Table of Contents
IV. From Risk to Resilience: Policy and Public Awareness Pathways
As discussed elsewhere in this report, traditional narratives often frame cyber threats as issues affecting specific individuals or companies. Everyday individuals may underestimate their own human vulnerabilities, and particularly those that lead to cybersecurity vulnerabilities. This section thus divides the individual from systemic solutions, in line with the human vulnerabilities discussed throughout this report, which are both individual (literacy and skills) and systemic (access).
Support and Scale Individual Awareness
Policies and systemic protections are vital to reducing cybersecurity risks, but individual awareness remains a critical frontline defense, especially in light of persistent assumptions about who is truly at risk. Due to these assumptions, there is a dangerous gap between risk and perceived threat. To close this gap, individuals must first be made aware of their human vulnerabilities that may lead to cybersecurity vulnerabilities. Further, digital literacy and skills must become standard knowledge for all users, not just information technology professionals or industry experts.
Although there are human factors that can contribute to cybersecurity vulnerabilities, education increases an individual’s ability and opportunity to proactively respond.1 Cyber education and awareness must be targeted toward the understanding that gaps in digital skills, literacy, and access may produce cybersecurity vulnerabilities. These human vulnerabilities are not just isolated personal shortcomings but often reflect broader systemic inequities, and recognizing the connection between human and cyber vulnerabilities will help increase awareness and hopefully lead to proactive behavior.
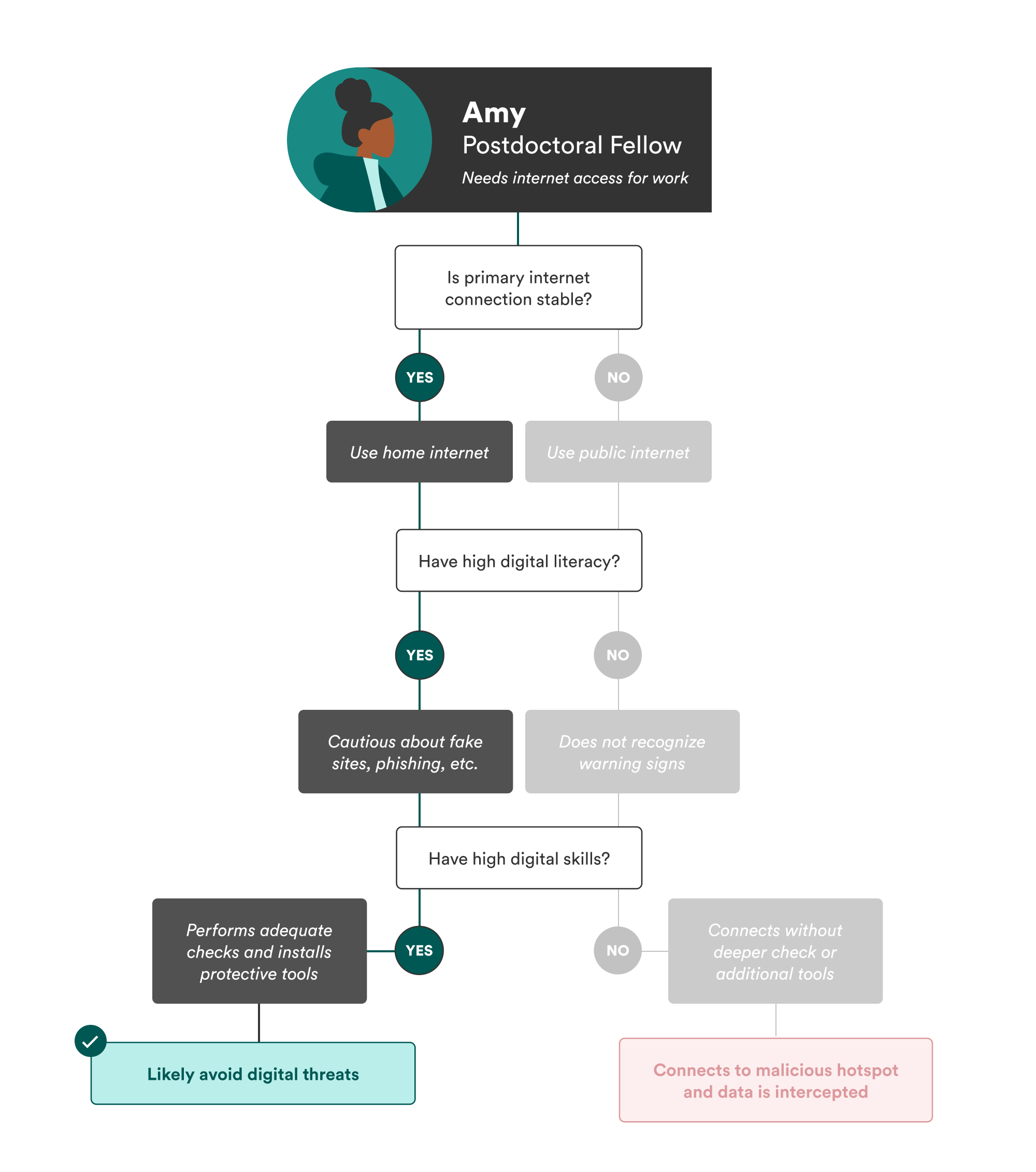
If Amy had been aware of her own vulnerabilities, she might have been more cautious about connecting to the café’s Wi-FI hotspot. Even if she lacked the technical skills or literacy to detect the risk outright, simply understanding her limitations, as illustrated by the steps in Figure 3, could have prompted her to seek safer alternatives or to ask for help, thereby reducing her exposure to cyber threats.
However, awareness about potential threats is not enough; people must be equipped with digital literacy and skills to recognize and respond to threats effectively. Resources are increasingly available to help individuals build digital resilience, and policymakers must support these initiatives—if not through specific mandated programming or national campaigns, then through funding.
Public libraries, for example, have become valuable community hubs for digital education.2 While libraries have always functioned as a “third place,” a welcoming atmosphere other than home and work or school for community, interaction, and learning, they played a key role in closing the digital divide during the COVID-19 pandemic.3 The Federal Communications Commission’s Digital Empowerment and Inclusion Working Group produced a report in 2021 describing congressional funding that enabled libraries to increase digital literacy and access.4 In Illinois, for example, Evanston Public Library provided “Ready-to-Work Starter Kits” to help patrons build basic computer and literacy skills.5
Nonprofit organizations like the National Digital Inclusion Alliance (NDIA) advance digital equity by “supporting community programs and equipping policymakers to act.” Through its Digital Inclusion Program Model, which provides guidance for digital inclusion programs, and its Digital Navigator Model, a replicable framework to help volunteers or staff provide digital skills and access, NDIA provides comprehensive tools to support local communities in closing the digital divide.6
Although the 2025 federal funding cuts have severely impacted many programs’ ability to provide digital literacy and skills training and classes, NDIA and a few other local organizations are still providing help that individuals need to be better equipped to recognize cybersecurity threats.7 To fill this gap, policy initiatives must prioritize sustainable funding for digital literacy and cybersecurity education at organizations like the NDIA. Equally important, these initiatives must explicitly address the link between human and cybersecurity vulnerabilities in order to create more comprehensive and resilient digital safety strategies. This could involve expanding NDIA’s Digital Navigator Model to include awareness of human vulnerabilities specific to the communities they serve, or adapting NDIA’s Digital Inclusion Program Model to emphasize partnerships between digital literacy programs and cybersecurity educators.
Design Vulnerability-Aware Cyber Policy
Attributing errors solely to individual failings reflects a narrow perspective that overlooks the critical role of institutional and systemic design in shaping human behavior. Effective cybersecurity policy must go beyond these traditional narratives, including the understanding that cybersecurity solutions are only technical in nature, and recognize that there are many different structures that create or exacerbate vulnerability.
Build on BEAD and the DEA to Address Cyber Risks
Policymakers should deepen their investment in existing frameworks—namely, the Broadband Equity Access and Deployment Program (BEAD) and the now-terminated Digital Equity Act (DEA)—to create and ensure long-term, systemic integration of human-centered approaches to cybersecurity.
BEAD acknowledges structural exclusions in internet infrastructure, but it does not go far enough in addressing the digital divide’s implications for cybersecurity. Notably, the program authorized funds for non-deployment uses, which could include cybersecurity and digital skills.8 However, on June 6, 2025, the Commerce Department paused all funding for non-deployment projects pending further guidance, casting uncertainty over the future of BEAD funding for these purposes.9 Millions still remain in broadband deserts, and others navigate the digital world without adequate literacy or skills—all of which increases susceptibility to cyber threats.10 Despite the important work that BEAD supports, there remains no clear mechanism that addresses the connection between human and cybersecurity vulnerabilities. The groundwork laid by digital divide policies like BEAD to expand digital access, skills, and literacy must be strengthened to directly address how lower levels of these factors can increase vulnerability to cybersecurity threats.
To achieve this, policy must center long-term investments in digital skills and literacy training aimed at the relationship between human and cybersecurity vulnerabilities. The DEA, created to help fund digital skills training, was a promising step in that direction. Its authorizing statute also mandated states’ digital equity plans to include ways to document and promote “awareness of, and the use of, measures to secure the online privacy of, and cybersecurity with respect to, an individual.”11 Nonetheless, digital divide and cybersecurity policy have yet to converge in a meaningful way. While state plans were mandated to include cybersecurity awareness, many other programs funded by the statute (those by non-state entities) did not include such a focus,12 and “cybersecurity awareness” has failed to fully address the human vulnerabilities described in this report. There may have been an opportunity to build on the initial progress of the DEA, but in May 2025, the Commerce Department announced that it would not move forward with DEA programming because of the statute’s requirement that funded programs serve marginalized populations. As a result, all grants are now terminated under the DEA.
Despite the discontinuation, the DEA—together with programs like BEAD—provides a valuable foundation for advancing a more human-centered cybersecurity strategy. Programs that solely focus on the digital divide should be expanded to support cybersecurity education, community-based training programs, and digital literacy outreach, with a specific emphasis on the connection between human and cybersecurity vulnerabilities. These policy efforts should complement, rather than replace, existing, more technical cybersecurity policies.
If we want effective and equitable cybersecurity policy, statutes like the DEA should be reestablished and redesigned around the recognition that human vulnerabilities often stem from inadequate systemic support and inequitable access to knowledge. The DEA had the capacity to fund programs related to digital skills and literacy, but future initiatives must go further: There must be an explicit acknowledgement and commitment toward the intersection between human and cybersecurity vulnerabilities, and there must be deeper investment in human-centered cybersecurity policies. Any future version of statutes like the DEA should explicitly require grantees to demonstrate how they are addressing human and cybersecurity vulnerabilities. By redeveloping programs like BEAD and the DEA, which already prioritize the human vulnerabilities this report describes, policymakers can begin to address the human factors at the heart of cybersecurity.
Maintaining, reviving, enhancing, and creating programs and statutes like BEAD and the DEA—rather than building entirely new structures—offers a practical path forward because the groundwork is already there. Nonetheless, shifts in federal policy and funding may curtail these efforts; thus, in addition to the work of policymakers, other stakeholders have a role to play. Companies affected by users’ lack of digital literacy can invest in user education initiatives, and philanthropies can support nonprofits providing community-based digital skills training.
What is needed now is a policy shift to move from seeing the digital divide and cybersecurity as separate siloes to recognizing the overlooked nexus.
Embed Participatory Frameworks in Design and Governance
Ethical, human-centered design must be a core component of cybersecurity policy. Frameworks such as “Secure by Design” or “Privacy by Design” emphasize that technologies should reflect users’ values and protect their rights by default.13 Yet few cybersecurity policies are designed with the digital divide in mind—even though the values embedded in digital divide policy efforts, such as equitable access, digital literacy, and user empowerment, are precisely what ethical design should account for.
To operationalize these principles, participatory approaches such as collaborative policy audits (evaluations of implemented policies with robust community involvement) or participatory threat modeling (which allows users to participate in research and define their own threats) can play a critical role in identifying and articulating human vulnerabilities that often go unrecognized in cybersecurity policymaking.14 These methods move beyond abstract design ideals by grounding policy in actual experience, allowing communities to articulate what access, risk, and protection mean in their context.
Only through collaborative and equitable engagement can the layered nature of human vulnerabilities be meaningfully explored. While RAND did create its framework through interviews of industry experts, this kind of top-down model often misses the lived experiences of those most impacted by poor cybersecurity infrastructure or policy. Institutions like NIST or RAND should deepen their commitment to incorporating these participatory mechanisms—with an emphasis on gathering information from the everyday user—to ensure that cybersecurity policies reflect the realities of human vulnerabilities. For both design and implementation, participatory approaches can inform not only how technologies are built, but also how risks are identified, prioritized, and managed.
Policymakers should fund and institutionalize these participatory processes so that they are not perfunctory, one-off engagements but, rather, ongoing structures for gathering insight. These methods must also be resourced equitably, with accessible formats, multilingual support, and partnerships with trusted local organizations to ensure meaningful participation. In doing so, nuanced understandings of human vulnerabilities—and how they intersect and contribute to cybersecurity vulnerabilities—can be embedded into the foundation of cybersecurity governance.
Keep Internet Access Equitable
Cybersecurity policy must not be used as a justification to restrict or cut off access to the internet, especially for civil society actors or marginalized groups.15 As organizations such as Access Now have documented, international internet shutdowns and surveillance regimes disproportionately target human rights defenders, journalists, and grassroots organizers, many of whom already lack the digital defenses they need to protect themselves. While these individuals lack consistent internet access, they may also lack digital literacy and skills—all of which are factors that can increase their exposure to cybersecurity vulnerabilities, which in turn can undermine their ability to safely carry out critical civic work.
Although internet shutdowns are typically associated with authoritarian contexts, U.S. cybersecurity policymakers must remain vigilant against these and other forms of digital exclusion. Restrictive content moderation due to cyber risks or poorly scoped threat response mechanisms can have similar exclusionary effects, particularly for marginalized communities.
Within the United States, access to the internet should continue to expand, not diminish. If cybersecurity justifications do emerge—such as emergencies prompting limited access—they should not curtail connectivity. Given the unpredictable level of federal investment in broadband programs like BEAD, it is crucial to ensure that cybersecurity concerns do not become a barrier to equitable access. This includes calls to restrict access based on identity, geography, or resource level under the guise of national security.
Security should not come at the cost of connectivity. Instead, policies should aim to fortify access (through programs like BEAD, but expanded) and support at-risk communities with the tools and training they need to stay safe online (through statutes like the DEA, but expanded).
Citations
- See Elrayah and Jamil, “Impact of Digital Literacy and Online Privacy Concerns on Cybersecurity Behaviour,” source.
- Public Library Association (PLA), 2023 Public Library Technology Survey: Summary Report (PLA, 2024), source.
- James K. Elmborg, “Libraries as the Spaces Between Us: Recognizing and Valuing the Third Space,” Reference & User Services Quarterly 50, no. 4 (Summer 2011): 338–50, source.
- Digital Empowerment and Inclusion Working Group, The Role of Public Libraries and Community Partnerships in Promoting Digital Adoption (Federal Communications Commission, June 24, 2021), source. See also “American Libraries and Museums Awarded $13.8 Million in IMLS CARES Act Grants,” Institute of Museum and Library Services, September 24, 2020, source.
- “Show Us the Money: Federal Broadband Support During the COVID-19 Pandemic,” Benton Institute for Broadband & Society, April 23, 2021, source.
- National Digital Inclusion Alliance (NDIA), The Digital Inclusion Program Manual (NDIA, 2024), source; “Digital Navigator Model,” National Digital Inclusion Alliance, source.
- For example, the Toledo Lucas County Public Library in Ohio provides local digital divide support and programming. “Digital Equity and Inclusion,” Toledo Lucas County Public Library, source.
- Caroline Stratton, “Three Questions About BEAD Non-Deployment Funding,” Benton Institute for Broadband & Society, June 24, 2025, source.
- Caroline Stratton, “Three Questions About BEAD Non-Deployment Funding,” Benton Institute for Broadband & Society, source.
- Christopher Ali, “For Millions of Americans, High-Speed Internet Is Unavailable or Unaffordable—A Telecommunications Expert Explains How to Bring Broadband to the Places That Need It the Most,” The Conversation, April 24, 2024, source.
- 47 U.S.C. § 1723(c)(1)(B(iv) (2021).
- For example, #BlackTechFutures aimed to use Digital Equity Act funding to establish “digital hubs offering internet access, shared workspaces, and tech training programs.” This is important work, but it is not exactly the work that this report calls for. Habiba Katsha, “Trump Cuts Digital Equity Act Funding: Black Tech Nonprofit Loses $12M,” People of Color in Tech, August 5, 2025, source.
- “Secure by Design,” Cybersecurity and Infrastructure Security Agency, source; “What Is Privacy-by-Design and Why It’s Important?,” Institute of Electrical and Electronics Engineers, source.
- Julia Slupska et al., “Participatory Threat Modelling: Exploring Paths to Reconfigure Cybersecurity,” CHI EA ’21: Extended Abstracts of the 2021 CHI Conference on Human Factors in Computing Systems 329 (May 8, 2021): 1–6, source.
- Tina Nguyen, “Iran Is Going Offline to Prevent Purported Israeli Cyberattacks,” The Verge, June 17, 2025, source.
