Table of Contents
How Human Rights Organizations Assess Their Cybersecurity and Select Tools: Survey Findings
This report draws on insights gathered from an original survey, conducted from May to July 2025, to evaluate the cybersecurity needs of and tools used by human rights organizations. The survey was designed to document organizational practices, decision-making factors, and perceived challenges related to cybersecurity. For details on survey methodology, see the Appendix.
The goal of the survey was to understand how human rights defenders (HRDs) evaluate their cybersecurity posture and threat landscape. To do this, the survey was designed to provide a deeper, more personal understanding of these trends, giving voice to the lived experiences of those working on the front lines. The survey aimed to identify the factors influencing HRDs’ cybersecurity decisions, particularly on how they balance security requirements against activities that directly support their organizations’ primary mission.
In total, representatives from 44 civil society organizations participated in the study, including groups working in human rights and journalism. Participants held positions such as chief executive officer, chief operations officer, network security engineer, and editor. Many participants held multiple roles within their organizations, which is common in grassroots organizations. Respondents were given the option to remain anonymous.
The following sections present the key findings of the survey and include insights from follow-up interviews with select participants.
Overview of Survey Respondents
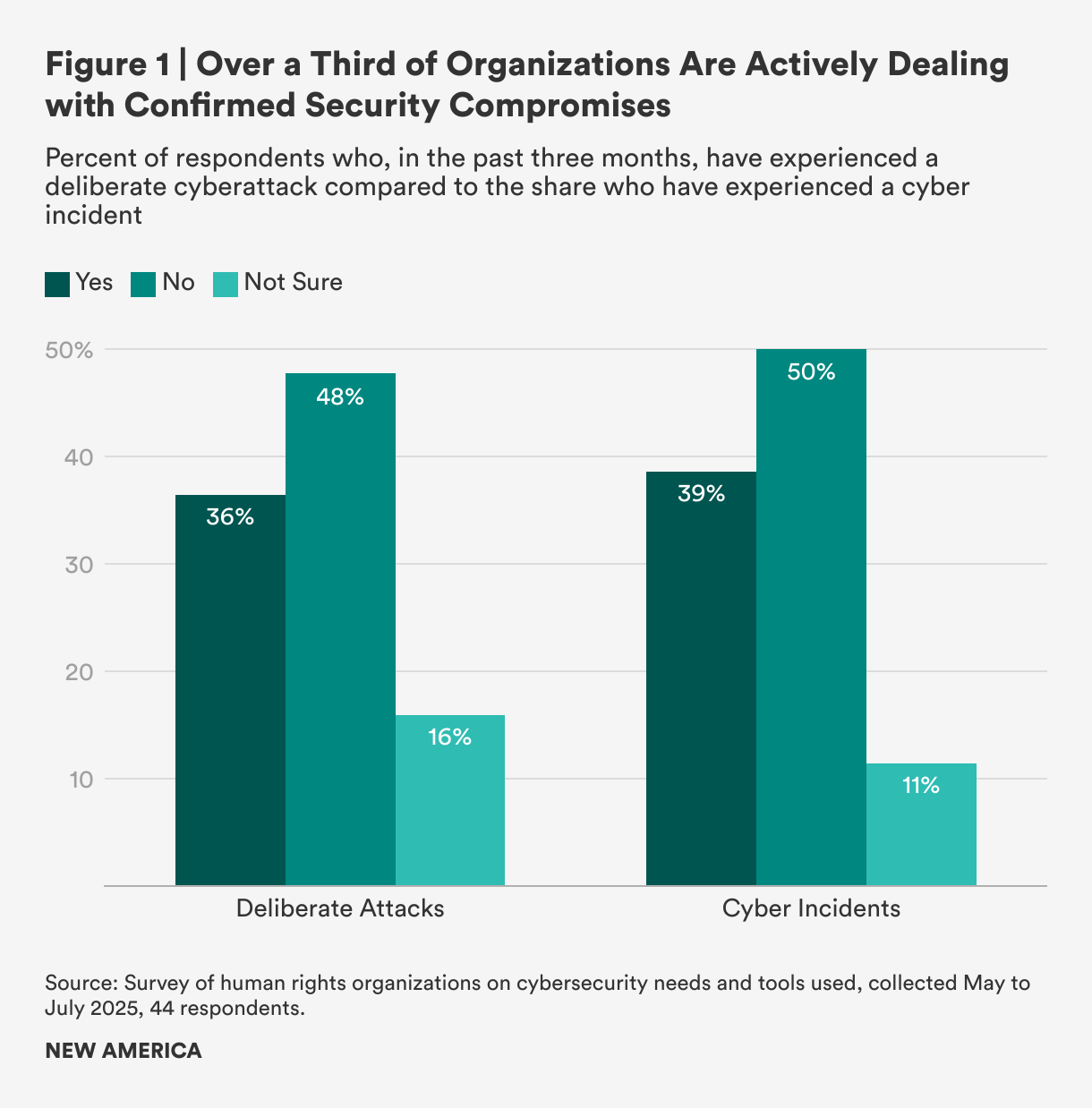
Many of the organizations interviewed had a global footprint with operations on multiple continents. The survey reveals a pattern of security threats facing these organizations. When asked specifically about successful, deliberate cyberattacks (such as ransomware or phishing attacks), 36 percent of organizations said they had been targeted; 48 percent reported they had not been targeted; and the remaining 16 percent were not sure (see Figure 1). This means that a majority of organizations—52 percent—are operating with either a confirmed compromise or a dangerous lack of certainty. This uncertainty poses its own risk: It makes it difficult for organizations to properly manage a compromise, leaving them vulnerable to further attacks and hindering their ability to implement effective security protocols.
When the question was broadened to cover any type of cybersecurity incident, 39 percent of respondents said they had experienced an incident such as a data breach and insider threats (that is, malicious or unintentional misuse of sensitive data or systems by someone with authorized access, like a staff member, volunteer, or trustee). The number of organizations reporting no incidents rose to 50 percent, up from 48 percent for external attacks alone. This suggests that many of those previously “unsure” were more confident they had not been breached by an internal threat (a cyber incident) or external threat (a deliberate attack). For clarity, external threats are deliberate attacks originating outside the organization (for example, malware, phishing, denial-of-service), while internal threats are cyber incidents originating inside the organization (e.g., accidental data leaks, misuse by staff, or compromised insider credentials). The key takeaway remains the same, however: Over a third of organizations are actively managing confirmed security compromises.
Organizations reported facing severe and organized cyber threats from three main types of actors. Government actors were identified as the primary threat by 36 percent of organizations, while cybercriminal groups were cited by 30 percent. Additionally, about 25 percent of organizations identified political or ideological groups as their main threat. Together, these three categories account for over 90 percent of all primary threats, showing that organizations are overwhelmingly targeted by sophisticated groups with clear financial, political, or ideological motives.
A respondent for a Ukrainian civil society organization makes it clear how sophisticated the adversaries are:
“We are constantly navigating a landscape of sophisticated digital threats. For us, a significant concern is malware delivered through well-crafted files sent by fake whistleblowers, a tactic that preys on the trust essential to our work with journalists. The danger is magnified by internal security gaps; a lack of consistent malware education or the absence of a corporate antivirus solution can leave our entire network vulnerable. The stakes are incredibly high, [as] a single compromised device could lead to the imprisonment of our contacts and sources. We see clear evidence that the same military-grade cyber-espionage tools used by state actors, like Lukashenka’s regime [in Belarus] against the Ukrainian military, are the same ones now being turned on us as journalists and activists, which underscores the severity of the threats we face.”
Furthermore, as a respondent for an organization supporting journalists in Eastern Europe noted, sophisticated state actors are able to prey on the specific vulnerabilities of HRDs:
“We recently assisted a Belarusian organization that was targeted by a sophisticated FSB phishing attack in 2024. The attack was successful because they had not yet implemented phishing-resistant two-factor authentication. Our role was to help them analyze the breach, identify the compromised data, and alert their people on the ground who faced potential criminal prosecution and needed to evacuate. To help prevent these incidents, we now work with organizations to receive and configure FIDO2/U2F security keys, like those from Yubico and Google, which provide the necessary protection against these advanced threats.”
Cybersecurity Capacity
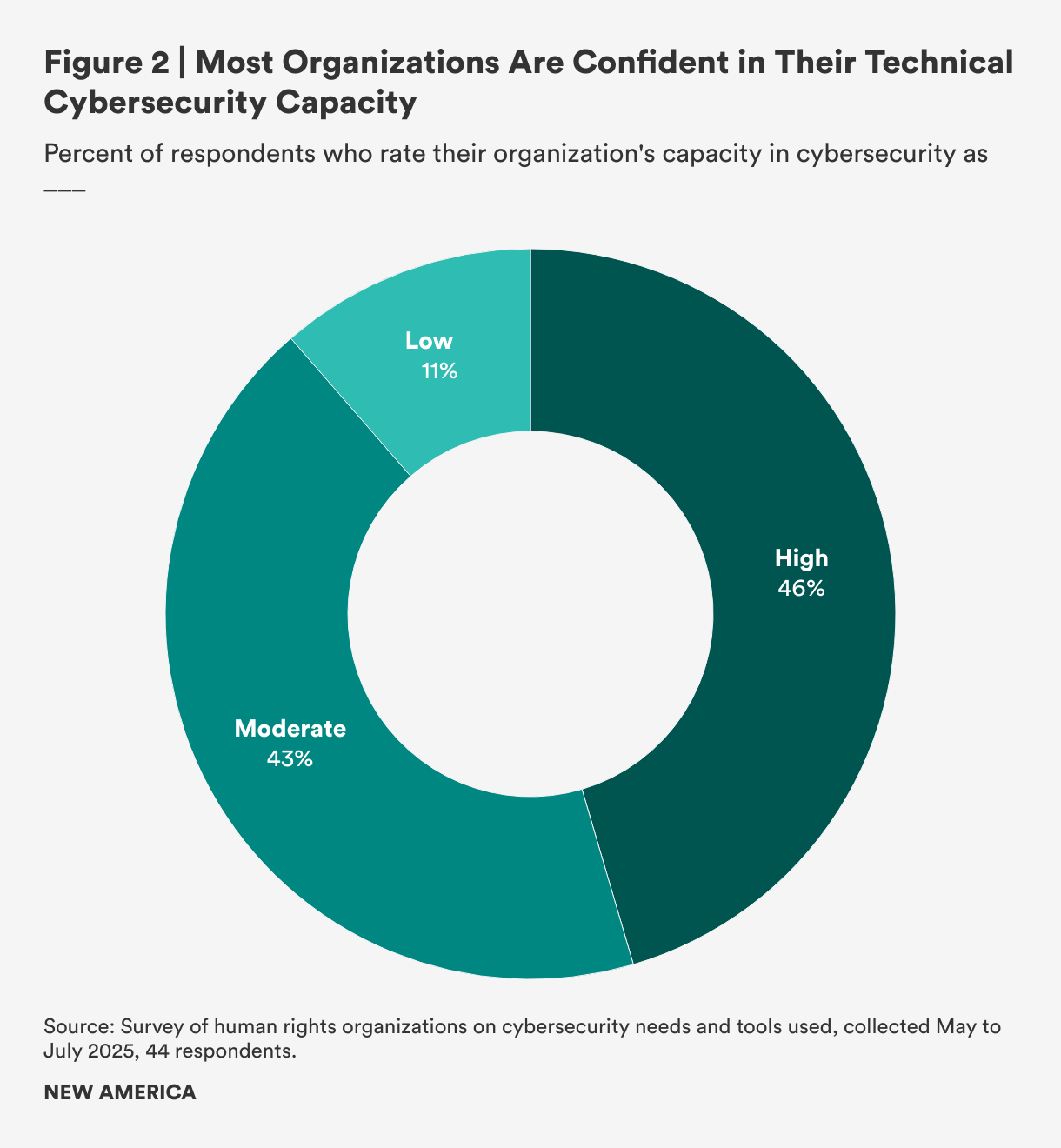
The survey reveals that organizations generally feel confident in their cybersecurity management, with none reporting “very low” capacity. Nearly half (46 percent) of the organizations rated their capacity as “high,” meaning they have dedicated staff who proactively manage their cybersecurity (see Figure 2). Another large group (43 percent) described their capacity as “moderate,” with enough technical knowledge to handle their security needs, while the remainder (11 percent) reported “low” capacity, signifying a heavy reliance on external support or struggles with internal management.
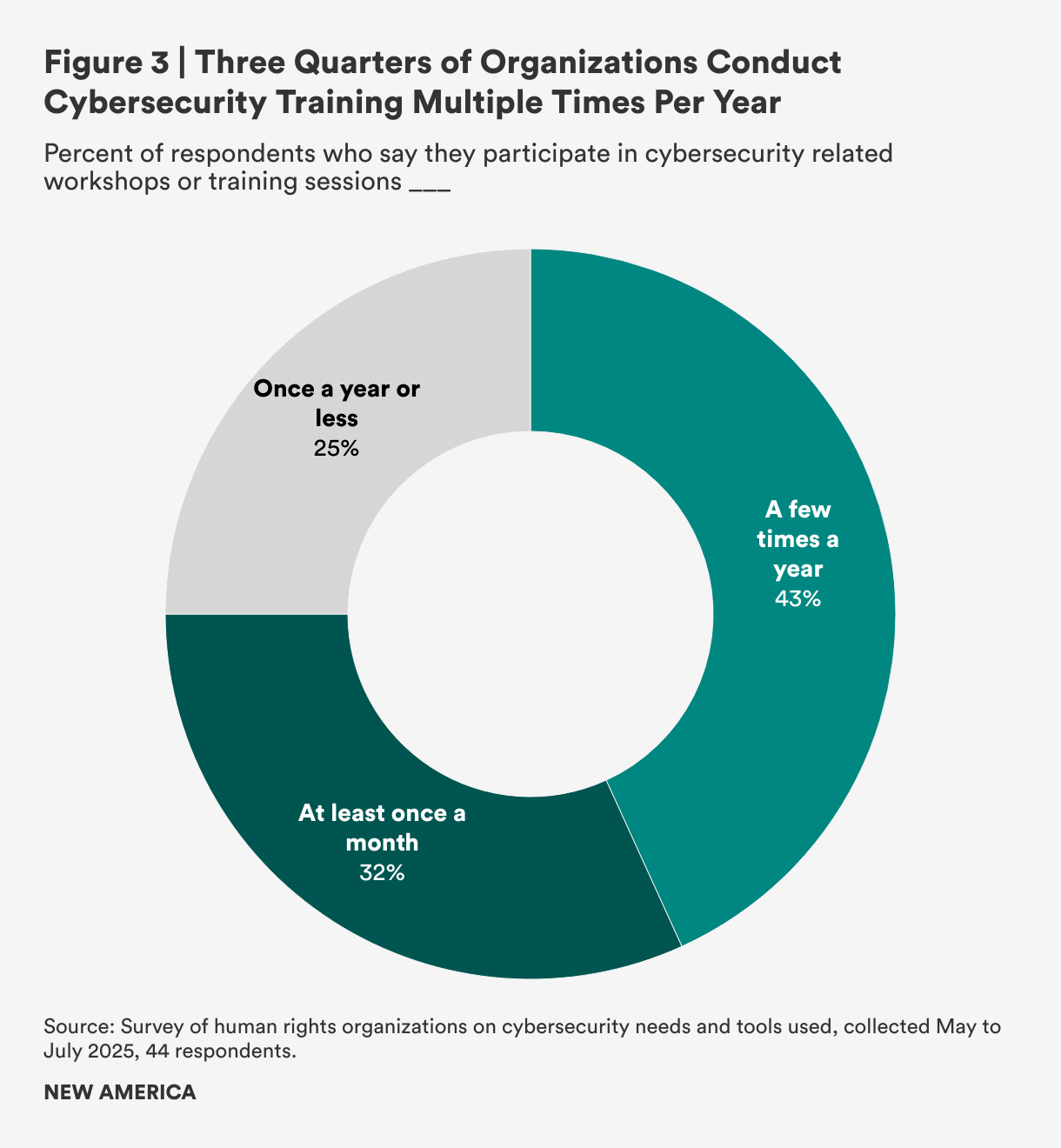
Although these data suggest that organizations generally feel well-prepared, training and preparation vary significantly. While three-fourths of organizations participate in training multiple times a year (32 percent of respondents report doing so at least once a month and 43 percent report doing so a few times a year), only 25 percent of organizations—a worrisomely small percentage—reported attending cybersecurity trainings once a year, at most (see Figure 3).
Tools and Discovery
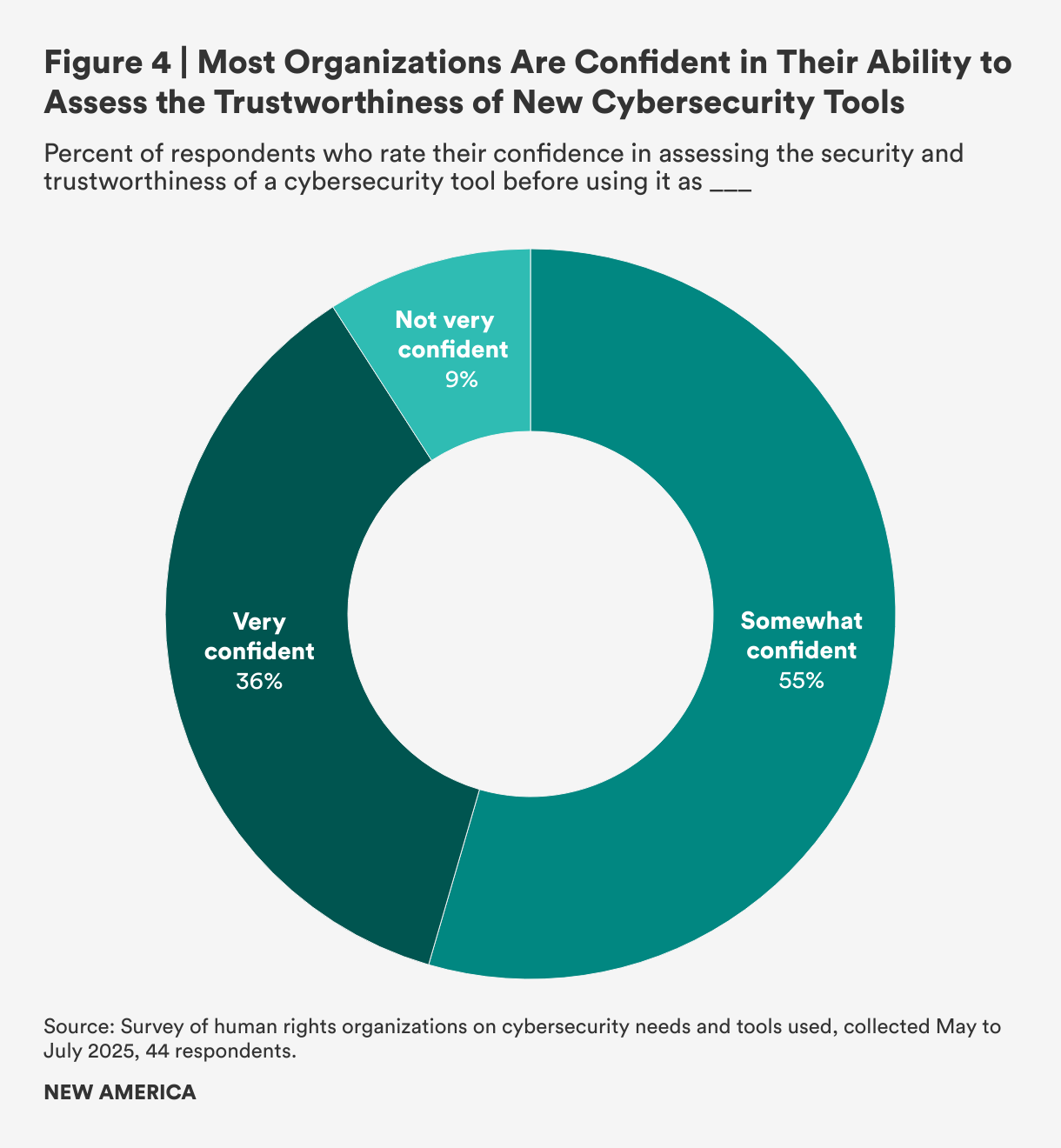
Participants were asked to assess their ability to evaluate the security and trustworthiness of new cybersecurity tools. As shown in Figure 4, a majority of respondents (55 percent) reported being “somewhat confident,” indicating they can make basic judgments but often rely on others. Additionally, a significant portion (36 percent) stated they were “very confident,” meaning they can evaluate tools independently and understand what to look for. The remaining 9 percent of respondents were “not very confident” and indicated that they usually depend on recommendations from trusted sources.
Organizations were asked to rate their motivations for seeking new cybersecurity tools on a scale of “1” (not at all motivating) to “5” (extremely motivating). The most significant factor was a proactive desire to improve current security practices, which 82 percent of organizations rated as a top motivation (a score of 4 or 5). While this illustrates a strategic focus on behalf of HRDs, urgent needs created by a recent security incident (rated 5 out of 5 by 45 percent of organizations) and the influence of partner recommendations (rated 4 out of 5 by 52 percent of organizations) are also important factors.
When evaluating a new tool, the top priority was trustworthiness, which 75 percent of organizations rated 5 out of 5. The next highest priority was that the tools must contain essential security features, such as end-to-end encryption and multi-factor authentication, which were rated 5 out of 5 by 68 percent of those surveyed. As a representative of one organization stated, “We evaluate the reputation of both the product and the company, including a review of their history and any negative press. As a general rule, we consider companies based in the U.S. or the EU to be more secure.”
When it comes to the decision-making process for selecting cybersecurity tools, the survey reveals that these choices are made at high levels within the organization. The IT team is the most frequently involved group at 46 percent of HRDs surveyed, with organizational leadership also being a key decision maker at 39 percent. The involvement of senior leadership highlights that cybersecurity is a priority, but their participation can also be driven by factors such as budget approval and risk management, and demonstrates the varied nature of these decisions.
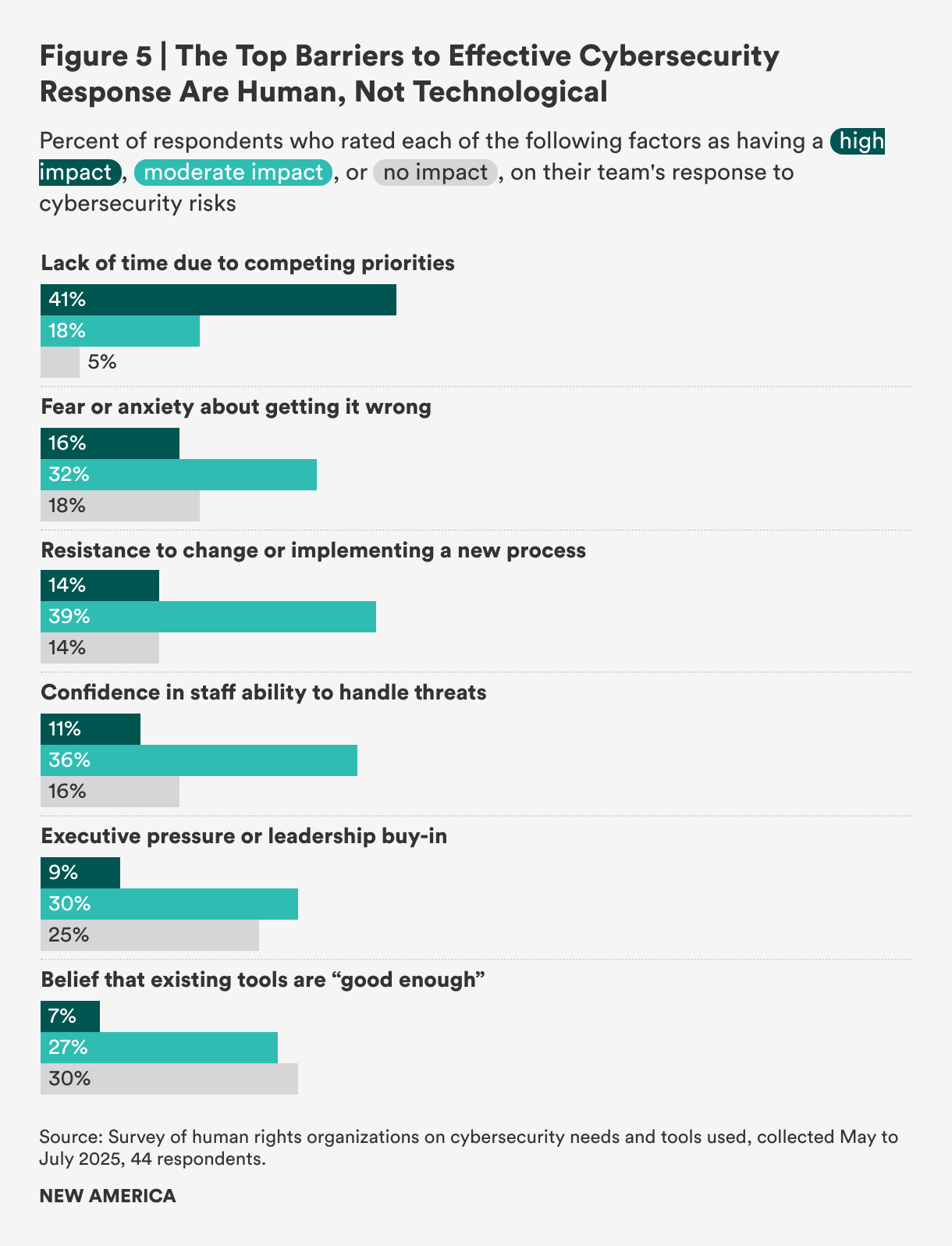
When asked to rate the top barriers to effective cybersecurity response, HRDs did not identify technology as the main obstacle, but rather institutional and human factors such as competing priorities and resistance to change. As shown in Figure 5, the most significant barrier was a “lack of time due to competing priorities,” which was rated as having a high impact by 41 percent of those surveyed. Additionally, “resistance to change or implementing a new process” was cited as having a moderate impact by 39 percent of the HRDs surveyed.
Put another way, more than half (56 percent) of organizations surveyed said they are willing to adopt new cybersecurity technologies, which strongly suggests that the primary challenges are not technological. Instead, the question of why they do not adopt new tools more frequently boils down to human and organizational friction that makes change difficult to effect. Specifically, the belief that current cybersecurity tools are “good enough” is not a major constraint on adopting new technology. This factor was indicated as having no impact by 29 percent of the organizations surveyed, and a moderate impact by another 27 percent, making it a minor barrier for the majority of respondents. As one respondent with a background in coding put it, “I feel comfortable using the tools themselves, but the harder process is actually change management within the organization and getting it rolled out to my team. That’s often the biggest piece that isn’t being considered by vendors, trainers, or folks writing resources online.”
Third-Party Support
For cybersecurity operations, many organizations use a hybrid approach, combining internal staff with external help. While some organizations manage all their security in-house, a significant number choose to outsource specific tasks. The survey found that 57 percent of HRDs prefer to hire a third-party company for functions such as threat monitoring, encryption management, and website security. In contrast, 43 percent of organizations surveyed prefer to handle these operations internally. This suggests that many organizations will strategically outsource resource-intensive tasks to external experts to fill a critical skills gap or improve efficiency. According to a regional cybersecurity provider interviewed for this report,
“Our own security posture is robust, which might make our responses to threats a bit unusual. But for us, managing our cybersecurity internally isn’t just a preference; it’s a critical operational decision that allows us to maintain the agility and deep control necessary to protect ourselves and, in turn, effectively protect the vulnerable organizations we serve in their daily struggles.”
When considering external support, organizations are most willing to outsource functions related to human capital and specific proactive security measures. The top function that organizations would outsource, according to 66 percent of HRDs surveyed, is staff training and awareness. This was followed by other critical areas, including proactive security measures such as threat detection and monitoring (57 percent) and incident response and recovery (also 57 percent). These data reveal a strategy in which HRDs prioritize outsourcing their “people problem” through staff training while delegating 24/7 security operations like detection and response to third-party cybersecurity providers. This approach allows organizations to focus on overall strategy while leveraging external groups for highly specialized tasks.
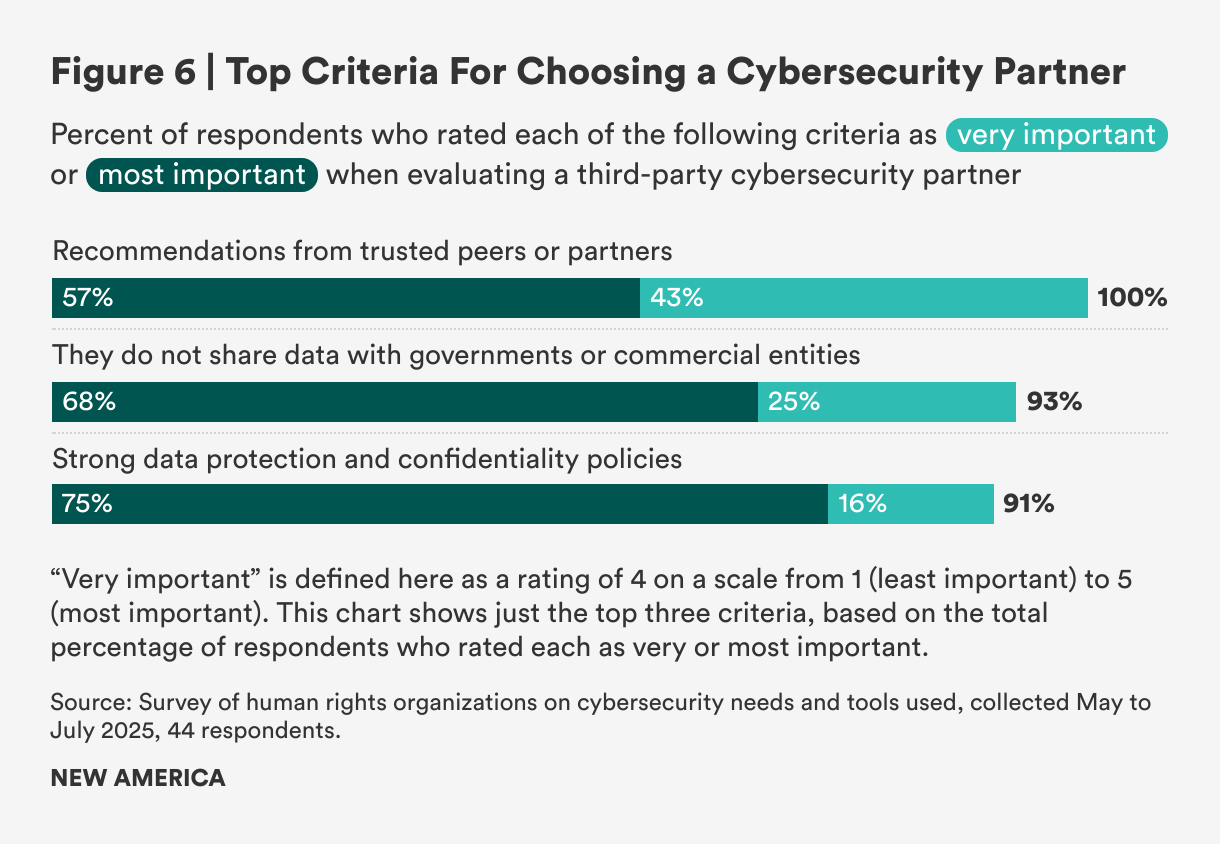
When evaluating third-party cybersecurity providers, trust and data governance are the most critical factors. As shown in Figure 6, the survey revealed that a strong data protection and confidentiality policy was rated “most important” by 75 percent of respondents, while a commitment to not share data with governments or commercial entities was similarly rated by 68 percent. This strong focus on data sovereignty is crucial because many HRDs view government entities as primary threat actors, making any data-sharing agreement a significant security vulnerability.
Beyond data policies, trust within peer networks was a universal theme. Every single respondent rated a recommendation from a trusted partner as highly important (a score of 4 or 5 on a scale of 1 to 5). In contrast, several factors were considered low priority, including the provider offering support in a local language or having nonprofit status, both of which 72 percent of organizations rated as unimportant (less than 3 on the scale).
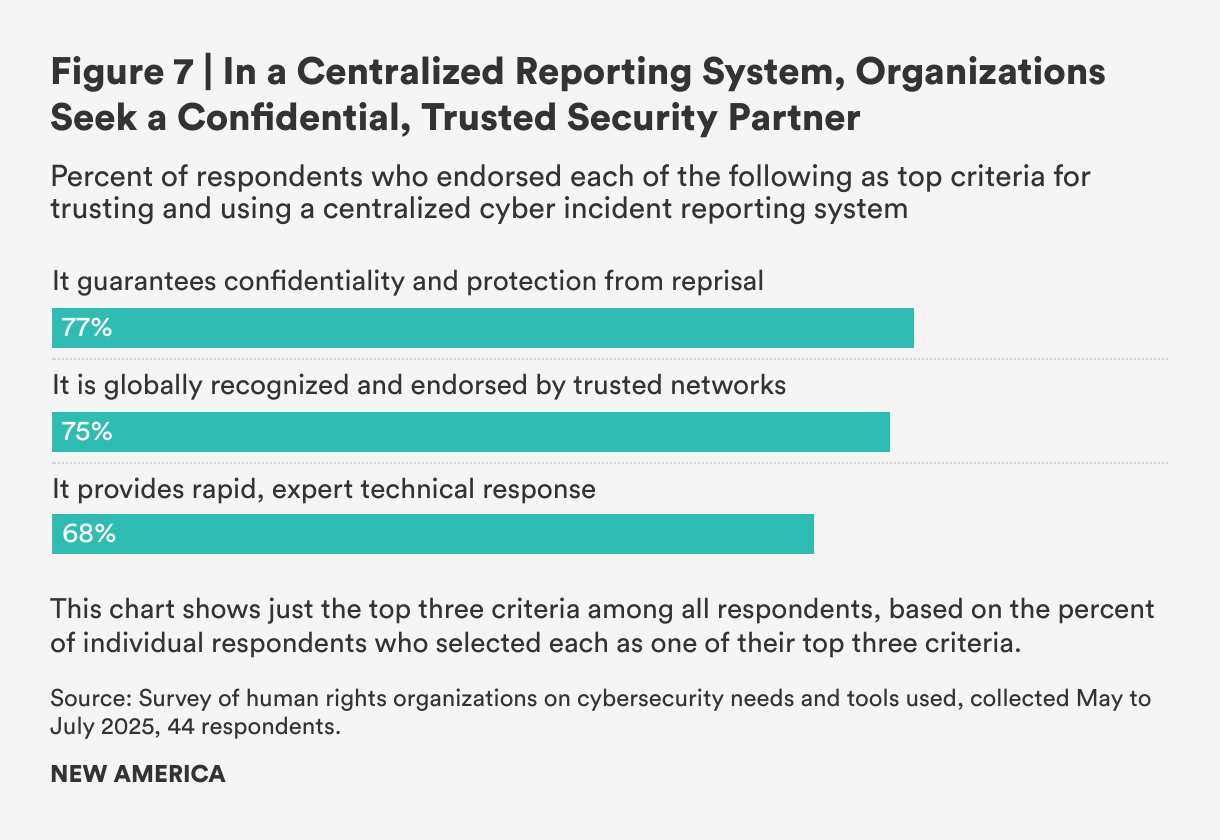
Although no single international reporting system currently exists where HRDs can report cyberattacks carried out against them, a strong majority—84 percent—would welcome such a system. However, their participation would be conditional on whether such a system met certain clear requirements—the most important being confidentiality guarantees and protection from reprisal, a condition cited by 77 percent of HRDs surveyed (see Figure 7).
It was also important to respondents that the system be recognized and endorsed by a trusted partner network (75 percent) and to provide rapid technical support and response (68 percent). As an investigative journalism organization based in Belarus put it,
“[The reporting system] doesn’t need to be globally recognized or backed by big organizations. What matters most is whether it has a strong reputation and is endorsed by people we trust in our community. For us, trust is everything. We know the biggest threats we face come from the government. We’ve seen how state actors launch attacks to silence us, block access to our work, and even compromise infrastructure. Any system we use has to guarantee real security and independence, otherwise it puts our journalists and sources at serious risk.”
Overall, these responses suggest that most HRDs would make use of a centralized threat sharing and cybersecurity organization, provided it is effective and can ensure appropriate privacy. Yet even in this arena, some HRDs would struggle with the human factors:
“If there were a trusted international system for reporting cyber incidents, would we use it? Honestly, I said no—not because we wouldn’t want to, but because we wouldn’t know how. There’s no clear guidance or training on what steps to take, and it feels like something only experts know how to navigate. If we understood the process and felt confident using it, then yes, we absolutely would.”
Cybersecurity Guidance
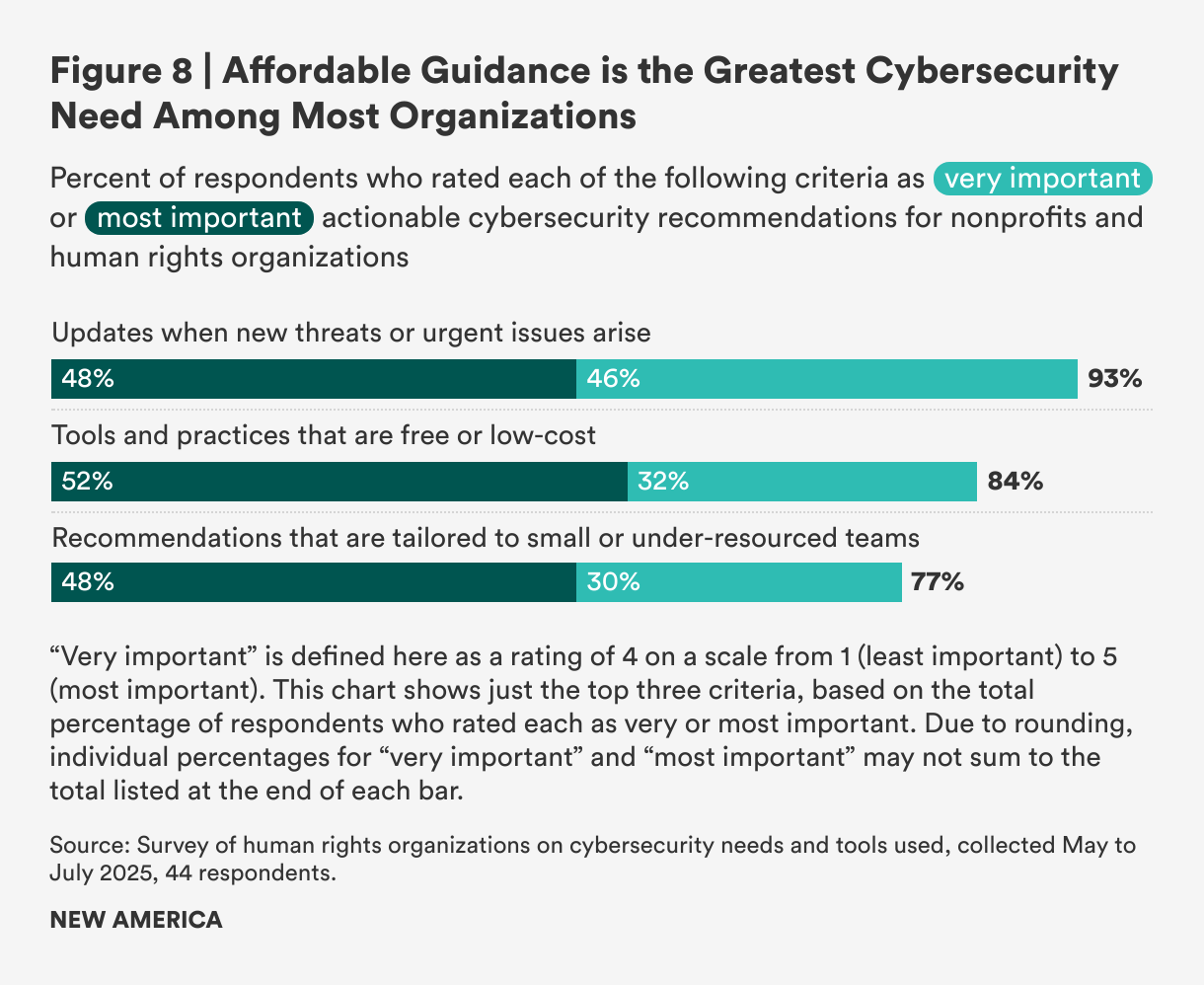
Organizations facing active threats with limited resources were asked to identify their top priorities for cybersecurity guidance. As illustrated in Figure 8, nearly all organizations (93 percent) responded that receiving updates on emerging threats was either a “very important” or the “most important” form of actionable cybersecurity guidance. This was followed by access to free or low-cost tools (84 percent) and recommendations tailored for small or under-resourced teams (77 percent). This data highlights a clear demand not only for complex security systems but for affordable partners providing guidance. As one respondent noted, “I’m often aware of general threats against organizations like ours, but the missing piece is always the practical response. The warnings tell me a threat exists, but they rarely provide clear steps on what my organization should do about it.”
In contrast, several aspects of cybersecurity guidance were considered less important. For instance, materials available in the organization’s local language were a low priority for 79 percent of organizations, and real-world case studies were assigned low importance by 61 percent of HRDs.
Despite background research showing low cybersecurity confidence among HRDs, a significant number of survey participants reported feeling highly confident in their cybersecurity management. This confidence, however, is not necessarily due to strong in-house technical skills. Instead, under-resourced teams strategically outsource critical security functions to trusted external partners. As a representative of the Fair Future Foundation, a volunteer-run humanitarian organization that provides medical care, clean water, and sanitation to remote Indonesian villages, said: “As a small medical NGO working in ultra-rural Indonesia, we operate under severe constraints with no reliable internet, very limited technical capacity, and high health risks. Cybersecurity is important for us, but often overshadowed by urgent health crises. Tailored, practical, low-cost solutions and clear guidance for low-resource settings are crucial.”
And yet, while this trust-based model can help HRDs feel secure, the fact that many remain “not sure” if they have been breached reveals a lack of internal visibility that could undermine their positive self-assessment. The high confidence can be a testament to the necessity of outsourcing rather than proof of their own technical strength.
Key Takeaways
Human Factors Can Be the Largest Hurdle for Organizations
The greatest barriers to cybersecurity are not technical; they are human. For 41 percent of organizations surveyed, a primary obstacle is a lack of time due to competing priorities. This issue is worsened by resistance to change, which 39 percent of organizations identified as a moderate barrier. The core challenge is also not a lack of effective tools—less than half of organizations (34 percent) stated that a shortage of “good enough” tools was a significant barrier—but rather the difficulty of integrating security practices into the demanding daily operations of human rights work.
Trust Is the Largest Theme in the Human Rights Space
Partnerships and trust drive security decisions, with all respondents citing a recommendation from a trusted partner as the most important factor in choosing a third-party cybersecurity provider. This emphasis on trust extends to data protection, with 75 percent of organizations prioritizing strong data governance and 68 percent requiring a commitment that data will not be shared with governments. This is a direct response to their primary threat actors, who 36 percent of organizations identified as government entities.
Human Rights Organizations Rely on External Cybersecurity Services
Human rights organizations rely heavily on external security capacity. Just over half (55 percent) of organizations surveyed said they were only “somewhat confident” in their ability to evaluate new security tools on their own; 46 percent admitted that they would be more vulnerable to threats without external training. These data suggest that their perceived strength comes from relying on external networks, not from internal self-sufficiency.
The Need for Practical Guidance
Organizations are more focused on getting actionable, immediate data on cyber threats than on theoretical guidance. Their most critical needs include timely updates on emerging threats (cited by 93 percent of organizations), access to free or low-cost tools (84 percent), and practical recommendations for small, under-resourced teams (77 percent). In contrast, less value is placed on time-intensive materials like real-world case studies, which 61 percent of organizations consider a low priority. This shows a clear preference for immediate, practical solutions.