Defending the Defenders: Building a Secure Digital Front Line for Human Rights Organizations
Abstract
This report examines the failures within the digital security support ecosystem for human rights defenders (HRDs). Despite existing efforts to protect these groups, the ecosystem remains fragmented and uncoordinated and leaves vulnerable communities exposed to digital threats. Based on an original survey of 44 human rights organizations, the report reveals that the primary cybersecurity challenges to HRDs are human factors, such as limited resources and a lack of practical guidance, not technical ones. The report provides a data-driven case for policy changes, calling for stakeholders to invest in a more resilient and coordinated support infrastructure.
Acknowledgments
This work would not have been possible without the leadership, guidance, and expertise in digital security for vulnerable communities provided by Patrick Day, Bridget Chan, Alissa Starzak, Lauren Zabierek, Andrew Ford Lyons, Ian Gottesman, James Eaton-Lee, Josh Levy, and Claudia Leon York. I am also especially grateful to the organizations and interviewees who participated in the survey, providing the essential perspective that grounds this research.
Editorial disclosure: The views expressed in this report are solely those of the author and do not reflect the views of New America, its staff, fellows, funders, or board of directors.
Downloads
Executive Summary
The ecosystem providing digital security support to human rights defenders (HRDs)—from journalists in conflict zones to organizations struggling to keep their websites online against cyberattacks—is broken.
Findings from an original survey of 44 human rights organizations included in this report illustrate these challenges. The report reveals that human factors, not technical ones, present the biggest cybersecurity challenges. Organizations rely heavily on trusted partners for security solutions and external support, highlighting a need for practical, actionable guidance over theoretical training. Despite investment and effort from civil society, governments, and the private sector, a fragmented approach and conflicting policies have left these vulnerable communities exposed to digital threats.
The report investigates the systemic failures that undermine effective protection of HRDs online and identifies three primary gaps in the current cybersecurity framework:
- Organizations prioritize their primary mission over cybersecurity. Due to extremely limited resources, small teams, and tight budgets, human rights organizations are forced to focus on their core mission while leaving cybersecurity as an afterthought. This issue has been made worse by events like the July 2025 closure of the U.S. Agency for International Development and the elimination of around $60 billion in global assistance, which included support for HRDs and their digital security initiatives.1
- Threat environments differ depending on region and area of work. Digital threats are specific to the context in which they occur, meaning there is no universal threat model that can serve all HRDs. For example, an activist in Brazil facing threats from paramilitary groups has a different threat model than an activist in China who is targeted by sophisticated state surveillance. Therefore, a single solution for everyone will not work for digital security and could even put HRDs at even greater risk.
- Global cybersecurity support systems are fragmented. The efforts of civil society, the private sector, and governments are often isolated and uncoordinated. Civil society organizations provide essential support but struggle with unreliable funding. Private sector companies offer help, but their products are often not designed for the unique threat landscape HRDs face, and some of these same companies contribute to those threats. Meanwhile, governments have contradictory policies—at times funding initiatives and tools while at other times expanding their own domestic surveillance powers.
The report highlights the real-world challenges faced by human rights defenders through firsthand accounts. These stories are critical for understanding HRDs’ experiences and provide much-needed evidence for illustrating systemic failures, building a data-driven case for policy changes, and helping preserve narratives and evidence that might otherwise be lost.
Citations
- Le Monde with AP, “Trump Slashes 90% of USAID Contracts, $60 Billion in Foreign Aid,” Le Monde, February 27, 2025, source.
The Digital Security Ecosystem for Human Rights Defenders
While many organizations have documented cyberattacks against human rights defenders (HRDs), these threats are nonetheless significantly underreported. This is largely due to the challenging and often dangerous nature of their work. The Office of the United Nations High Commissioner for Human Rights defines an HRD not by a specific profession but by their actions and the context in which they operate. As outlined in the Declaration on Human Rights Defenders, they are individuals and groups dedicated to advancing human rights and eliminating human rights violations. This broad definition, which includes a wide range of work and advocacy, makes it incredibly difficult to identify and analyze all of the cyberattacks against them. Compounding the problem, HRDs may have limited knowledge on how to report an incident or a legitimate fear of reprisal if they do. This underreporting makes it very difficult to understand the full scope of digital threats HRDs face.
Yet, while digital threats are hard to track, the physical risks faced by human rights defenders are well-documented and extreme. In a 2023 survey by the Kvinna till Kvinna Foundation, three-fourths of the 458 women human rights defenders surveyed reported being threatened or harassed because of their work promoting women’s rights.1 The foundation reported that almost one in four respondents had received death threats and 37 activists had survived attempted murders. A 2023 study by Front Line Defenders made clear the extreme risks faced by HRDs, documenting the deaths of 300 activists in 28 countries.2
Physical threats to HRDs have also moved into the digital world, including online abuse, surveillance, phishing attacks, malware infections, data breaches, and denial-of-service attacks. For example, Access Now’s Digital Security Helpline, which supports at-risk civil society members, received 3,709 requests for digital security help in 2023.3 Cybersecurity company Cloudflare blocked 108.9 billion cyber threats targeting organizations in human rights, journalism, and civil society—an average of nearly 325.2 million attacks per day over an 11-month period in 2024 and 2025.4 According to a 2024 report by the Center for News, Technology & Innovation, one in three journalists had been harassed or threatened in the past year. The report found that online abuse was a significant factor, with 78 percent of journalists who perceive themselves to be at “very high” risk reporting such abuse.5
This rest of this section identifies and discusses three key challenges human rights defenders face in protecting themselves from digital threats: (1) their prioritization of their primary mission over cybersecurity, (2) threat environments that differ dramatically depending on region and area of work, and (3) global cybersecurity support systems that are fragmented and uncoordinated.
1. Organizations Prioritize Their Primary Mission over Cybersecurity
Human rights defenders and small nonprofits often work with limited resources. While cybersecurity is becoming a priority across all sectors, these organizations face unique challenges due to small teams, budgets, and a focus on their core mission. A 2025 report by NetHope found that only 31 percent of nonprofits considered their cybersecurity budgets to be adequate. Additionally, only 17 percent of these organizations reported having a dedicated chief information security officer in 2025, further highlighting the significant staffing gaps.6
The consequences for organizations that lack the resources to invest in cybersecurity can be devastating, as illustrated by a Brazil-based media outlet focused on deforestation in the Amazon. The outlet consisted of just three staff members, each of whom wore multiple hats—as journalist, website manager, funding coordinator, and environmental advocate. In 2023, soon after the organization began referring to itself online as a feminist organization, the organization was hit with a protracted denial-of-service attack that took its website offline for a week. To restore access, the organization had to hire a tech firm at the cost of 5,000 Brazilian reals (about $900)—a significant portion of its annual operating expenses.7
The lack of investment also extends to crucial areas such as digital skills training. A 2018 report by Microsoft and NTEN found that 59 percent of nonprofits had not provided any cybersecurity training to their staff.8 This gap persists. A November 2024 report published by the Center for Long-Term Cybersecurity at the University of California at Berkeley found that 53 percent of San Francisco-based nonprofit organizations do not offer any type of cybersecurity awareness training.9 This is concerning, especially as the sector is rapidly adopting new technologies. (For example, as of 2025, 83 percent of organizations had acquired threat detection and response tools, up from about 70 percent in previous years.10) The president and CEO of a small nonprofit surveyed for this report noted that while cybersecurity had become essential for his organization’s work, choosing the right tools was difficult and resource-intensive. “For every application we use, there are at least three more we’ve heard of but can’t properly assess,” he said. “We have to think about cost, how long it will take to implement, whether we’ll need to train staff, and if the tool will still meet our needs six months from now. We’re often making decisions in the dark, unless we can get guidance from someone who really understands the threat landscape.”
The situation has become more uncertain following the Trump administration’s closure of the U.S. Agency for International Development (USAID) in July 2025. The shuttering of USAID resulted in the elimination of an estimated $150 million that directly funded journalism and media support, as well as funding for related digital rights and freedom of expression programs. This has had a devastating impact on crucial support systems, forcing digital security helplines and other services to shut down or reduce aid to at-risk groups. For example, Internews’s digital safety initiatives that were funded by the U.S. government were brought to a halt, leaving independent media organizations more exposed to digital threats.11 In addition, the 988 Suicide & Crisis Lifeline’s specialized services for LGBTQ+ youth were terminated, removing a vital resource for a vulnerable population.12
As a result, many nonprofits in high-risk areas have been disproportionately affected, particularly on the cybersecurity front. According to a survey conducted by the Tech Global Institute, 71 percent of digital rights organizations in “global majority” countries had scaled back programming in the first three months of 2025 due to funding challenges.13 In sub-Saharan Africa, according to an Internews report, the loss of U.S. government funding has affected programs across the region, including the Adisi Cameroun initiative in Cameroon, which has lost 80 percent of its funding for open data, digital rights, and journalist training. In countries such as Ethiopia and Zimbabwe, the same report states that media partners have had to cut up to 80 percent of their staff and reduce operations, further impacting media operations.14 This loss of direct funding and specialized security support leaves these organizations even more exposed to digital threats.
2. Threat Environments Differ Dramatically Depending on Region and Area of Work
Digital threats targeting human rights defenders are specific to the context in which they work, including the region and political landscape. This means there is no universal threat model that can serve all human rights defenders worldwide. Instead, security strategies must be uniquely tailored depending on the threats or perceived threats by the user, which makes providing protection and advice a challenge.
For example, an environmental activist in Brazil faces threats from a mix of actors, including paramilitary groups, corporate interests tied to environmental exploitation, and state-based actors who are opposed to the activists’ goals. A 2003 Global Witness analysis identifies the Amazon, where environmental and land rights activists are often targeted with violence and assassination attempts due to their work, as one of the most dangerous places in the world for activists.15 This is a different threat model from that faced by an activist in China, where the primary adversary is a highly technical state operation. The technical environments of these countries make the cyberattacks look different. For example, China maintains a closed internet system designed with state surveillance built in at the infrastructure level. As a result, activists there face constant challenges with tracking and surveillance and have limited access to tools such as virtual private networks. Freedom House cites the widespread use of surveillance networks and censorship to monitor and suppress criticism against the state as a rationale for maintaining China’s “not free” rating.16
The disparity in threat models creates a challenge for security professionals and organizations aiming to protect activists globally. One security strategy may be effective against physical threats in one region but could be inadequate in another. This forces organizations to develop and maintain multiple, specialized security protocols, which can be costly and can lead to security gaps. This approach can leave activists in certain regions exposed to threats that their security plan is not designed to handle.
Compounding these external threats is the inherent insecurity of the technology available to many human rights defenders. Due to limited resources, these groups often rely on consumer-grade or low-cost software that lacks robust security protections. Even when more secure tools exist, they might be unaffordable, as large software companies charge premium prices for enterprise versions with better protections. Even their discounted pricing schemes for nonprofits often leave crucial security features out of reach.
Furthermore, the principle of “secure by design”17—which mandates that security be a core component of a product from its inception—is rarely applied to tools accessible to the nonprofit sector. For example, many constituent relationship management systems and case management tools used by nonprofits lack the necessary security controls to protect sensitive data. This risk was highlighted by the 2020 Blackbaud ransomware attack, which compromised millions of donor records due to the failure to implement basic secure-by-design features such as multi-factor authentication.18 The inability of HRDs to acquire state-of-the-art cybersecurity protections—because of affordability or any other reason—leaves HRDs in a dangerous predicament in which the tools they rely on can actually increase their risk, resulting in sensitive information being stored on servers vulnerable to targeting or surveillance by an adversary.
3. Global Cybersecurity Support Systems Are Fragmented
The ecosystem surrounding the digital security of human rights defenders is an uncoordinated and complex landscape. This ecosystem is composed of a variety of actors—both those providing support and those posing threats—whose actions are often isolated from one another. While many of the efforts of specific support actors are effective, the lack of coordination prevents the formation of a unified safety net, leaving HRDs with significant protection gaps. There are three main actors that play large roles in providing cybersecurity support to HRDs: (1) civil society organizations, (2) private sector companies, and (3) governments.
The Role of Civil Society Organizations
Within the broader landscape of civil society, a subset of organizations provides essential digital security training, threat awareness, and advocacy on human rights issues worldwide. For example, Access Now operates a 24/7 Digital Security Helpline that has responded to thousands of incidents, offering direct emergency support to human rights defenders under attack. Organizations such as Global Cyber Alliance, CyberPeace Institute, and Common Good Cyber also provide crucial incident response services and resources to protect vulnerable groups.
However, beyond these well-known organizations, a less visible but highly critical ecosystem of specialized protection and rights groups provides direct, on-the-ground support to HRDs. This includes groups with a global footprint such as Open Briefing as well as region-specific groups like Digital Security Lab Ukraine and CyHub Armenia. These actors, along with prominent research and advocacy groups like Citizen Lab and Amnesty Tech, focus on the high-risk, direct work of defending activists, investigating cyberattacks, and providing targeted support.
Unfortunately, many of these efforts struggle to keep up with demand due to unreliable funding and a lack of scalable services. Many of these groups rely on short-term project grants that are often designated for set outcomes, such as training workshops or advocacy campaigns. This is compounded by a challenging funding model for human rights work, which has been compromised by cuts from major funders, including USAID. This funding model rarely covers the long-term, sustained costs of managing digital security infrastructure, staff salaries, or the development needed to build long-term solutions. As a result, these organizations are often in a constant state of fundraising and diverting resources from their mission to deal with costly cybersecurity needs, making it difficult for them to plan for the future. A 2024 study by the Institute for Voluntary Action Research found that 92 percent of the 1,241 charities surveyed identified better access to multiyear funding as a top priority.19
In addition, organizations that provide cybersecurity services to HRDs are frequently targeted themselves. For instance, in 2023, the International Press Institute (IPI) published a report on a series of coordinated denial-of-service attacks against more than 40 Hungarian media websites critical of Prime Minister Viktor Orbán’s government.20 After publishing the report, IPI itself was targeted by a denial-of-service attack that lasted several weeks and was responsible for taking down its website for multiple days.21
The Role of Private Sector Companies
In the last 10 years, a number of private sector companies have launched initiatives offering pro bono protection against cyberattacks or discounted access to technology services. These efforts are driven by a desire to help vulnerable communities but also strategic goals such as improving public relations, enhancing brand reputation, and identifying future commercial opportunities.
However, the technology and products offered are often not designed for the unique threats faced by HRDs and focus on protecting business data, not safeguarding individuals from cybersecurity threats such as data exfiltration or surveillance. A typical corporate security model focuses on protecting business data and infrastructure from financial and operational threats, whereas the threat model for a human rights defender is about safeguarding an individual from state-sponsored surveillance and other sophisticated attacks. This distinction is critical because tools built for corporate needs often fail to protect against tactics most frequently deployed against individual HRDs.22
Even when companies offer free services, organizations may be hesitant to use them if they are required to turn over sensitive personal information to gain access. This is because governments can legally compel technology companies to produce user data under local law, often citing law enforcement or national security concerns. Cloudflare highlighted this trade-off in its comment on a proposed Commerce Department “Know Your Customer” rule, arguing that such broad data collection would not stop malicious actors but would instead “meaningfully restrict access to necessary services for those who most need them.”23
In some cases, businesses are actually compounding the threats faced by HRDs by selling sophisticated surveillance technology to governments. This has given rise to a largely unregulated surveillance-for-hire industry. Companies such as Israel’s NSO Group and Germany’s Finfisher have reportedly sold spyware to governments with an established track record of abuse against civil society organizations. For example, NSO Group exploited a WhatsApp vulnerability in 2019 to install spyware on the phones of HRDs via a simple missed call.24 In 2023, a joint investigation reported that the Mexican military used NSO Group’s Pegasus software to spy on human rights defender Raymundo Ramos and his communication with journalists.25 Operating with little oversight and often hiding behind national security policies, these firms make it nearly impossible for victims to seek accountability for the resulting human rights violations. In response to the growing use of commercial spyware, the Biden administration in 2023 issued an executive order prohibiting U.S. government agencies from using commercial spyware that has been misused to target activists and journalists.26
The Role of Government
The role of governments in protecting HRDs online is filled with contradictions. On one hand, a number of democratic governments have established crucial support systems. For example, the Freedom Online Coalition brings together 42 countries to diplomatically oppose internet shutdowns and censorship. The Open Technology Fund continues to provide essential grants for privacy-enhancing communication tools like Signal and Tor, despite facing funding freezes and legal disputes from the Trump administration. Nations such as Canada, the Netherlands, and Norway consistently provide financial support for NGOs that offer emergency assistance and digital security training.27
However, this support is often at odds with domestic politics and geopolitical priorities. For many HRDs, the government is not a potential partner but a primary threat actor. This is evident in the case of Rose Njeri, the Kenyan software developer who was arrested in May 2025 for creating a website to facilitate public opposition to a controversial finance bill. Her arrest, and a broader government crackdown that led to at least 60 deaths and over 2,000 arrests, illustrates the state’s role as a potential adversary.28 In June 2025, a Citizen Lab report detailed a Russian government-linked social engineering campaign that bypassed two-factor authentication to target activists.29
Even within the nations that support human rights online, internal contradictions are common: A government may fund privacy tools with one hand while expanding its own domestic surveillance powers with the other. For example, the United Kingdom is a member of the Freedom Online Coalition, but in 2016 it passed a law—the Investigatory Powers Act—that has been criticized by Amnesty International for legalizing bulk data collection.30 In France, the government advocates for digital rights internationally but has repeatedly expanded its domestic surveillance laws with powers that Human Rights Watch warns could be used to target activists.31
The United States also exemplifies these competing priorities, showcasing the shifts that can happen within a democratic country with a change in administration. While the Cybersecurity and Infrastructure Security Agency launched the Joint Cyber Defense Collaborative, an initiative to defend high-risk communities, the effort has been undermined by the shifting political agenda of the Trump administration. And while the Biden administration elevated the issue of internet freedom and digital rights, in 2025 the Trump administration has scaled back the State Department’s annual human rights reports; reduced staff for the Bureau of Democracy, Human Rights, and Labor; and rolled back funding for the civil society space.32
This kind of ambivalence is also evident at the international level. Without effective international cooperation and with conflicting policies among democratic nations and pressure from authoritarian countries, coordinated global support for these groups remains lacking. As a result, the response remains ad hoc, leaving groups to struggle with a complex and often contradictory set of priorities.
Citations
- Kvinna till Kvinna Foundation, Hope and Resistance Go Together: The State of Women Human Rights Defenders 2023 (Kvinna till Kvinna Foundation, 2023), source.
- Front Line Defenders, Global Analysis 2023/24 (Front Line Defenders, 2023), source.
- Luis Barrueto, “Visualizing the Digital Security Helpline’s Recent Impact,” Access Now, April 25, 2024, source.
- “Project Galileo 11th Anniversary,” Cloudflare, July 12, 2025, source.
- Jay Barchas-Lichtenstein et al., What It Means to Do Journalism in the Age of AI: Journalist Views on Safety, Technology, and Government (Center for News, Technology & Innovation, March 2025), source.
- NetHope, 2025 State of Humanitarian and Development Cybersecurity Report (NetHope, 2025), source.
- Interview with feminist activist at Access Now Rightscon, June 4, 2023.
- Afrua Bruce, Cybersecurity for Nonprofits: A Guide (NTEN and Microsoft, February 2020), source.
- Sarah Powazek and Shannon Pierson, CyberCAN: Cybersecurity for Cities and Nonprofits (Center for Long-Term Cybersecurity at UC Berkeley, November 2024), source.
- NetHope, 2025 State of Humanitarian and Development Cybersecurity Report, 25, source.
- Internews, Crisis in Journalism: The Impact of U.S. Government Funding Cuts on Global Media (Internews, 2025), source.
- Trevor News, “Closed: Trump Admin Officially Shuts Down the 988 Suicide & Crisis Lifeline's LGBTQ+ Youth Specialized Services,” The Trevor Project, July 17, 2025, source.
- “The Impact of Funding Freezes on Internet Freedom in the Global Majority,” Tech Global Institute, source.
- Internews, Crisis in Journalism, source.
- “Almost 2,000 Land and Environmental Defenders Killed Between 2012 and 2022,” Global Witness, September 13, 2023, source.
- “Freedom on the Net 2024: China, Key Developments, June 1, 2023–May 31, 2024,” Freedom House, source.
- “Secure by Design,” Cybersecurity and Infrastructure Security Agency, source.
- “Blackbaud Security Incident,” Oregon Tech Foundation, source.
- Chris Mills, Liz Firth, and Ben Cairns, Time to End the Dominance of Short-Term Grants: The Evidence for Multi-Year Funding (Institute for Voluntary Action Research, 2023), source.
- “DDoS Attacks Traced to Proxy Infrastructure: White Proxies,” Qurium, November 2, 2023, source.
- International Press Institute, “Hungary: Police Arrest Suspect Behind DDoS Cyberattacks on IPI and Independent Media Websites,” Media Freedom Rapid Response, July 22, 2025, source.
- A substantial majority of HRDs surveyed in the Congo, Kenya, Senegal, and Zimbabwe—85 percent—feel their work is negatively impacted by their political environment, with a large majority (65 percent) believing they are specifically under surveillance by their state. See Tomiwa Ilori, Use of Digital Security Tools by Human Rights Defenders in African Contexts: Lessons from the Democratic Republic of the Congo, Kenya, Senegal, and Zimbabwe (Open Technology Fund, July 2025), source.
- Cloudflare, Inc., “Comments of Cloudflare, Inc. on Proposed Rulemaking for Information and Communications Technology and Services Supply Chain Rule to Address Foreign Adversary Concerns,” submitted to the U.S. Department of Commerce, May 27, 2021, 5, source.
- “NSO Group Tools Abused WhatsApp to Target Human Rights Defenders with Invasive Spyware,” Amnesty International, October 21, 2019, source.
- “Mexico: Pegasus Spyware Used on Journalists and Citizens,” PEN International, June 28, 2023, source.
- “Fact Sheet: President Biden Signs Executive Order to Prohibit U.S. Government Use of Commercial Spyware That Poses Risks to National Security,” White House, March 27, 2023, source.
- “Minister Joly Announces Support for Digital Security of Human Rights Defenders,” Global Affairs Canada, February 2, 2025, source; “New Civil Society Fund Launched by Iceland, Liechtenstein, and Norway: An Unprecedented Commitment to Strengthen Democracy and Human Rights in Europe,” EEA and Norway Grants, November 20, 2024, source.
- “Monthly Newsletter: Updates from May 2025,” DefendDefenders, May 25, 2025, source.
- John Scott-Railton, Rebekah Brown, and Bill Marczak, “Same Sea, New Phish: Russian Government-Linked Social Engineering Targets App-Specific Passwords,” Citizen Lab at the Munk School of Global Affairs & Public Policy, University of Toronto, June 18, 2025, source.
- Rachel Logan and Joshua Franco, “Why We’re Challenging the U.K.’s Surveillance Laws in Court Today,” Amnesty International, November 7, 2017, source.
- Elvire Fondacci, “French MPs Approve Controversial Surveillance Tech Under Olympics Pretext,” Human Rights Watch, March 29, 2023, source.
- Jason Pielemeier, “Reinvigorating Internet Policy: Doubling Down on Human Rights,” Council on Foreign Relations, February 20, 2021, source; Graham Smith, “The State Department Is Changing Its Mind About What It Calls Human Rights,” NPR, April 18, 2025, source.
How Human Rights Organizations Assess Their Cybersecurity and Select Tools: Survey Findings
This report draws on insights gathered from an original survey, conducted from May to July 2025, to evaluate the cybersecurity needs of and tools used by human rights organizations. The survey was designed to document organizational practices, decision-making factors, and perceived challenges related to cybersecurity. For details on survey methodology, see the Appendix.
The goal of the survey was to understand how human rights defenders (HRDs) evaluate their cybersecurity posture and threat landscape. To do this, the survey was designed to provide a deeper, more personal understanding of these trends, giving voice to the lived experiences of those working on the front lines. The survey aimed to identify the factors influencing HRDs’ cybersecurity decisions, particularly on how they balance security requirements against activities that directly support their organizations’ primary mission.
In total, representatives from 44 civil society organizations participated in the study, including groups working in human rights and journalism. Participants held positions such as chief executive officer, chief operations officer, network security engineer, and editor. Many participants held multiple roles within their organizations, which is common in grassroots organizations. Respondents were given the option to remain anonymous.
The following sections present the key findings of the survey and include insights from follow-up interviews with select participants.
Overview of Survey Respondents
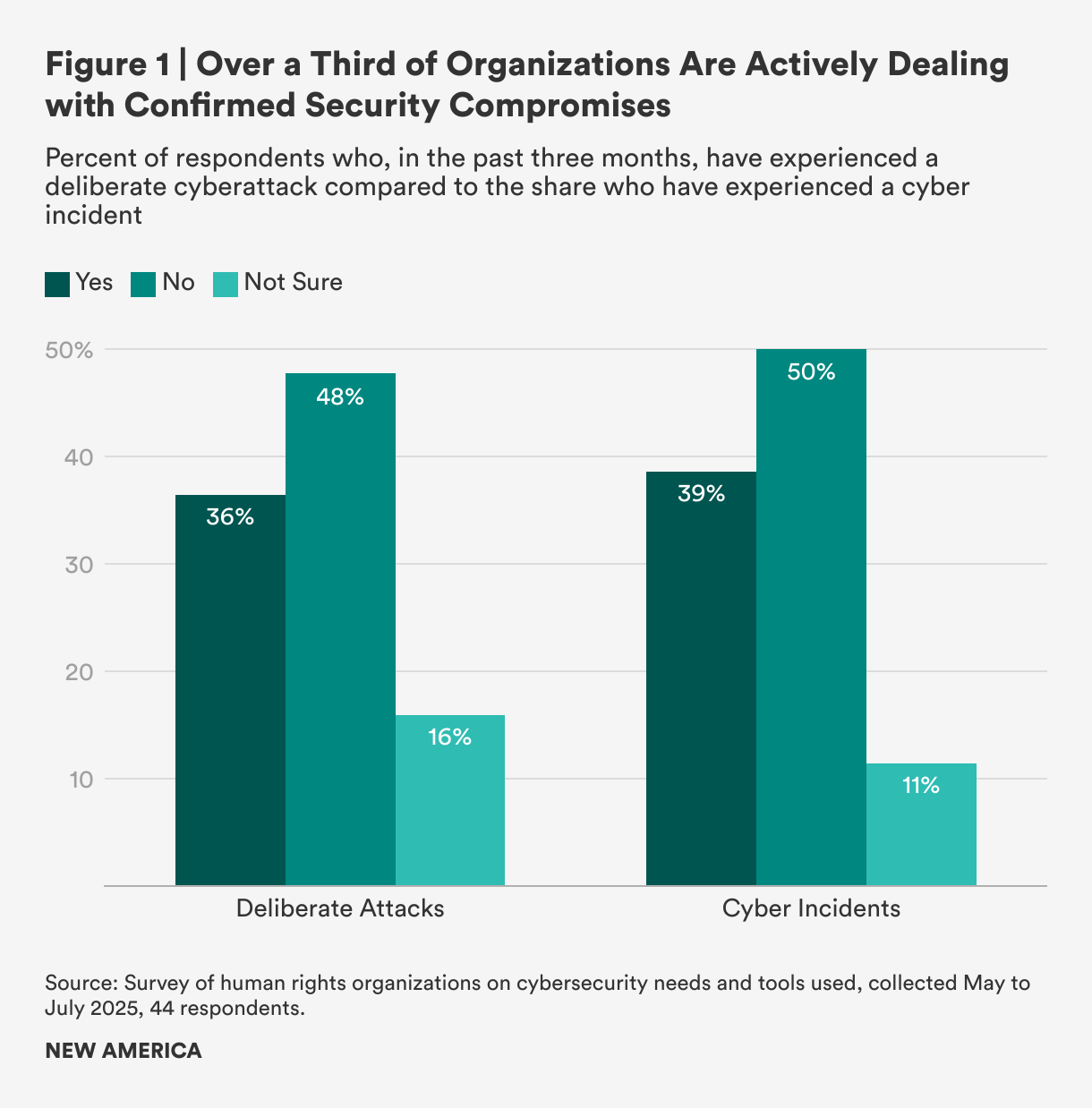
Many of the organizations interviewed had a global footprint with operations on multiple continents. The survey reveals a pattern of security threats facing these organizations. When asked specifically about successful, deliberate cyberattacks (such as ransomware or phishing attacks), 36 percent of organizations said they had been targeted; 48 percent reported they had not been targeted; and the remaining 16 percent were not sure (see Figure 1). This means that a majority of organizations—52 percent—are operating with either a confirmed compromise or a dangerous lack of certainty. This uncertainty poses its own risk: It makes it difficult for organizations to properly manage a compromise, leaving them vulnerable to further attacks and hindering their ability to implement effective security protocols.
When the question was broadened to cover any type of cybersecurity incident, 39 percent of respondents said they had experienced an incident such as a data breach and insider threats (that is, malicious or unintentional misuse of sensitive data or systems by someone with authorized access, like a staff member, volunteer, or trustee). The number of organizations reporting no incidents rose to 50 percent, up from 48 percent for external attacks alone. This suggests that many of those previously “unsure” were more confident they had not been breached by an internal threat (a cyber incident) or external threat (a deliberate attack). For clarity, external threats are deliberate attacks originating outside the organization (for example, malware, phishing, denial-of-service), while internal threats are cyber incidents originating inside the organization (e.g., accidental data leaks, misuse by staff, or compromised insider credentials). The key takeaway remains the same, however: Over a third of organizations are actively managing confirmed security compromises.
Organizations reported facing severe and organized cyber threats from three main types of actors. Government actors were identified as the primary threat by 36 percent of organizations, while cybercriminal groups were cited by 30 percent. Additionally, about 25 percent of organizations identified political or ideological groups as their main threat. Together, these three categories account for over 90 percent of all primary threats, showing that organizations are overwhelmingly targeted by sophisticated groups with clear financial, political, or ideological motives.
A respondent for a Ukrainian civil society organization makes it clear how sophisticated the adversaries are:
“We are constantly navigating a landscape of sophisticated digital threats. For us, a significant concern is malware delivered through well-crafted files sent by fake whistleblowers, a tactic that preys on the trust essential to our work with journalists. The danger is magnified by internal security gaps; a lack of consistent malware education or the absence of a corporate antivirus solution can leave our entire network vulnerable. The stakes are incredibly high, [as] a single compromised device could lead to the imprisonment of our contacts and sources. We see clear evidence that the same military-grade cyber-espionage tools used by state actors, like Lukashenka’s regime [in Belarus] against the Ukrainian military, are the same ones now being turned on us as journalists and activists, which underscores the severity of the threats we face.”
Furthermore, as a respondent for an organization supporting journalists in Eastern Europe noted, sophisticated state actors are able to prey on the specific vulnerabilities of HRDs:
“We recently assisted a Belarusian organization that was targeted by a sophisticated FSB phishing attack in 2024. The attack was successful because they had not yet implemented phishing-resistant two-factor authentication. Our role was to help them analyze the breach, identify the compromised data, and alert their people on the ground who faced potential criminal prosecution and needed to evacuate. To help prevent these incidents, we now work with organizations to receive and configure FIDO2/U2F security keys, like those from Yubico and Google, which provide the necessary protection against these advanced threats.”
Cybersecurity Capacity
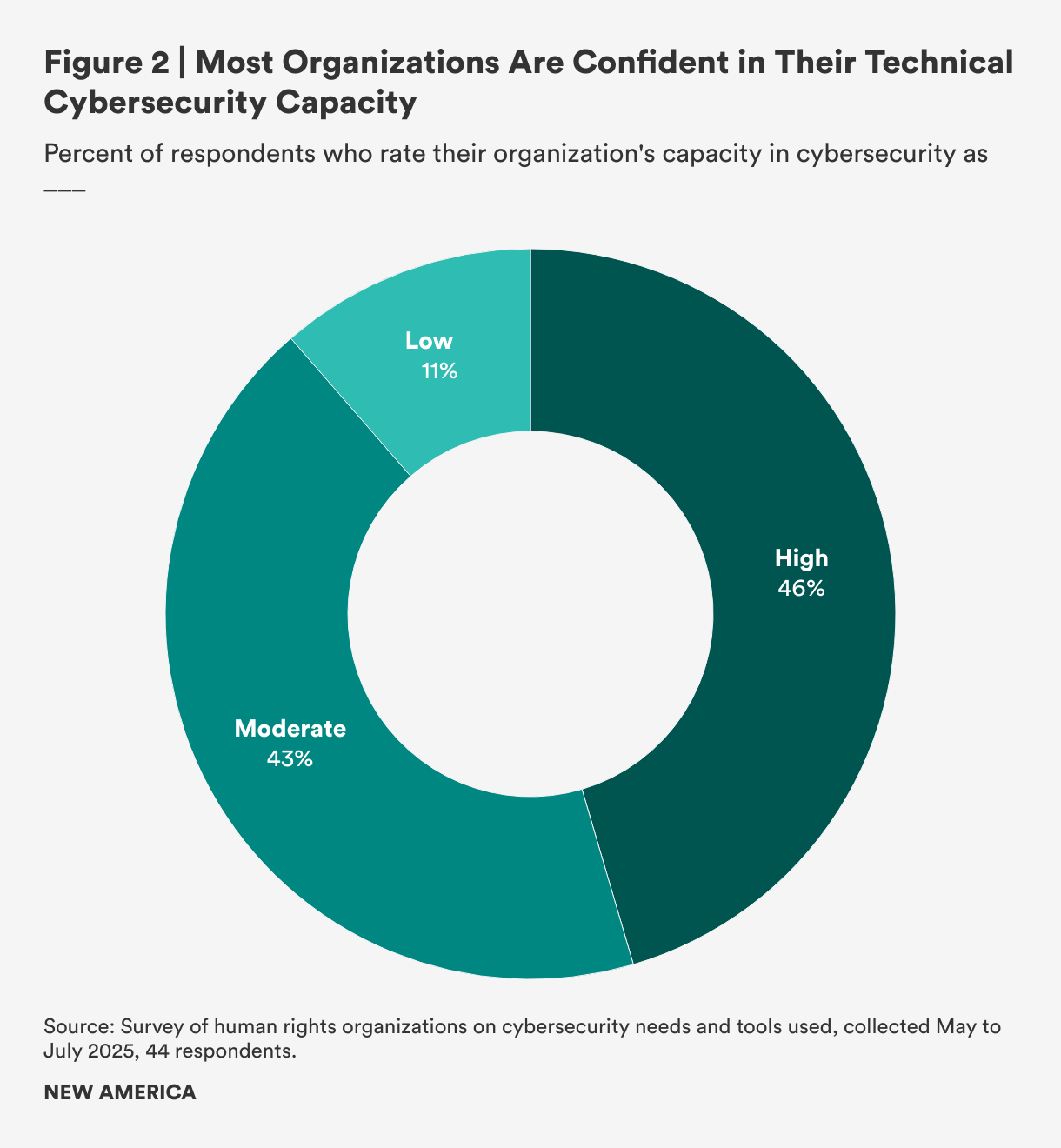
The survey reveals that organizations generally feel confident in their cybersecurity management, with none reporting “very low” capacity. Nearly half (46 percent) of the organizations rated their capacity as “high,” meaning they have dedicated staff who proactively manage their cybersecurity (see Figure 2). Another large group (43 percent) described their capacity as “moderate,” with enough technical knowledge to handle their security needs, while the remainder (11 percent) reported “low” capacity, signifying a heavy reliance on external support or struggles with internal management.
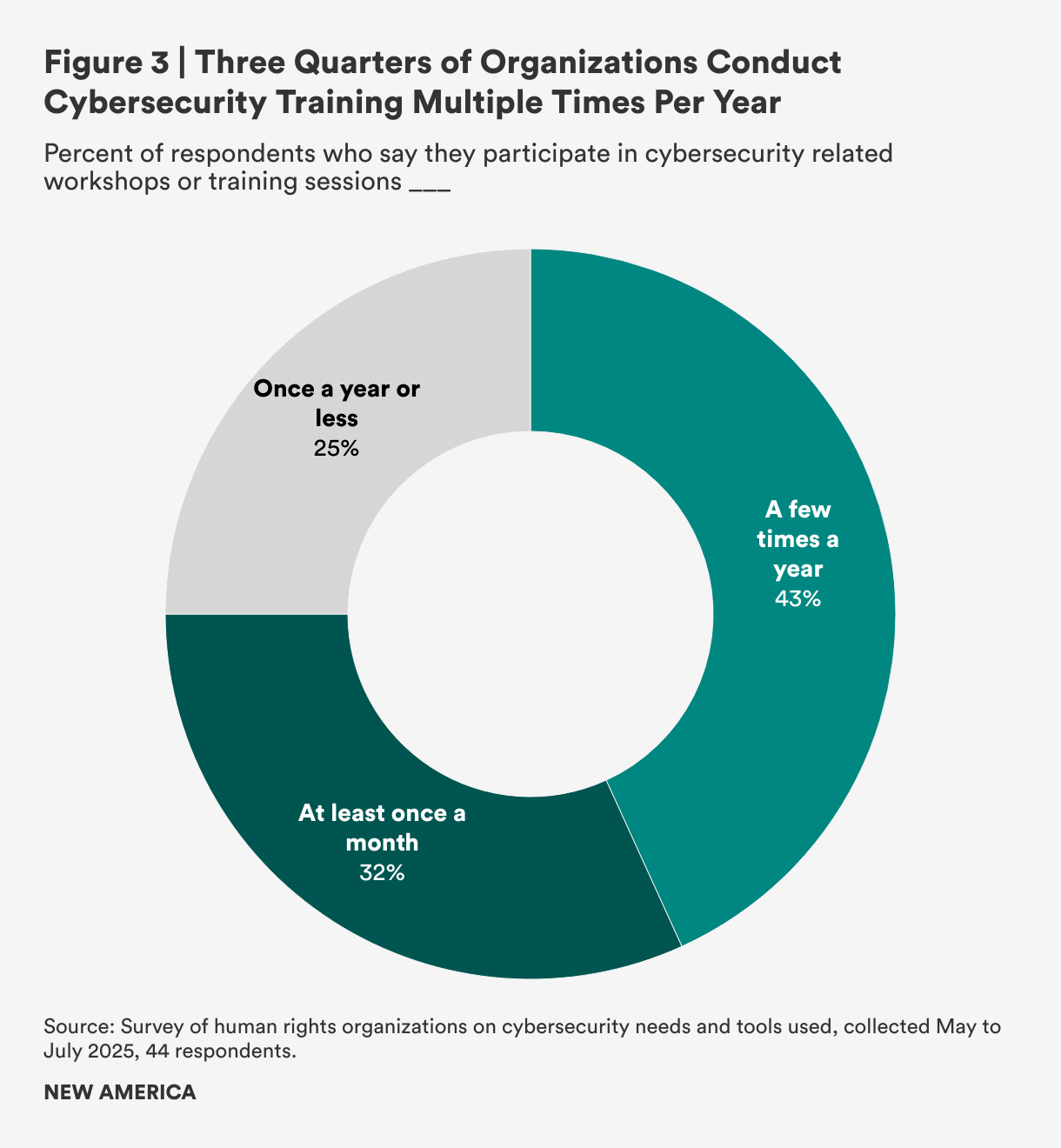
Although these data suggest that organizations generally feel well-prepared, training and preparation vary significantly. While three-fourths of organizations participate in training multiple times a year (32 percent of respondents report doing so at least once a month and 43 percent report doing so a few times a year), only 25 percent of organizations—a worrisomely small percentage—reported attending cybersecurity trainings once a year, at most (see Figure 3).
Tools and Discovery
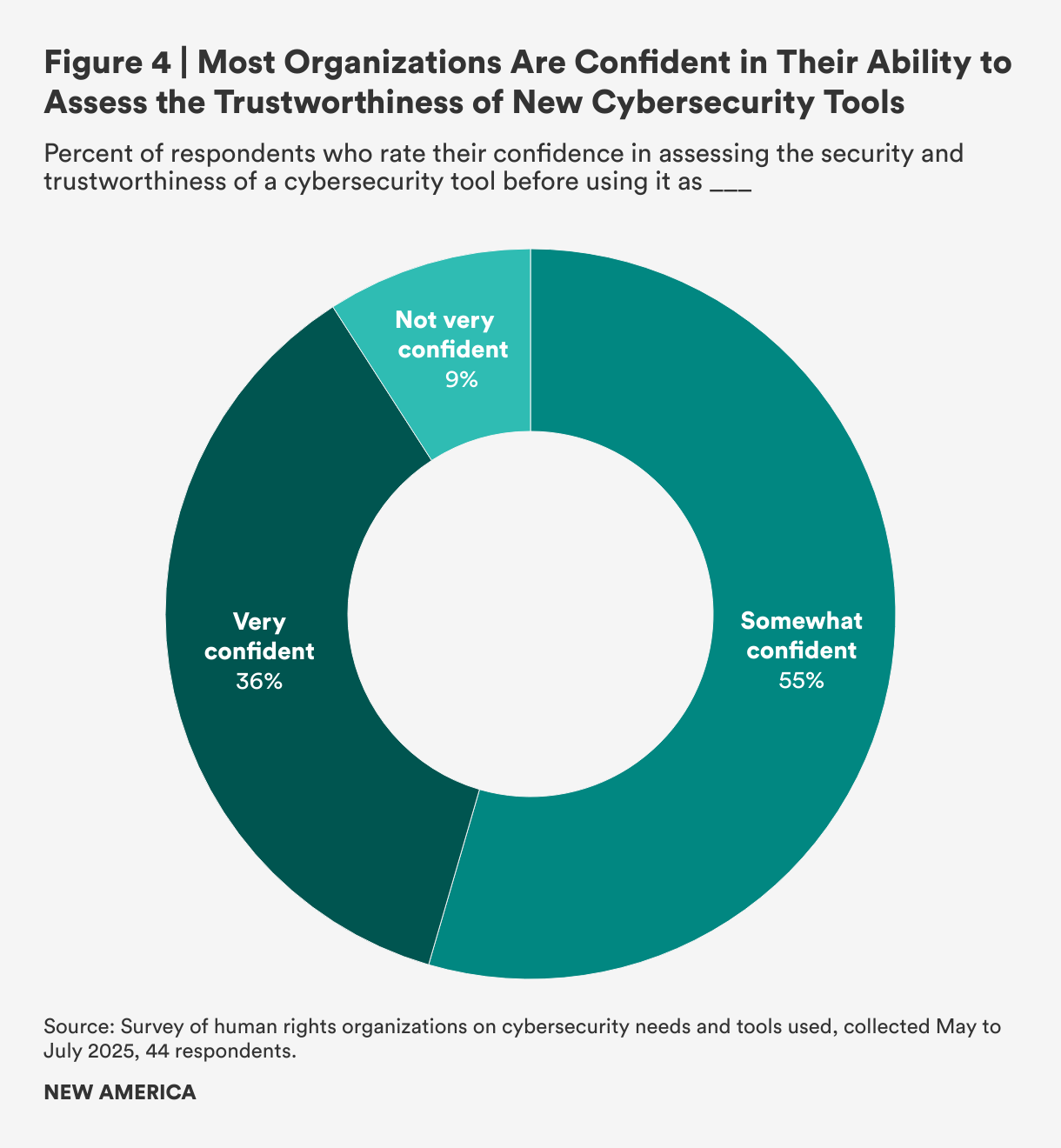
Participants were asked to assess their ability to evaluate the security and trustworthiness of new cybersecurity tools. As shown in Figure 4, a majority of respondents (55 percent) reported being “somewhat confident,” indicating they can make basic judgments but often rely on others. Additionally, a significant portion (36 percent) stated they were “very confident,” meaning they can evaluate tools independently and understand what to look for. The remaining 9 percent of respondents were “not very confident” and indicated that they usually depend on recommendations from trusted sources.
Organizations were asked to rate their motivations for seeking new cybersecurity tools on a scale of “1” (not at all motivating) to “5” (extremely motivating). The most significant factor was a proactive desire to improve current security practices, which 82 percent of organizations rated as a top motivation (a score of 4 or 5). While this illustrates a strategic focus on behalf of HRDs, urgent needs created by a recent security incident (rated 5 out of 5 by 45 percent of organizations) and the influence of partner recommendations (rated 4 out of 5 by 52 percent of organizations) are also important factors.
When evaluating a new tool, the top priority was trustworthiness, which 75 percent of organizations rated 5 out of 5. The next highest priority was that the tools must contain essential security features, such as end-to-end encryption and multi-factor authentication, which were rated 5 out of 5 by 68 percent of those surveyed. As a representative of one organization stated, “We evaluate the reputation of both the product and the company, including a review of their history and any negative press. As a general rule, we consider companies based in the U.S. or the EU to be more secure.”
When it comes to the decision-making process for selecting cybersecurity tools, the survey reveals that these choices are made at high levels within the organization. The IT team is the most frequently involved group at 46 percent of HRDs surveyed, with organizational leadership also being a key decision maker at 39 percent. The involvement of senior leadership highlights that cybersecurity is a priority, but their participation can also be driven by factors such as budget approval and risk management, and demonstrates the varied nature of these decisions.
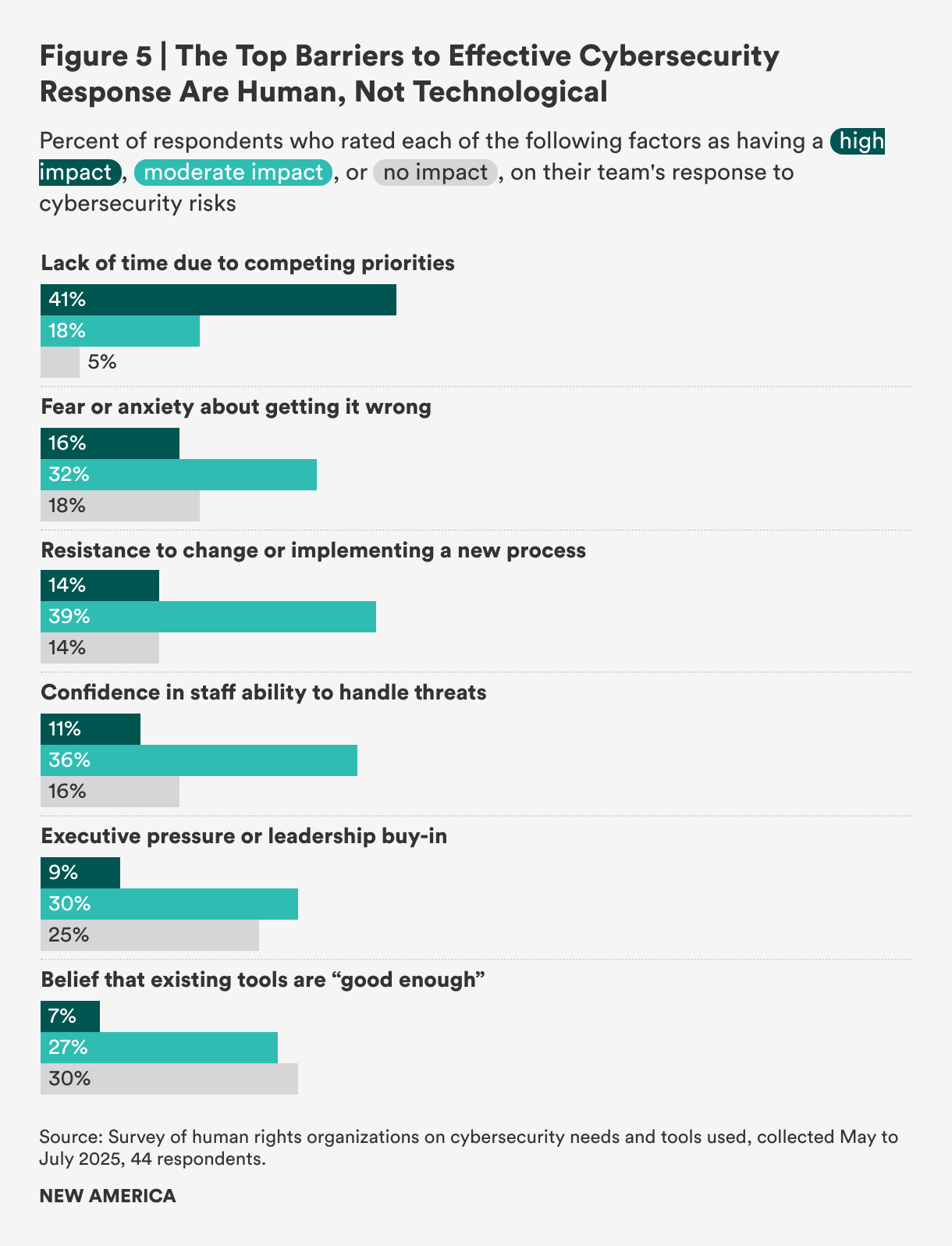
When asked to rate the top barriers to effective cybersecurity response, HRDs did not identify technology as the main obstacle, but rather institutional and human factors such as competing priorities and resistance to change. As shown in Figure 5, the most significant barrier was a “lack of time due to competing priorities,” which was rated as having a high impact by 41 percent of those surveyed. Additionally, “resistance to change or implementing a new process” was cited as having a moderate impact by 39 percent of the HRDs surveyed.
Put another way, more than half (56 percent) of organizations surveyed said they are willing to adopt new cybersecurity technologies, which strongly suggests that the primary challenges are not technological. Instead, the question of why they do not adopt new tools more frequently boils down to human and organizational friction that makes change difficult to effect. Specifically, the belief that current cybersecurity tools are “good enough” is not a major constraint on adopting new technology. This factor was indicated as having no impact by 29 percent of the organizations surveyed, and a moderate impact by another 27 percent, making it a minor barrier for the majority of respondents. As one respondent with a background in coding put it, “I feel comfortable using the tools themselves, but the harder process is actually change management within the organization and getting it rolled out to my team. That’s often the biggest piece that isn’t being considered by vendors, trainers, or folks writing resources online.”
Third-Party Support
For cybersecurity operations, many organizations use a hybrid approach, combining internal staff with external help. While some organizations manage all their security in-house, a significant number choose to outsource specific tasks. The survey found that 57 percent of HRDs prefer to hire a third-party company for functions such as threat monitoring, encryption management, and website security. In contrast, 43 percent of organizations surveyed prefer to handle these operations internally. This suggests that many organizations will strategically outsource resource-intensive tasks to external experts to fill a critical skills gap or improve efficiency. According to a regional cybersecurity provider interviewed for this report,
“Our own security posture is robust, which might make our responses to threats a bit unusual. But for us, managing our cybersecurity internally isn’t just a preference; it’s a critical operational decision that allows us to maintain the agility and deep control necessary to protect ourselves and, in turn, effectively protect the vulnerable organizations we serve in their daily struggles.”
When considering external support, organizations are most willing to outsource functions related to human capital and specific proactive security measures. The top function that organizations would outsource, according to 66 percent of HRDs surveyed, is staff training and awareness. This was followed by other critical areas, including proactive security measures such as threat detection and monitoring (57 percent) and incident response and recovery (also 57 percent). These data reveal a strategy in which HRDs prioritize outsourcing their “people problem” through staff training while delegating 24/7 security operations like detection and response to third-party cybersecurity providers. This approach allows organizations to focus on overall strategy while leveraging external groups for highly specialized tasks.
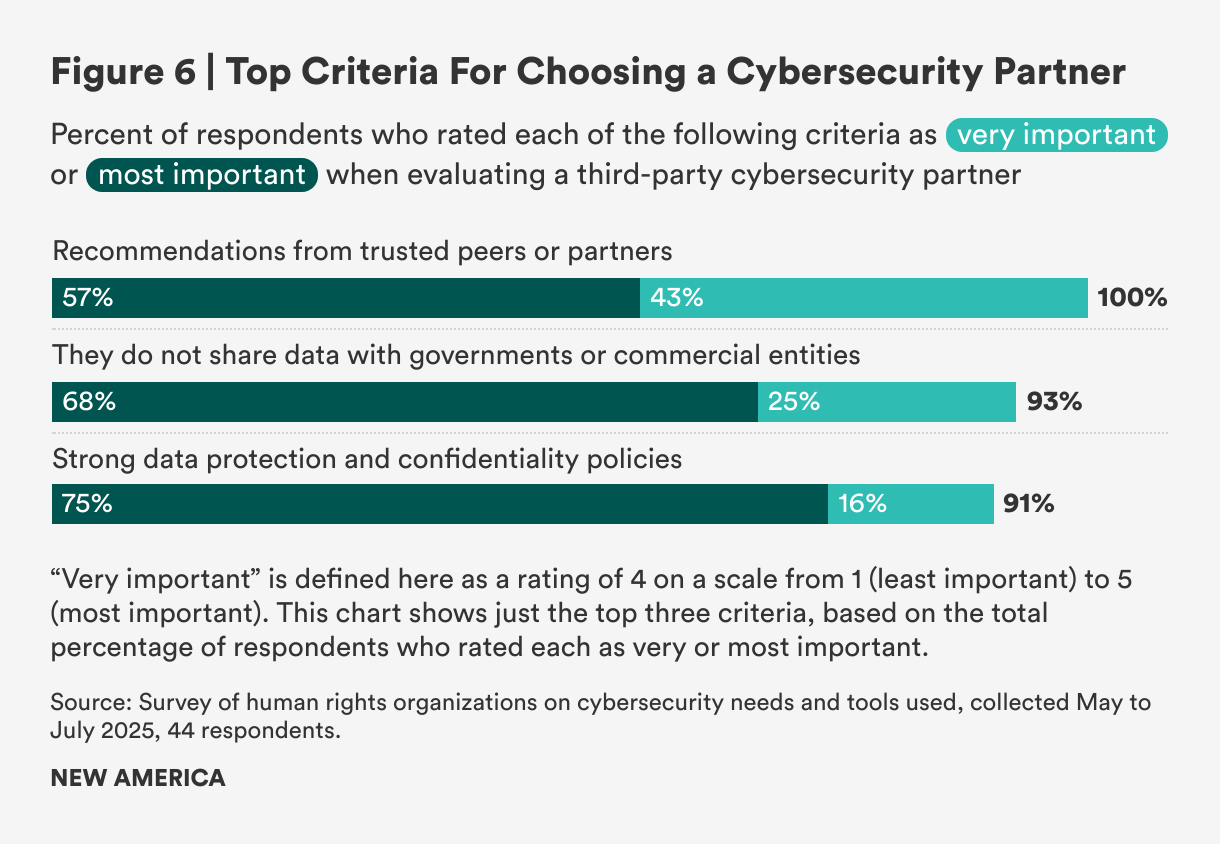
When evaluating third-party cybersecurity providers, trust and data governance are the most critical factors. As shown in Figure 6, the survey revealed that a strong data protection and confidentiality policy was rated “most important” by 75 percent of respondents, while a commitment to not share data with governments or commercial entities was similarly rated by 68 percent. This strong focus on data sovereignty is crucial because many HRDs view government entities as primary threat actors, making any data-sharing agreement a significant security vulnerability.
Beyond data policies, trust within peer networks was a universal theme. Every single respondent rated a recommendation from a trusted partner as highly important (a score of 4 or 5 on a scale of 1 to 5). In contrast, several factors were considered low priority, including the provider offering support in a local language or having nonprofit status, both of which 72 percent of organizations rated as unimportant (less than 3 on the scale).
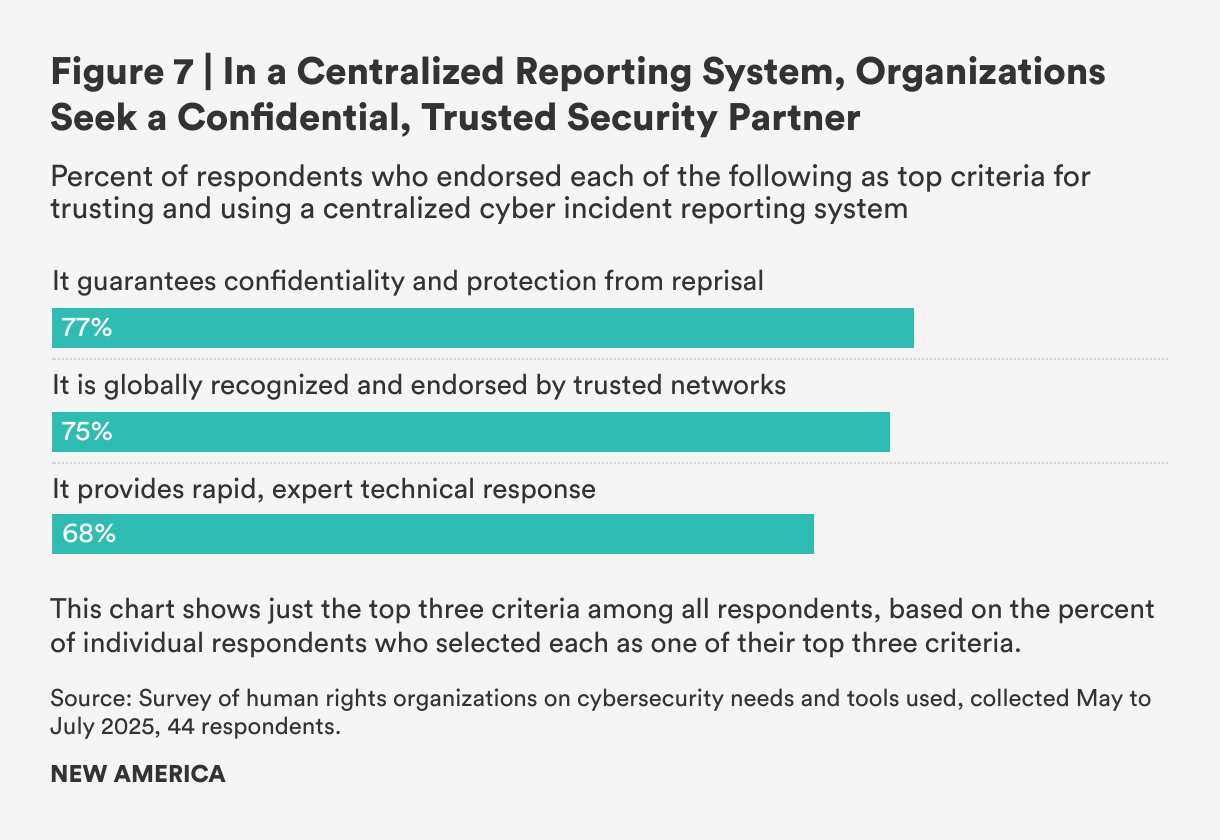
Although no single international reporting system currently exists where HRDs can report cyberattacks carried out against them, a strong majority—84 percent—would welcome such a system. However, their participation would be conditional on whether such a system met certain clear requirements—the most important being confidentiality guarantees and protection from reprisal, a condition cited by 77 percent of HRDs surveyed (see Figure 7).
It was also important to respondents that the system be recognized and endorsed by a trusted partner network (75 percent) and to provide rapid technical support and response (68 percent). As an investigative journalism organization based in Belarus put it,
“[The reporting system] doesn’t need to be globally recognized or backed by big organizations. What matters most is whether it has a strong reputation and is endorsed by people we trust in our community. For us, trust is everything. We know the biggest threats we face come from the government. We’ve seen how state actors launch attacks to silence us, block access to our work, and even compromise infrastructure. Any system we use has to guarantee real security and independence, otherwise it puts our journalists and sources at serious risk.”
Overall, these responses suggest that most HRDs would make use of a centralized threat sharing and cybersecurity organization, provided it is effective and can ensure appropriate privacy. Yet even in this arena, some HRDs would struggle with the human factors:
“If there were a trusted international system for reporting cyber incidents, would we use it? Honestly, I said no—not because we wouldn’t want to, but because we wouldn’t know how. There’s no clear guidance or training on what steps to take, and it feels like something only experts know how to navigate. If we understood the process and felt confident using it, then yes, we absolutely would.”
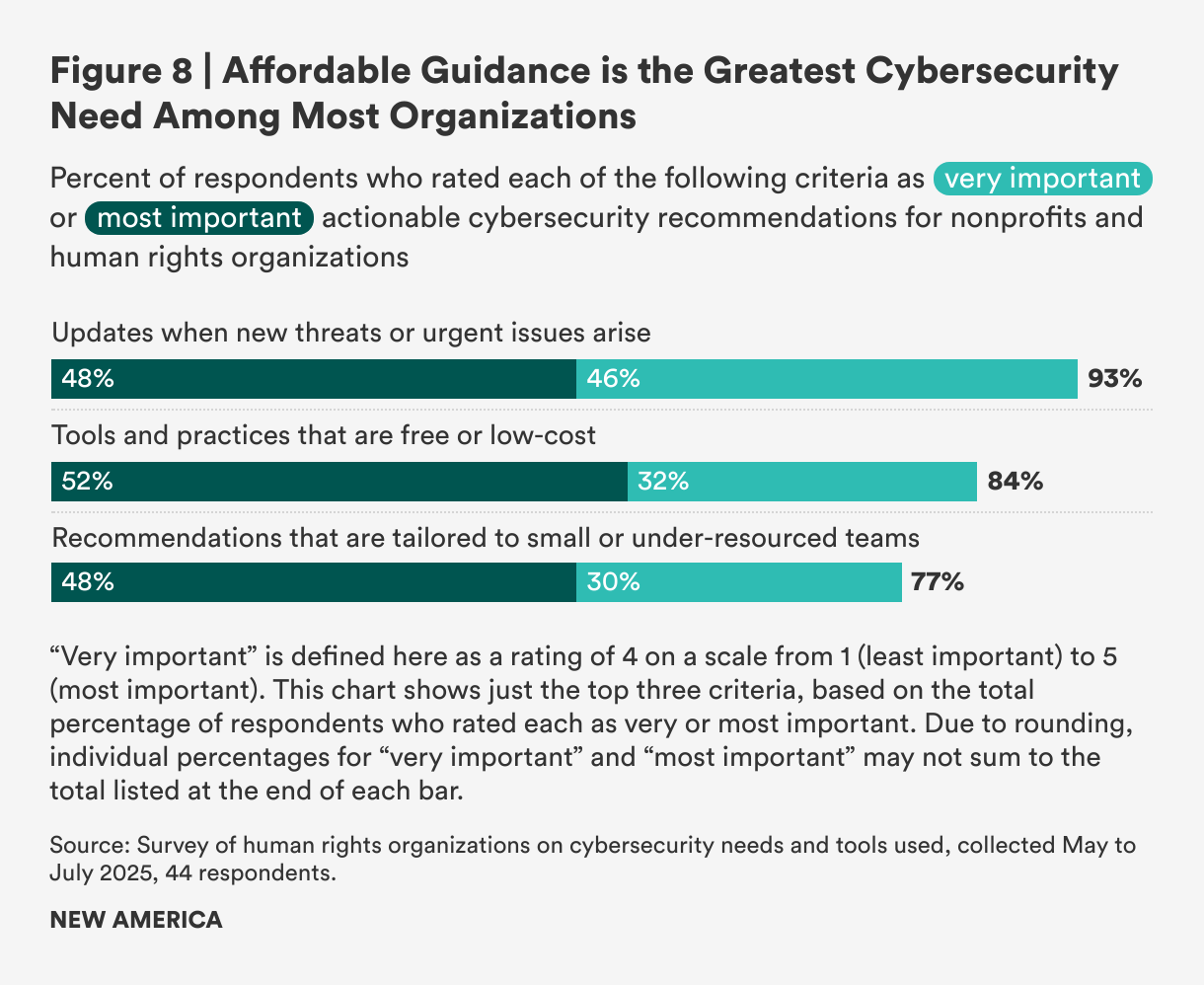
Cybersecurity Guidance
Organizations facing active threats with limited resources were asked to identify their top priorities for cybersecurity guidance. As illustrated in Figure 8, nearly all organizations (93 percent) responded that receiving updates on emerging threats was either a “very important” or the “most important” form of actionable cybersecurity guidance. This was followed by access to free or low-cost tools (84 percent) and recommendations tailored for small or under-resourced teams (77 percent). This data highlights a clear demand not only for complex security systems but for affordable partners providing guidance. As one respondent noted, “I’m often aware of general threats against organizations like ours, but the missing piece is always the practical response. The warnings tell me a threat exists, but they rarely provide clear steps on what my organization should do about it.”
In contrast, several aspects of cybersecurity guidance were considered less important. For instance, materials available in the organization’s local language were a low priority for 79 percent of organizations, and real-world case studies were assigned low importance by 61 percent of HRDs.
Despite background research showing low cybersecurity confidence among HRDs, a significant number of survey participants reported feeling highly confident in their cybersecurity management. This confidence, however, is not necessarily due to strong in-house technical skills. Instead, under-resourced teams strategically outsource critical security functions to trusted external partners. As a representative of the Fair Future Foundation, a volunteer-run humanitarian organization that provides medical care, clean water, and sanitation to remote Indonesian villages, said: “As a small medical NGO working in ultra-rural Indonesia, we operate under severe constraints with no reliable internet, very limited technical capacity, and high health risks. Cybersecurity is important for us, but often overshadowed by urgent health crises. Tailored, practical, low-cost solutions and clear guidance for low-resource settings are crucial.”
And yet, while this trust-based model can help HRDs feel secure, the fact that many remain “not sure” if they have been breached reveals a lack of internal visibility that could undermine their positive self-assessment. The high confidence can be a testament to the necessity of outsourcing rather than proof of their own technical strength.
Key Takeaways
Human Factors Can Be the Largest Hurdle for Organizations
The greatest barriers to cybersecurity are not technical; they are human. For 41 percent of organizations surveyed, a primary obstacle is a lack of time due to competing priorities. This issue is worsened by resistance to change, which 39 percent of organizations identified as a moderate barrier. The core challenge is also not a lack of effective tools—less than half of organizations (34 percent) stated that a shortage of “good enough” tools was a significant barrier—but rather the difficulty of integrating security practices into the demanding daily operations of human rights work.
Trust Is the Largest Theme in the Human Rights Space
Partnerships and trust drive security decisions, with all respondents citing a recommendation from a trusted partner as the most important factor in choosing a third-party cybersecurity provider. This emphasis on trust extends to data protection, with 75 percent of organizations prioritizing strong data governance and 68 percent requiring a commitment that data will not be shared with governments. This is a direct response to their primary threat actors, who 36 percent of organizations identified as government entities.
Human Rights Organizations Rely on External Cybersecurity Services
Human rights organizations rely heavily on external security capacity. Just over half (55 percent) of organizations surveyed said they were only “somewhat confident” in their ability to evaluate new security tools on their own; 46 percent admitted that they would be more vulnerable to threats without external training. These data suggest that their perceived strength comes from relying on external networks, not from internal self-sufficiency.
The Need for Practical Guidance
Organizations are more focused on getting actionable, immediate data on cyber threats than on theoretical guidance. Their most critical needs include timely updates on emerging threats (cited by 93 percent of organizations), access to free or low-cost tools (84 percent), and practical recommendations for small, under-resourced teams (77 percent). In contrast, less value is placed on time-intensive materials like real-world case studies, which 61 percent of organizations consider a low priority. This shows a clear preference for immediate, practical solutions.
Recommendations
To ensure human rights defenders (HRDs) can operate securely, the cybersecurity support ecosystem must move beyond fragmented, short-term solutions. This report provides recommendations for key stakeholders—civil society, donors, the private sector, and the international community—on how to invest in sustainable, long-term infrastructure to better protect frontline defenders.
For Civil Society
Civil society groups lead the way in protecting HRDs. However, to move from reactive projects to providing lasting protection, their work must be built on a foundation of sustainable funding.
Develop and Maintain Training for Defenders
Creating shareable training is a core function, directly addressing the need for clear, step-by-step guides written in nontechnical language and recommendations for under-resourced teams. As one NGO respondent stated, “Clear guidance for low-resource settings” is crucial. Sustainable funding is required to maintain these resources over the long term and keep them updated against new threats.
Build and Sustain Trusted Peer Review Networks
Formalizing networks for peer-reviewing tools directly responds to the finding that the most important factors for trusting a security tool are recommendations and endorsements from trusted peers and partners. This essential community infrastructure cannot run on just the goodwill of companies; it requires dedicated staff and resources, which sustainable funding provides.
Improve Staff Confidence in Security Tools
Helping groups understand what they want to protect is crucial to improving staff confidence in identifying security tools. While almost 30 percent of respondents said they are not held back by the belief that their current tools are “good enough,” a significant lack of confidence in staff’s ability to handle threats acts as a barrier. This factor was rated as having a high impact by 11 percent of organizations surveyed and a moderate impact by 36 percent. This suggests that the challenge is not a false sense of security but rather the hurdles of integrating new security practices and understanding of what to protect.
For Donors
To shift cybersecurity from an under-resourced item to an operational component, donors must see their role as sustaining the support ecosystem.
Require and Fund Digital Safety Plans
Individuals or organizations that fund nonprofit organizations should require and provide dedicated funding to support digital safety plans. The survey shows that a majority of organizations are either confirmed compromised or dangerously uncertain of their security status. The primary obstacle to addressing this is not a lack of will, but a lack of time due to competing priorities, which 41 percent of organizations cited as a high-impact barrier. By making a safety plan a funded requirement, donors can provide the necessary resources to transform security from an overlooked priority into a core, strategic function.
Establish an Audit Mechanism
Donors should establish an audit mechanism to help grantees validate their security posture. The survey reveals a critical gap between self-assessed capacity and the reality of the group: While 46 percent of organizations rated their capacity as “high,” 16 percent were unsure if they had suffered a successful cyberattack. To ensure these audits are consistent and effective, they should be measured against an agreed-upon cybersecurity framework, such as the NIST Cybersecurity Framework. External audits provide an objective assessment to identify hidden vulnerabilities, ensuring grant funds support organizations that are truly resilient against threats.
For the Private Sector
Private sector entities can contribute to the sustainability of the ecosystem by reducing the technical burden on frontline organizations and the civil society groups that support them.
Adopt Secure-by-Design Principles
By applying a security-first model, technology companies can create tools that are easier and safer to use.1 This approach aligns with the needs of HRDs, as 68 percent of organizations surveyed rated essential security features such as multi-factor authentication a top priority when evaluating a new tool. In a sector in which every single organization relies on trust when selecting partners, a public commitment to taking ownership of security outcomes is the most effective way to build the credibility required to serve this community.
Co-Design and Test Tools with Civil Society Partners
The survey reveals that 55 percent of HRDs feel only “somewhat confident” in their ability to assess new tools. This lack of confidence creates a major barrier to adoption. Collaboration between the manufacturers of cybersecurity tools and their users in the HRD community could be an effective way of addressing this issue. By co-designing with civil society partners that support HRDs in making decisions about new tools, a company can ensure its products meet HRDs’ unique security needs and build the trust required for market acceptance. This proposed collaboration directly addresses the top priority of 77 percent of respondents: trustworthiness.
Increase Donation of Tools and Services to Civil Society Partners
Tech companies and donors should provide more low-cost or no-cost tools for cybersecurity to HRDs and their civil society partners. These donations need to go beyond licenses and other goods to include services to assist with implementation, change management, and other aspects of installing new tools.
For the International Community
The establishment of a trusted, coordinated global body to support the cybersecurity needs of HRDs is necessary to replace the fragmented and unpredictable support provided in the current ecosystem. (The feedback from stakeholders highlights that while organizations like Access Now are well-positioned to take on a coordinating role due to their resources and standing, they may face inherent trust issues from smaller groups.)
Create a Multi-Sector Fund for Civil Society Support
The most critical step is to establish a sustainable, pooled funding mechanism dedicated to supporting the civil society organizations that provide essential cybersecurity aid. This will ensure the vital ecosystems that build community trust remain operational and can offer their services to frontline defenders reliably and affordably.
Launch a Coordinated and Funded Incident Response System
There is a clear demand for a trusted international system for responding to cyberattacks, with 77 percent of organizations surveyed saying they are willing to use one. For such a system to be trusted, it must guarantee confidentiality—the top concern, cited by 77 percent of respondents—and provide rapid, expert technical response.
Develop a “Tool Safety Index” and Threat-Sharing Platform
A threat-sharing platform would directly address the community’s need for updates on emerging threats, which 93 percent of organizations consider highly critical. There is a clear appetite for such a system, as 84 percent of organizations indicated they would be willing to report incidents to a designated, trusted body.
Citations
- See “Secure by Design,” Cybersecurity and Infrastructure Security Agency, source.
Conclusion
Digital threats to human rights defenders (HRDs) have reached a crisis point, fueled by rising authoritarianism and cuts to foreign aid. Among their greatest vulnerabilities is a fragmented and uncoordinated support ecosystem that leaves HRDs exposed to digital threats from powerful adversaries. The path forward requires establishing sustainable, long-term funding as a top priority and empowering HRDs with practical education to help them understand and navigate their unique risks.
The challenges facing these organizations are clear: They are targeted by sophisticated state actors and cybercriminals while struggling with limited time and resources. This report concludes that addressing these challenges requires more than just new tools but a fundamental shift toward building and sustaining the support ecosystem they rely on.
Ultimately, investing in this trusted support infrastructure is a direct investment in the safety, resilience, and efficacy of human rights defenders everywhere. Their ability to protect freedom of expression and political opposition is foundational to the survival of democracies around the world. Ensuring their voices can participate and remain secure online needs to be a priority for governments, organizations, and individuals worldwide.
Appendix: Survey Methodology
This appendix presents the full survey disseminated for this report. The survey was designed to gather insights into how nonprofits and human rights organizations discover, evaluate, and adopt cybersecurity tools. In addition, it sought to identify key challenges, gaps in support, and opportunities for collaboration within the sector.
The survey was organized into six sections:
- Section 1: About Your Organization
- Section 2: Current Cybersecurity Capacity
- Section 3: Tools and Discovery
- Section 4: Third-Party Support Models
- Section 5: Recommendations and Incident Reporting
- Section 6: Final Reflections
Survey: Exploring Cybersecurity Needs and Tools for Human Rights Organizations
For the purpose of this survey, “cybersecurity” refers to the practices and tools your organization uses to keep its digital systems, data, and communications safe from hacking, surveillance, or other online threats. This includes things like:
- Using secure messaging apps (e.g., Signal, WhatsApp)
- Protecting devices with antivirus or encryption
- Managing strong passwords and two-factor authentication
- Training staff on how to avoid phishing attacks
- Backing up important data securely
For this survey, “cyber incident” means any event that threatens your organization’s digital security, such as the confidentiality, integrity, or availability of digital information or information systems. This includes both successful and unsuccessful cyberattacks, as well as security breaches that may not involve a direct attack. A “cyberattack” refers more specifically to deliberate, malicious actions that cause harm to a system, including unauthorized access, data theft, disruption of services, or damage to systems.
Section 1: About Your Organization
Tell us a bit about your organization as it helps us understand the diversity of experiences represented in the survey.
1. What is your primary role within the organization? (Fill in the blank.)
2. Which region(s) does your organization primarily operate in? (Select all that apply.)
- Africa
- Asia-Pacific
- Latin America
- Middle East and North Africa
- Europe
- North America
- Other:
3. Who do you consider your organization’s most significant cybersecurity threat actor? (Mark only one.)
- Government actors
- Cybercriminals
- Political or ideological groups
- Private companies
- Other:
Section 2: Current Cybersecurity Capacity
These questions explore how your organization currently approaches cybersecurity, which includes your technical capacity, internal support, and training.
4. How would you rate your organization’s technical capacity in cybersecurity? (Mark only one.)
- High (Dedicated technical staff and proactively manage cybersecurity)
- Moderate (Some technical knowledge and can handle basic cybersecurity needs)
- Low (Rely heavily on external support or struggle to manage cybersecurity internally)
- Very low (Minimal technical capacity and are vulnerable to threats)
5. Has your organization experienced a cyber incident (examples include phishing attacks, malware infections, ransomware attacks, data breaches, and insider threats) in the past 3 months? (Mark only one.)
- Yes
- No
- Not sure
6. Has your organization experienced a cyberattack (i.e., deliberate, malicious actions such as phishing, malware, and denial-of-service attacks) in the past 3 months? (Mark only one.)
- Yes
- No
- Not sure
7. How often do you participate in cybersecurity-related workshops or training sessions? (Mark only one.)
- At least once a month
- A few times a year
- Once a year or less
- Never
8. What would happen if you or your team no longer had access to training from external cybersecurity experts? (Mark only one.)
- We would fall behind in security best practices
- We would be more vulnerable to threats
- We wouldn’t know how to choose or use new tools
- It wouldn’t affect us much as we are fully self-sufficient
- Other:
9. What additional support would help you feel more secure in protecting your organization? (Select the top three that apply.)
- More training on using cybersecurity tools
- User-friendly tools
- Multilingual support for tools and documentation
- Direct access to technical experts for assistance
- More financial support for cybersecurity tools
- Access to peer networks for knowledge sharing
- Other:
Section 3: Tools and Discovery
This section focuses on how your organization finds, evaluates, and adopts cybersecurity tools to protect your work and the people you serve.
10. How strongly do the following factors motivate you to look for new cybersecurity tools? (Rate each on a scale from 1 (not at all motivating) to 5 (extremely motivating). Check all that apply.)
- A recent threat or security incident
- Launching a new project or campaign
- Participation in a training session or workshop
- Recommendation from a peer or partner organization
- Requirements from donors or funders
- Discovery of new tools through media or online platforms
- Change in staff or technical capacity
- Desire to improve or upgrade current security practices
11. How important is each of the following categories when evaluating a new cybersecurity tool? (Rate each on a scale from 1 (least important) to 5 (most important). Check all that apply.)
- Usability
- Cost (free vs. paid)
- Trustworthiness/source of the tool
- Peer reviews or testimonials
- Language/localization
- Technical support availability
- Open source vs. proprietary
- Compatibility with existing systems
- Security features (e.g., encryption, multi-factor authentication)
12. How important are the following sources in helping you discover new cybersecurity tools? (Rate each on a scale from 1 (least important) to 5 (most important). Check all that apply.)
- Social media
- Online searches
- Recommendations from peers/partners
- Attending trainings/workshops
- Community forums/listservs (e.g., Association for Progressive Communications, Access Now)
- Newsletters or blogs
13. How do you determine whether a cybersecurity tool is trustworthy before using it? (Select the top two that apply.)
- It is recommended by a trusted peer, partner, or trainer
- It is open source, and the code is available for review
- It has been reviewed or endorsed by a reputable nongovernmental organization or digital rights group
- It has a clear and transparent privacy policy
- It is developed or supported by a nonprofit or academic institution
- Other:
14. Who is involved in the decision-making process when choosing a cybersecurity tool? (Mark only one.)
- Individual decision
- IT team
- Leadership
- External consultant
- Donor recommendation
- Other:
15. What challenges have you faced while implementing cybersecurity tools on your own or [for your] organization? (Select the top two that apply.)
- Lack of technical expertise
- High cost of tools
- Limited access to tools in my language
- Tools are difficult to configure or use
- Lack of training resources
- Other:
16. How confident are you in your ability to assess the security and trustworthiness of a cybersecurity tool before using it? (Mark only one.)
- Very confident: I can evaluate tools independently and understand what to look for
- Somewhat confident: I can make basic judgments but often rely on others
- Not very confident: I usually depend on recommendations from trusted sources
- Not confident at all: I don’t know how to assess whether a tool is secure or trustworthy
17. How significant are the following challenges your organization has faced when implementing cybersecurity tools? (Rate each on a scale from 1 (not a challenge) to 5 (major challenge). Check all that apply.)
- Lack of technical expertise
- High cost of tools
- Limited access to tools in my language
- Tools are difficult to configure or use
- Limited or no support from tool providers
- Fear of retaliation or surveillance
- Lack of training resources
Section 4: Third-Party Support Models
We’d like your thoughts on the idea of outside organizations helping manage or support your cybersecurity needs, such as trusted nonprofits or technical service providers.
18. Would your organization be open to having a third-party service provider manage your cybersecurity operations (e.g., securing websites, monitoring for threats, managing encryption)? (Mark only one.)
- Yes, we would prefer to outsource cybersecurity management to experts
- No, we prefer to manage our cybersecurity internally
19. How important are the following criteria when evaluating whether to trust and work with a third party to manage your organization’s cybersecurity operations? (Rate each on a scale from 1 (least important) to 5 (most important). Check all that apply.)
- The provider is a nonprofit organization
- The provider has experience working with human rights organizations
- They offer transparent practices and clear accountability
- They do not share data with governments or commercial entities
- They provide services in our local language or region
- They offer free or subsidized support for under-resourced groups
- They allow us to retain control over critical decisions
- They have strong data protection and confidentiality policies
- Recommendations from trusted peers or partners
20. What specific types of cybersecurity support would your organization be most willing to outsource to a trusted third party? (Select the top three that apply.)
- Threat detection and monitoring
- Incident response and recovery
- Tool selection and implementation
- Staff training and awareness
- Secure website or server hosting
- Ongoing system updates and patching
- Risk assessments or audits
- Other:
Section 5: Recommendations and Incident Reporting
This section asks about your interest in receiving tailored cybersecurity recommendations and whether your organization would use a centralized, secure reporting system for digital threats.
21. If there were a secure third-party system to report cyberattacks or threats, would your organization use it? (Mark only one.)
- Yes
- No, we prefer to handle incidents internally
22. How important are the following features to your organization when considering actionable cybersecurity recommendations specifically for nonprofits and human rights organizations? (Rate each on a scale from 1 (least important) to 5 (most important). Check all that apply.)
- Clear, step-by-step guides written in nontechnical language
- Recommendations that are tailored to small or under-resourced teams
- Tools and practices that are free or low-cost
- Guidance on how to prioritize which tools to implement first
- Multilingual materials or region-specific guidance
- Real-world examples or case studies of similar organizations
- Options for direct support or consultation
- Updates when new threats or urgent issues arise
- Printable checklists or quick-reference materials
23. What would make you trust and use a centralized reporting and advocacy system for cyber incidents? (Select the top three that apply.)
- It is run by a nonprofit or civil society–led body
- It provides rapid, expert technical response
- It guarantees confidentiality and protection from reprisal
- It is globally recognized and endorsed by trusted networks
- It includes advocacy or legal follow-up beyond technical support
- It publishes regular reports on trends and threats
24. If a trusted international system for cyber incident reporting existed, how likely would your organization be to use it? (Mark only one.)
- Yes
- No, we prefer to handle incidents internally
Section 6: Final Reflections
A few closing questions, including the option to participate in a follow-up interview or be featured in the final research.
25. Would you like to remain anonymous? (Mark only one.)
- Yes
- No
26. Would you be open to being contacted for a follow-up discussion or interview? (Mark only one.)
- Yes
- No
27. If you are open for a follow-up discussion, please provide your contact.
28. Comments or additional insights you’d like to share?