Table of Contents
Chapter 2: How Did We Get Here?
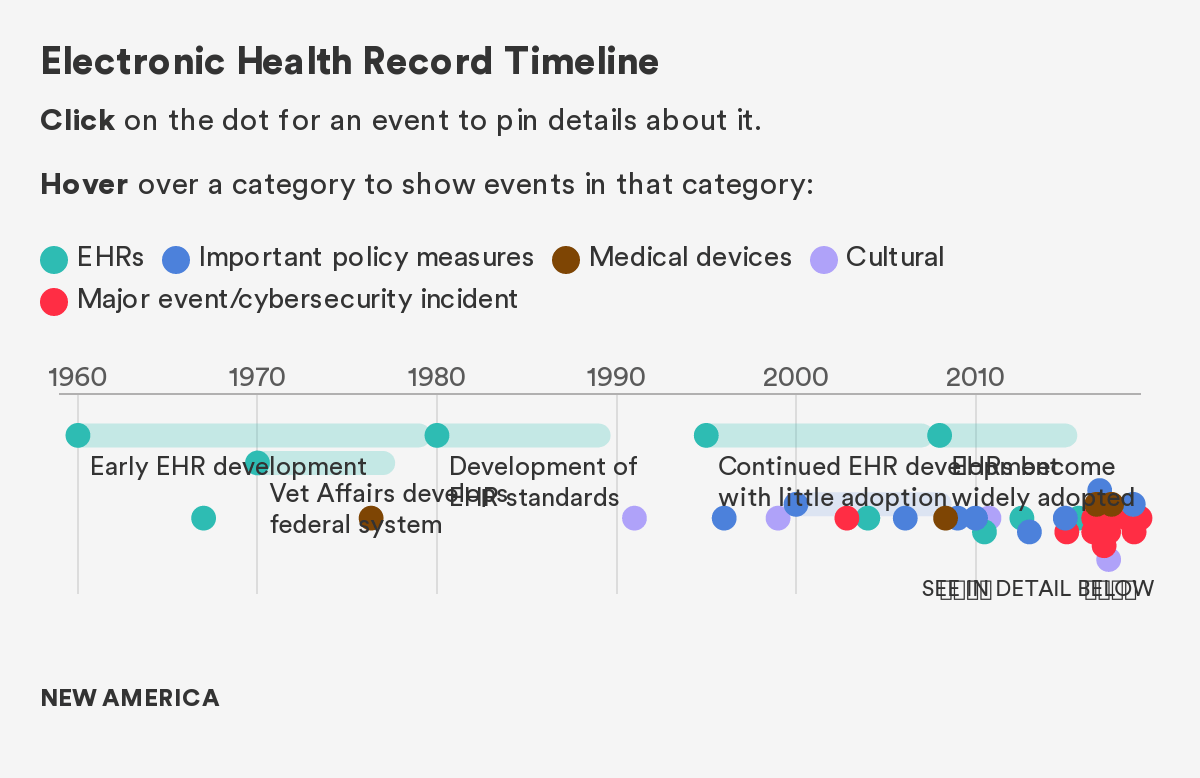
Before introducing the policy solutions that can help steer healthcare towards a more cyber-secure future, it is useful to understand the historical context that shaped the current healthcare cybersecurity landscape. The following section provides a brief historical overview and timeline of the events and policies that underpin the current state of cyber insecurity in the healthcare sector.
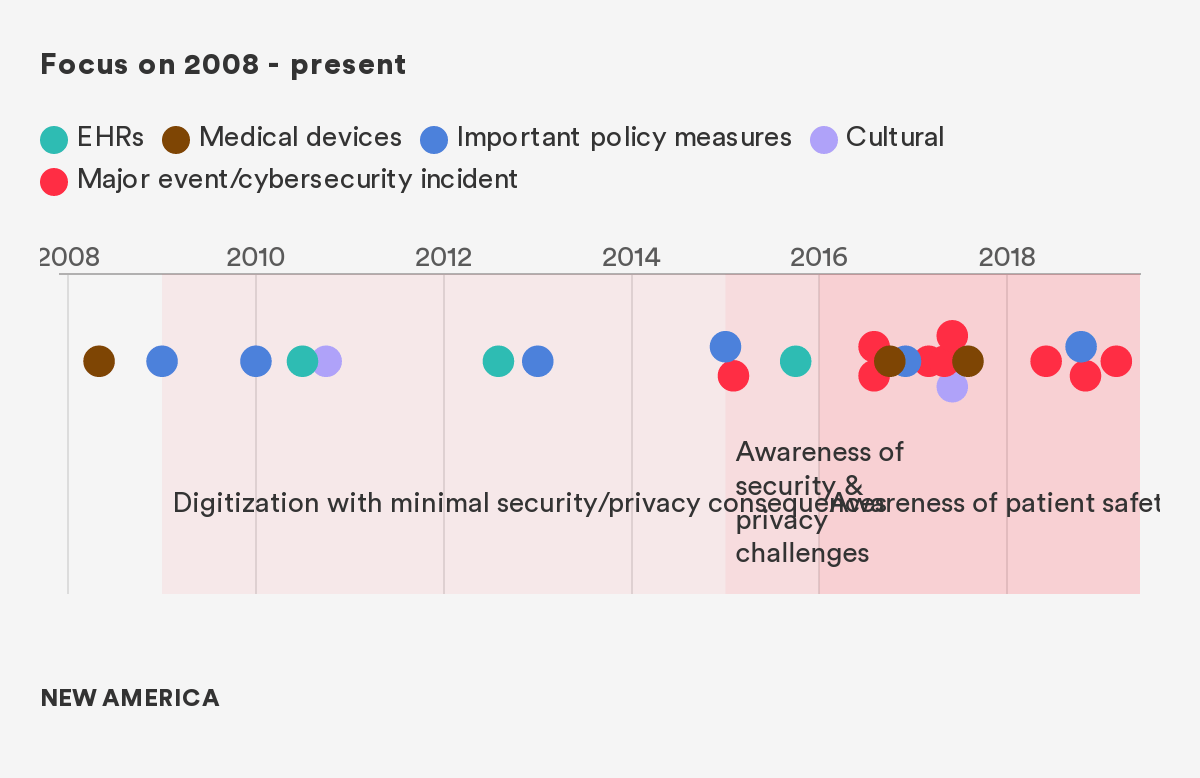
The story of the last decade of healthcare privacy and security is one that is defined by both progress and tragedy, often in parallel. With the broad rollout of EHR technology, driven by meaningful use incentives contained in the HITECH Act of 2009, the capacity of healthcare infrastructure transformed to capture and access patient health data electronically.1 However, this transformation came at a great cost—the creation of a slate of privacy and security vulnerabilities that are only beginning to be addressed. Likewise, the burgeoning of new wirelessly connected medical devices,2 sometimes referred to as the medical Internet of Things (mIoT), increased healthcare’s reliance on medical data to improve chronic and diet-related illnesses,3 predict disease outbreaks,4 and create strategic benefits driven by big data analytics.5 The use of algorithms and big data has also enabled clinicians to, with extraordinary accuracy and efficiency, diagnose, and treat diseases including skin cancer, cardiovascular disease, and retinopathy (which causes blindness), and predict a patient’s likelihood of deteriorating or dying.6
While many efforts were focused on improving patient care and interoperability—and appropriately so—this forward sprint neglected the concomitant deployment of technologies that would ensure these systems were secure, and that the data held within them was not accessible to individuals who had no use for it. As a result, the system created hundreds of millions of vulnerable digital medical records, and innumerable vulnerable devices and other entities, all of which led to a vast number of attacks over the past decade.
As Figure 1 demonstrates, the transition to EHR started slowly, but an explosion occurred in 2009, and with it, an attendant explosion of both large and small cybersecurity events, all of which had the potential for devastating impact.7 Since To Err is Human, the seminal report on patient safety and medical errors that defined a generation of clinical research, the industry has experienced tremendous improvement in attentiveness to patient safety and medical errors.8 However, only in the last few years, has some of this research related to the safety and dignity of patients and how this is impacted by cybersecurity and privacy vulnerabilities.
We separate out the pre-2008 and post-2008 era largely because of the significant transformation in healthcare technology that occurred in 2009 with the HITECH act. This massive incentive program (in combination with other secular trends in the space) fundamentally changed the digital landscape, creating new opportunities and new vulnerabilities.
Figure 1: The Events, Policies, and Technologies That Have Affected Healthcare Cybersecurity
Citations
- The number of physicians and hospitals using at least a basic EHR in 2008 was only 17 percent and nine percent, respectively. By 2015, however, the number of hospitals and physicians using even more robust certified EHR technologies had skyrocketed to 96 percent and 78 percent, respectively. For more, see: The Office of the National Coordinator for Health Information Technology, 2016 Report to Congress on Health IT Progress: Examining the HITECH Act and the Future of Health IT (Washington, DC: Department of Health and Human Services, 2016).
- The number of connected things in use worldwide, including medical devices, wearables, and mobile phones, was more than 8 billion in 2017 and will reach 20.4 billion by 2020. The market for global connected medical devices is expected to reach “$1.34 billion by 2021 at a growth rate of 26 percent.” For more, see: Bill Kleyman, “The Future of Edge Healthcare Services and HIT Infrastructure,” HIT Infrastructure, February 26, 2018; Elizabeth O’Dowd, “Health IT Connected Medical Device Market on the Rise,” HIT Infrastructure, October 24, 2016.
- Dimiter Dimitrov, “Medical Internet of Things and Big Data in Healthcare,” Healthcare Informatics Research 22 (July 2016): 156-163.
- Min Chen, Yixue Hao, Kai Hwang, Lu Wang, Lin Wang, “Disease Prediction by Machine Learning Over Big Data From Healthcare Communities,” IEEE Access Volume 5 (April 26, 2017): 8869-8879.
- Yichuan Wang, LeeAnn Kung, Terry Anthony Byrd, “Big Data Analytics: Understanding its capabilities and potential benefits for healthcare organizations,” ScienceDirect Volume 126 (January 2018): 3-13.
- Andrew Burt and Samuel Volchenboum, “How Health Care Changes When Algorithms Start Making Diagnoses,” Harvard Business Review, May 08, 2018.
- We would also like to note a counterargument posed by some very thoughtful commentators on this topic – notably that before HITECH, there were no standards for cybersecurity, and there was a very bad state of healthcare cybersecurity investment even before the 2009 incentives, minimizing the extent to which you can lay our current predicament at the feet of these incentives. We concur—we think that a fair characterization of healthcare cybersecurity is that it was bad before HITECH, it was on balance made worse by the explosion in EHRs, but that there were certainly some good security and privacy innovations that came from regulators through Meaningful Use requirements and other federal incentives.
- Linda T. Kohn, Janet M. Corrigan, Molla S. Donaldson, To Err Is Human, The National Academies of Sciences Engineering Medicine, November 1999.