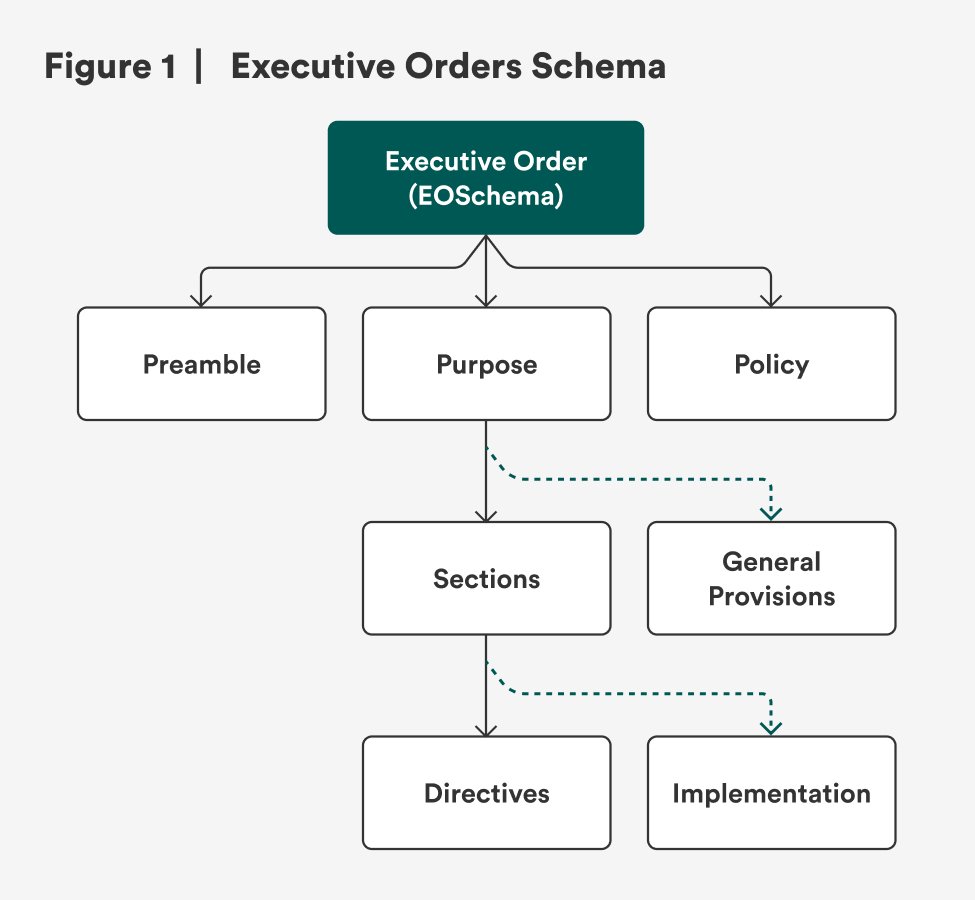
Executive Orders Schema
The “Executive Orders Schema” within GovSCH provides a standardized, machine-readable structure for capturing the essential elements of U.S. presidential executive orders. Its design reflects the consistent components observed across multiple orders while ensuring flexibility for varying formats and content (see Figure 1 and Table 4).
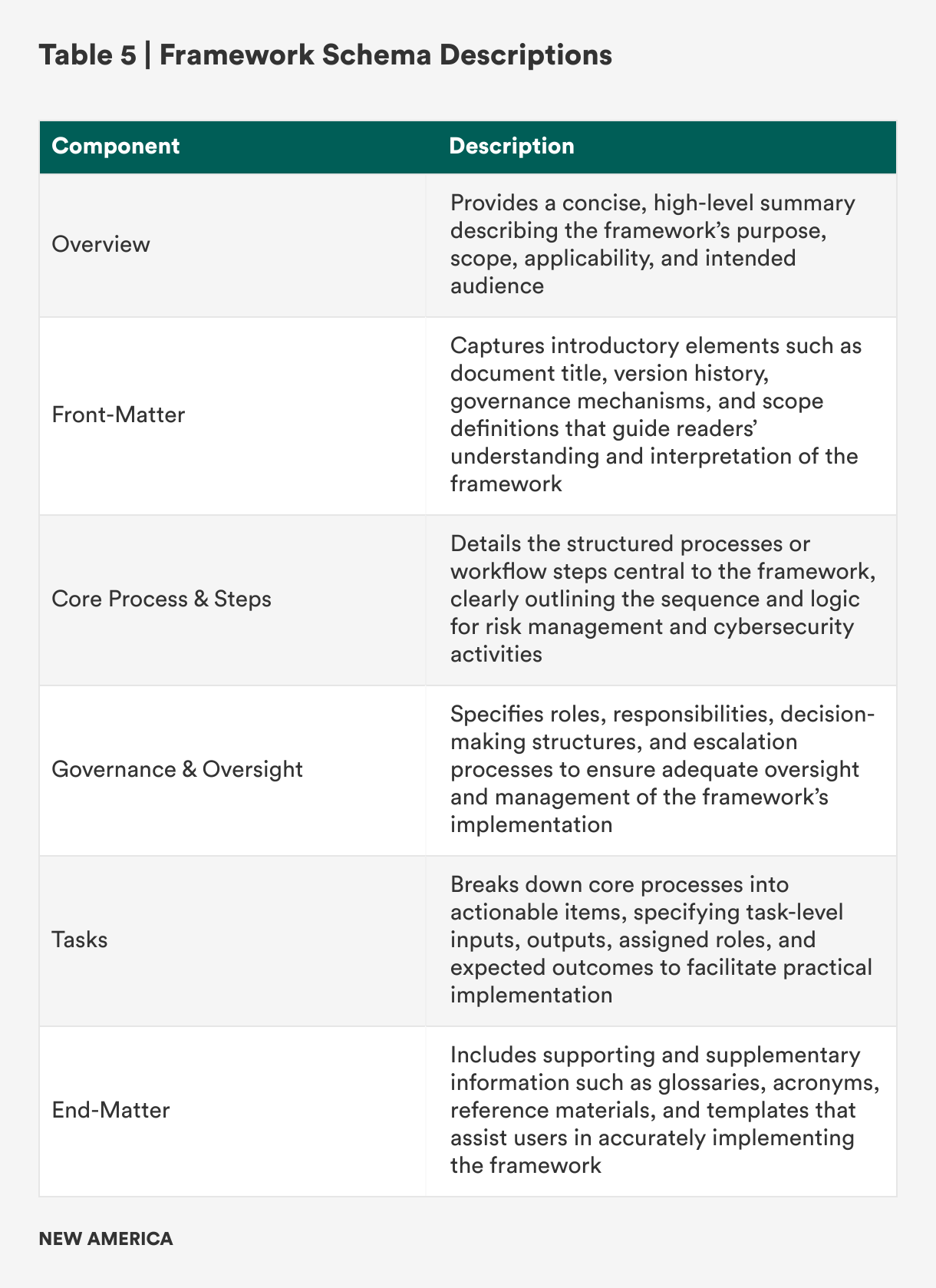
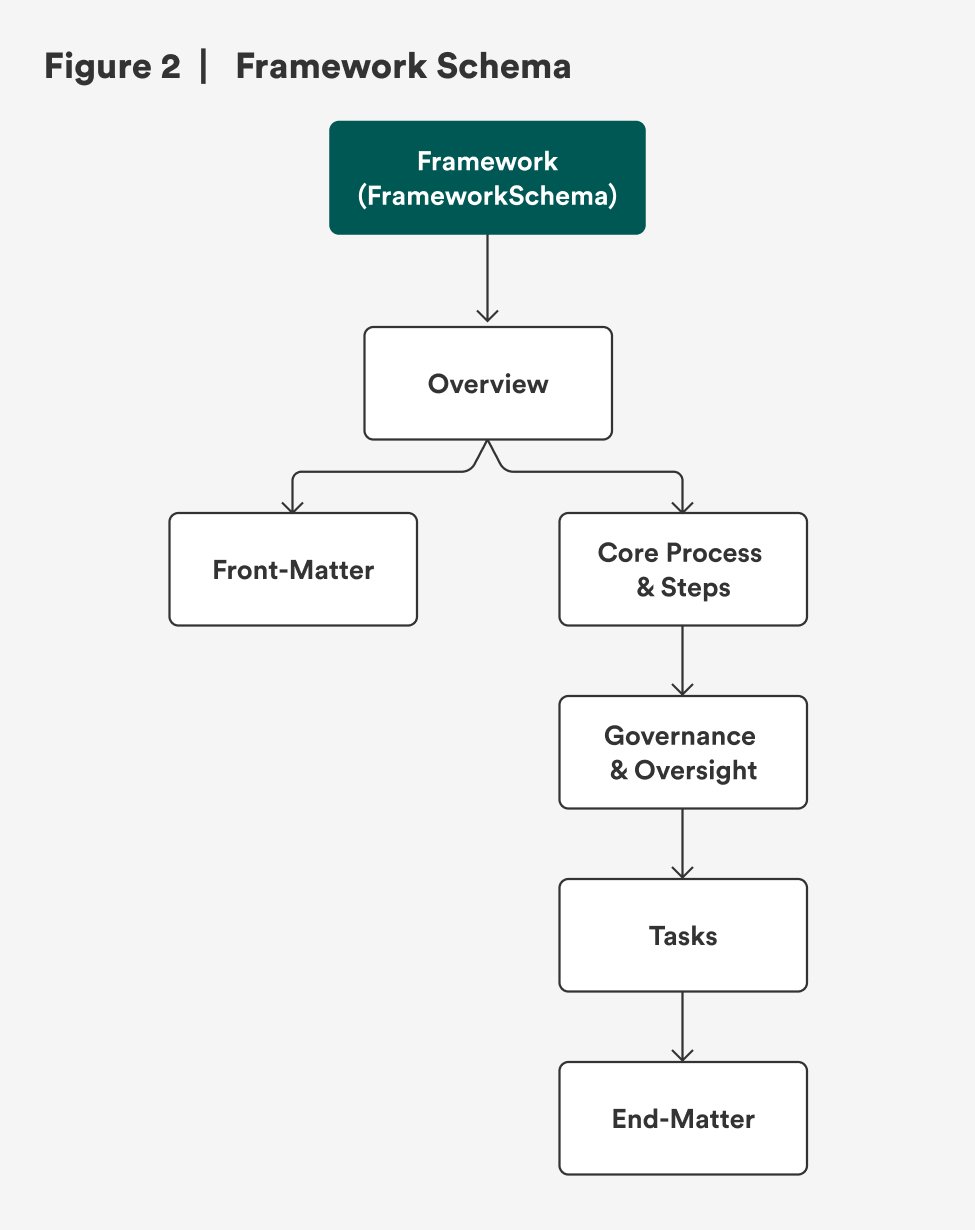
Framework Schema
The “Framework Schema” within GovSCH provides a standardized, machine-readable structure for capturing the essential elements of cybersecurity and risk management frameworks, such as the NIST Risk Management Framework (SP 800‑37) and DoD RMF (DoDI 8510.01). Its design reflects these frameworks’ layered, process-driven nature, while ensuring adaptability for future versions or similar governance instruments (see Figure 2 and Table 5).
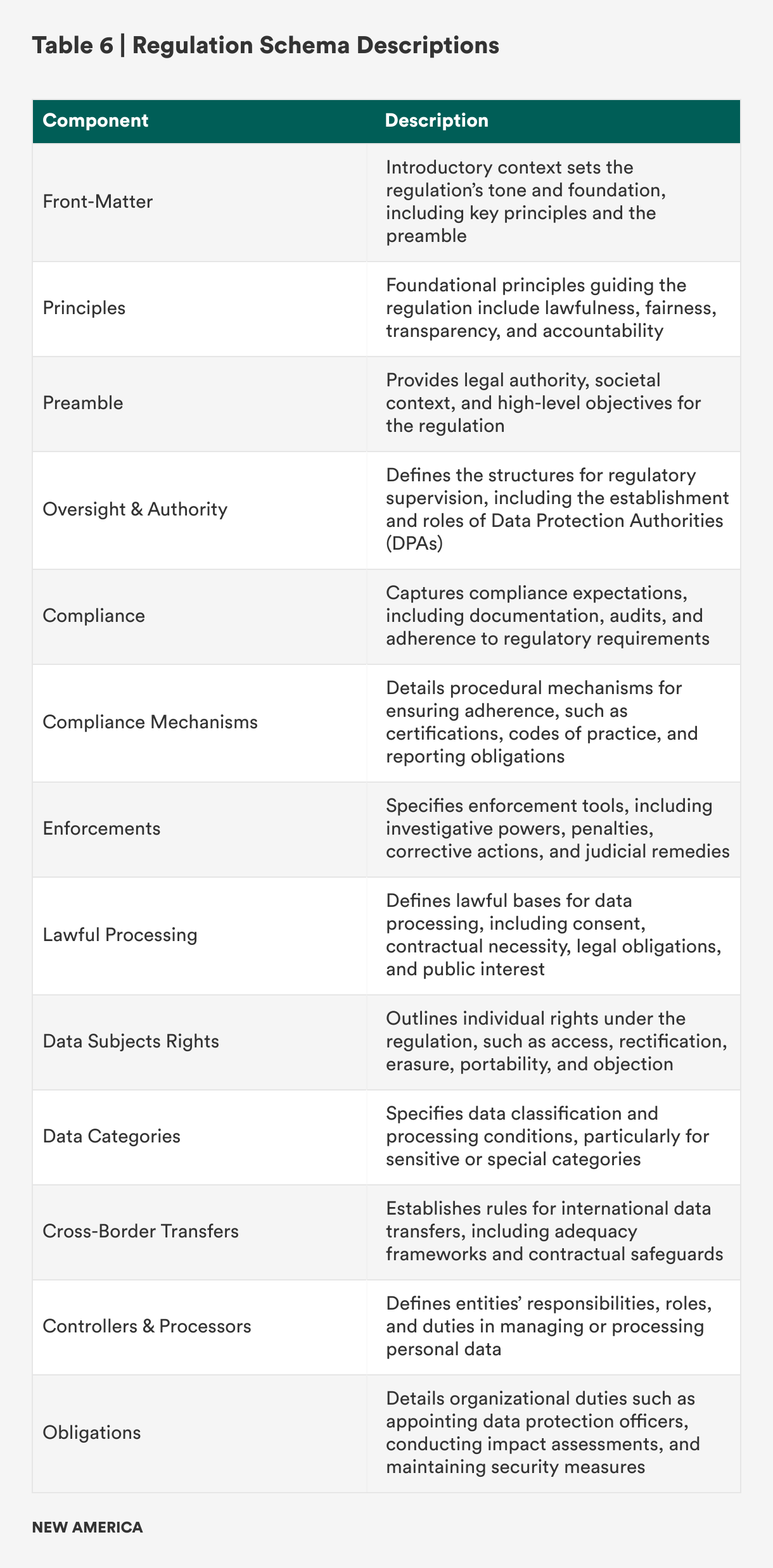
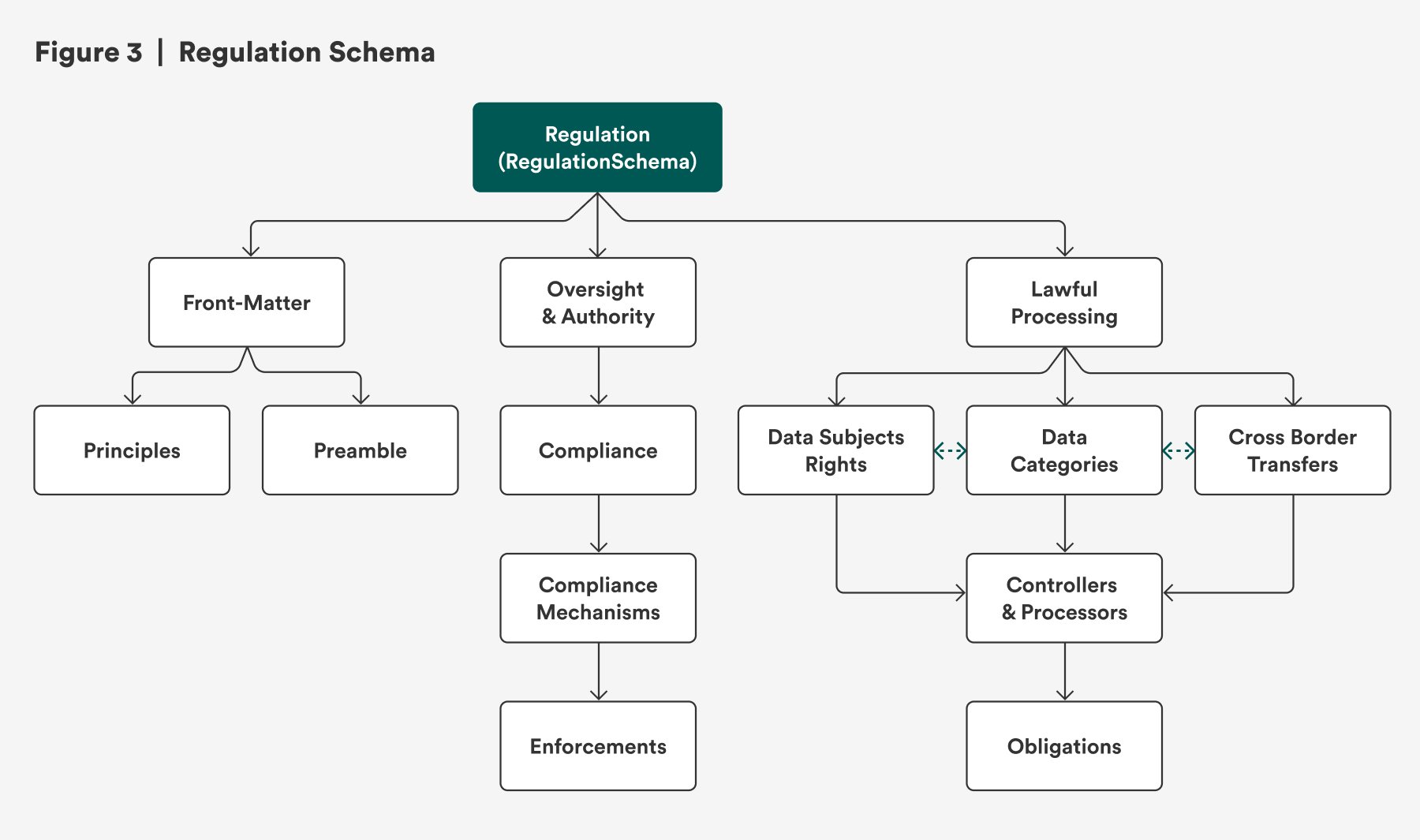
Regulation Schema
The “Regulation Schema” within GovSCH provides a comprehensive, machine-readable structure for capturing the essential components of international data protection and privacy laws, such as the General Data Protection Regulation (GDPR) in the European Union and United Kingdom, the Lei Geral Proteção de Dados (LGPD) in Brazil, the Personal Information Protection Law (PIPL) in China, and similar instruments. This schema captures the breadth of regulatory content, legal authority, principles, rights, obligations, and enforcement mechanisms, while maintaining a clear and logical hierarchy for easy use in compliance, governance, and automation contexts (see Figure 3 and Table 6).
Analysis and Reflection
The development of GovSCH’s distinct schemas for executive orders, frameworks, and regulations underscores the necessity for structured, machine-readable standards in cybersecurity and AI governance. These schemas share core design principles, such as structured metadata, clear hierarchies, defined roles and responsibilities, and explicit compliance mechanisms. However, each is explicitly tailored to its context. Collectively, they offer significant advancements toward greater coherence, interoperability, and efficiency in policy development, implementation, and compliance.
Complementary Roles and Distinctive Features
Each schema addresses a unique governance document type, reflecting distinct purposes and audience needs:
Executive Orders Schema
- Directive-focused: This schema emphasizes clear instructions, deadlines, responsible entities, and implementation mechanisms, which are critical for translating high-level presidential directives into actionable policy tasks.
- Authoritative precision: It prioritizes capturing explicit legal provisions and executive intent, enhancing accountability, clarity, and enforcement capacity within government and related institutions.
Framework Schema
- Process-oriented: This schema meticulously details operational steps, tasks, inputs, outputs, roles, and expected outcomes, ensuring comprehensive coverage of risk management and cybersecurity processes, as exemplified by risk management frameworks from NIST and DoD.
- Structured flexibility: It is intentionally designed to balance structural consistency with the flexibility required to adapt to diverse organizational contexts and varying implementation scenarios.
Regulation Schema
- Rights-based and enforcement-driven: This schema extensively defines rights, obligations, compliance mechanisms, and enforcement strategies, reflecting the detailed, prescriptive nature of international privacy and data protection regulations such as GDPR, LGPD, and PIPL.
- Global applicability: It captures universal regulatory components, accommodating cultural and jurisdictional differences, making it particularly valuable for multinational organizations facing complex cross-border compliance landscapes.
Shared Design Principles and Interoperability
Despite their tailored characteristics, these schemas consistently apply a set of fundamental design principles that enhance their practical value:
- Hierarchical clarity: Each schema employs nested structures (metadata, sections, and subsections) that mirror the original documents’ logical organization, facilitating readability and automation for teams tasked with implementing policy in builds and products.
- Machine-readability and human-friendliness: Available in JSON and YAML, the schemas bridge the gap between automated compliance tools and human policy analysts, enabling seamless integration across different organizational functions.
- Semantic consistency: Clear definitions and standardized terminology improve communication between policymakers, compliance professionals, and engineers, promoting alignment and mutual understanding.
- Practical flexibility: Optional fields, extensible components, and flexible arrays ensure the schemas can evolve alongside new policies, frameworks, and regulatory developments.
Implications for Cybersecurity and AI Governance
Introducing these structured schemas marks a significant step toward more rigorous and transparent governance. By standardizing the expression of complex governance documents, GovSCH facilitates improved clarity, consistency, and interoperability across governance contexts. Potential implications include:
- Enhanced policy implementation: Clearly defined roles, tasks, and timelines within these schemas enable rapid translation of governance directives into actionable tasks, thereby accelerating compliance cycles.
- Improved accountability and auditability: Structured schemas enable systematic tracking, auditing, and validation of policy adherence, supporting enhanced governance accountability and organizational transparency.
- Reduced compliance burden: The schemas facilitate automation of compliance processes, significantly reducing the overhead associated with manual interpretation and documentation of policy requirements and also enabling quicker adaptation to changing regulatory landscapes.
- Interdisciplinary collaboration: By creating a common language between policy drafters, compliance specialists, and engineers, the schemas promote more effective collaboration, reduced misunderstandings, and greater organizational efficiency.
Reflection on Limitations
Despite their strengths, these schemas must be acknowledged within realistic boundaries. While they are foundational for streamlining compliance, they are primarily designed to simplify authoring, interpretation, and implementation, rather than to function as comprehensive enforcement tools themselves. Real-world validation through widespread industry adoption, stakeholder feedback, and continuous refinement remains a critical next step. The open-source nature of GovSCH allows for iterative evolution driven by community and institutional engagement, ensuring the schemas stay relevant and practical.
Reflection on Opportunities
Future opportunities for development include extending these schemas into compliance automation platforms, integrating AI-assisted regulatory change management, and expanding their scope to additional governance instruments. Leveraging these schemas in combination with advanced analytics, artificial intelligence, and continuous monitoring technologies could unlock significant efficiencies and effectiveness in global governance and compliance ecosystems.
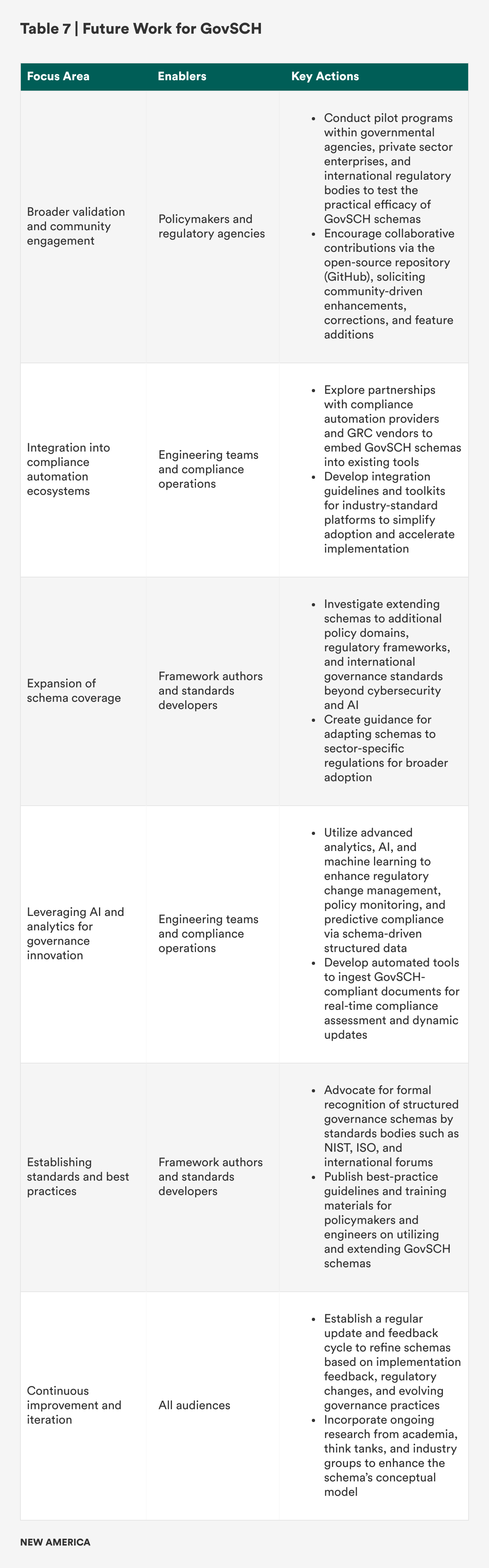
Recommendation and Building Forward
GovSCH’s development and application represent a meaningful stride forward in digital governance and compliance innovation. GovSCH aligns governance practices with contemporary demands for clarity, interoperability, and automation by providing structured, machine-readable schemas. This alignment positions GovSCH as a valuable resource for policymakers, regulatory bodies, private sector enterprises, and compliance professionals navigating the increasingly complex cybersecurity and AI regulatory landscape.
The work presented in this report is potentially foundational. However, realizing GovSCH’s full potential requires sustained effort, community engagement, practical validation, and continuous refinement. To this end, several strategic recommendations and future steps are proposed in Table 7 below.
Conclusion
The development and documentation of GovSCH’s standardized schemas represent an essential advancement in the systematic structuring and machine-readable translation of governance documents related to cybersecurity and artificial intelligence. This report has illustrated how structured standardization can bridge the gap between complex policy language and practical implementation, fostering greater transparency, accountability, and operational efficiency across organizations and jurisdictions by introducing structured schemas for (1) executive orders, (2) frameworks, and (3) regulations.
GovSCH’s schemas collectively address persistent policy and regulatory implementation challenges, including ambiguity in policy interpretation, inconsistencies in compliance practices, and inefficiencies arising from manual processes. Though tailored to its specific governance type, each schema embodies shared principles such as clarity, semantic consistency, machine-readability, and adaptability, which are essential for enabling streamlined governance and compliance automation.
GovSCH embodies a potentially transformative vision for modern governance. It lays the groundwork for significantly improved governance efficiency, compliance assurance, and operational clarity by structuring cybersecurity and AI governance documents into transparent, interoperable, and automatable schemas. It has the potential to facilitate a deeper, more collaborative dialogue between policymakers, regulatory authorities, technology developers, and compliance practitioners worldwide.
Achieving this vision, however, requires sustained collaboration and innovation. Policymakers and governance bodies must be receptive to adopting structured authoring practices. Regulatory authorities and standards organizations need to embrace and support schema-based approaches. Private and public sector entities should actively refine and deploy these schemas, thus enhancing global governance effectiveness and trustworthiness in cybersecurity and AI ecosystems. GovSCH represents a pivotal opportunity to drive global governance forward. By embracing structured, machine-readable governance, we collectively move toward a future characterized by greater transparency, accountability, agility, and resilience, which are essential in navigating the complex and dynamic challenges of cybersecurity and AI governance today and into the future.
GovSCH is deliberately provided as an open-source initiative, emphasizing transparency, collaborative improvement, and community engagement. All schema documentation, technical specifications, and practical implementation examples are freely accessible via the GovSCH. This open approach encourages participation from policymakers, regulatory authorities, industry experts, engineers, compliance professionals, and academia, ensuring the schemas’ continuous evolution, refinement, and practical relevance. Through open-source collaboration, GovSCH aims to foster a collective and shared commitment to better global cybersecurity and AI governance.