Table of Contents
- Key Points
- Summary and Introduction
- Section One: What are Cybersecurity Jobs?
- Section Two: How Do We Teach Cybersecurity?
- Section Three: How is Competence Measured and Communicated?
- Section Four: What is the Role of Government in Cyber Workforce Development?
- Conclusions
- Appendix: Unanswered Questions in Cybersecurity Workforce Empirics
Section One: What are Cybersecurity Jobs?
Detailed research that monitors and quantifies the cybersecurity workforce is hard to come by. One of the few points that has been consistently measured is the very top-line number: How many people work in cybersecurity? In 2010, experts estimated that there were 2.28 million information security1 professionals employed worldwide.2 By 2015, there were 4.24 million professionals, almost almost twice as many as five years prior.
Observers soon started measuring not just the total number of professionals employed, but also projections of the future difference between open cybersecurity jobs and the expected number of workers entering the industry. In 2015, the anticipated global shortfall was expected to reach 1.5 million unfilled jobs by 2020;3 in 2017, the estimate was 1.8 million by 2022;4 and the estimated current-day gap is close to 3 million.5 The trend is hard to ignore. However you define them, it is clear that unfilled cybersecurity jobs in the field are emerging at a dramatically increasing rate.
But other than indicating a need for more workers, what do those numbers really say? It is hard to infer much meaning simply because “the cybersecurity workforce” is a malleable term. Efforts to define and classify “cybersecurity jobs” are only just beginning to see common use, and as cybersecurity becomes an increasingly critical part of virtually every industry, the number of non-technical roles that require some amount of cybersecurity expertise is growing quickly.
Cybersecurity Jobs are Heterogeneous
The pool of cybersecurity jobs encompasses a broad range of work, which often overlaps with other fields. Acknowledging and delineating the variations in cybersecurity jobs allows policymakers and stakeholders to develop a greater variety of solutions tailored to different specific requirements. Some systems exist to do this, but further work remains.
The National Initiative on Cybersecurity Education (NICE), an office within the National Institute of Standards and Technology, has undertaken the daunting task of standardizing the language and taxonomy used to describe work in cybersecurity. (Disclosure: Some of the Cybersecurity Initiative work is funded by NIST/NICE. They did not provide any financial support for this publication.) The NICE Cybersecurity Workforce Framework6—a self-described “non-prescriptive cybersecurity workforce dictionary”— was first posted for public comment in 2012, and since has been informed by extensive outreach to the cybersecurity community.
In 2015, the anticipated global shortfall was expected to reach 1.5 million unfilled jobs by 2020; in 2017, the estimate was 1.8 million by 2022; and the estimated current-day gap is close to 3 million.
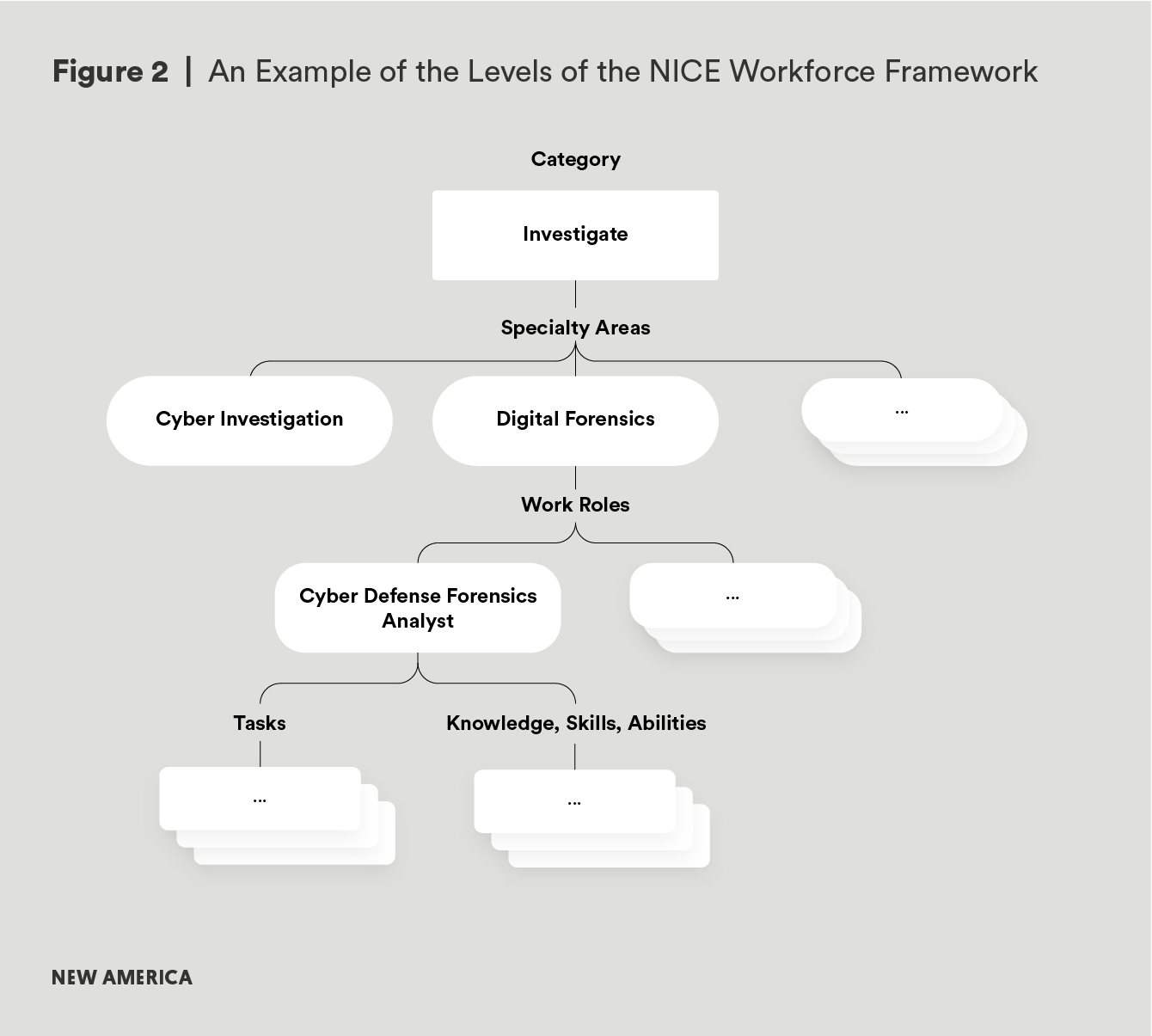
The framework sorts the industry into seven categories, depicted in Figure 1, which then divide into 32 specialty areas, which further separate into specific work roles, each detailed with tasks expected and the knowledge, skills, and abilities required to be successful in that specific work role. For example, “Investigate” is one of the seven categories defined. “Digital Forensics” is a specialty area within the “Investigate” category. “Cyber Defense Forensic Analyst” is a job role within “Digital Forensics,” and one expected task is “Conduct[ing] analysis of log files, evidence, and other information to determine best methods for identifying the perpetrator(s) of a network intrusion.”7 These relationships are depicted in Figure 2.

The NICE framework helps provide a common lexicon, but it is not used universally. Many bureaucracies have legacy frameworks that do not map directly to the NICE framework, and the human resources restructuring necessary for implementation is seen as burdensome relative to the potential benefits of standardization. Other employers, particularly those that have deep experience in information security, prefer to stay with their own understandings of cybersecurity jobs. While this variation is not a bad thing, it makes it difficult to measure statistics and trends across the industry. Without that kind of empirical data, it is hard to design policies that respond to real-world demands.
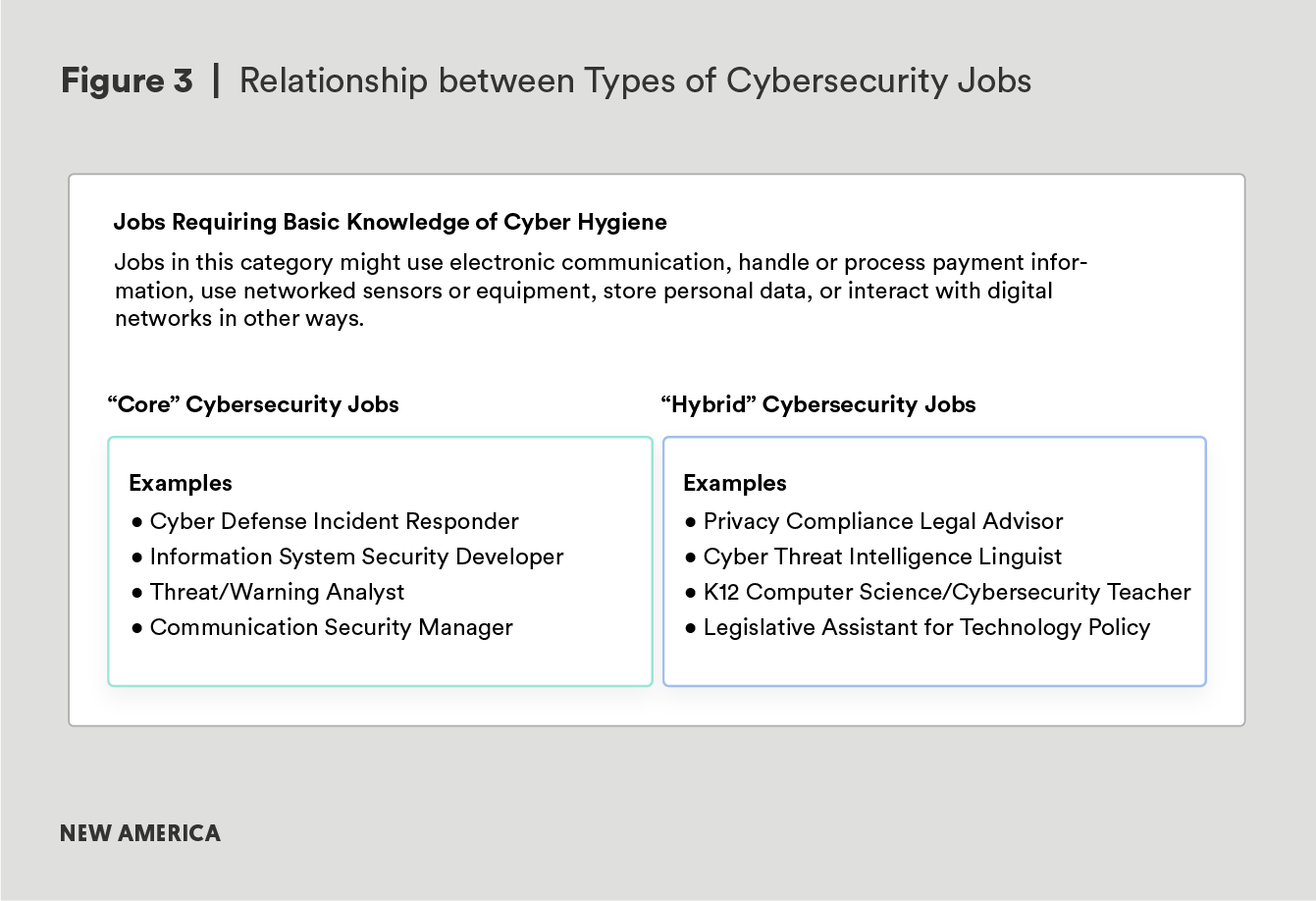
There is another category of work that is not generally—and arguably should not always be—captured in the NICE framework, and may require its own taxonomy. Sometimes called “hybrid jobs,”8 these are jobs that touch on cybersecurity, but are not, strictly speaking, based in the same discipline. The NICE framework addresses some of what might be called “hybrid jobs” (e.g. cybersecurity legal advisors, hiring managers, and instructors).
Trying to include all hybrid jobs would dilute the utility of the framework. Does one include a company executive in charge of risk management? Currently, this would not generally fall within the framework, but clearly this individual would need to have a very firm understanding of the company’s cybersecurity risk profile to perform their job effectively. Similarly, a legislative assistant who advises on national cybersecurity policy must also be cybersecurity experts in their own fashion.
When any employee can accidentally fall for a phishing scam and expose that core product to harm, it becomes important for all employees to understand the basics of good cyber hygiene.
The converse is also true. In many cases, sector-specific knowledge is essential to enable a cybersecurity expert to work effectively. For example, cybersecurity in financial services is a discipline in its own right.9 Experts in these jobs need to understand not just cybersecurity itself, but the nuances of the complex regulatory framework that protects everything from consumer data to the international banking networks that enable financial transactions.
Virtually every sector of the economy benefits from a certain amount of cybersecurity awareness. Networked information systems are critical to the core functions of most businesses. For example, Goldman Sachs CEO Lloyd Blankfein has famously declared, “We are a technology firm.”10 JPMorgan CFO Marianne Lake has expressed a similar sentiment,11 and they are not alone. Increasingly, companies’ core products are becoming their digital tools and systems. When any employee can accidentally fall for a phishing scam and expose that core product to harm, it becomes important for all employees to understand the basics of good cyber hygiene.
Clearly, not every employee with access to email should be considered a cybersecurity worker, for all that good cyber hygiene may be critical to success. It becomes increasingly difficult to know where to draw the line in terms of what is or is not considered part of the cybersecurity workforce. This report does not define a line separating “cybersecurity” from “not cybersecurity,” but rather treats cybersecurity jobs as overlapping sets of roles ranging from the types of positions that fall within a conventional understanding of cybersecurity to experts with hybrid jobs—those positions where cybersecurity and another specialty are functionally inseparable—to virtually every position that benefits from increased cybersecurity awareness.
Degree and Experience Requirements
Unthinking requirements for degrees and work experience artificially narrow the pool of potential employees. Bachelor’s degrees should not be the only entry point into the field, especially in a field that prizes on-the-job experience. For those jobs where a bachelor’s degree is necessary or enables long-term career growth, conventional degrees can be improved by incorporating work-based learning.
One of the challenges of evaluating the cybersecurity workforce is simply that very little data exists to use as a benchmark against which to measure changing trends. Organizations like (ISC)2 (The International Information System Security Certificate Consortium)12 measure some high-level numbers like the total number of cybersecurity workers globally, and NICE, CompTIA, and Burning Glass have jointly built CyberSeek, a tool that monitors data on job postings in the United States that fall within the NICE workforce framework and the industry certifications that are in demand.13
Even with these resources, there are significant gaps in the data, often filled by anecdotes or assumptions. For example: How many jobs in other sectors or functions require significant cybersecurity expertise? How many cybersecurity experts were trained initially by the intelligence community or military? How many are trained in higher education institutions? How many learn in informal settings—on-the-job or through self-teaching—and, without a degree, how do they market themselves to employers? To what extent are recent graduates hired into cybersecurity positions in the private sector? In the public sector?
Many narratives exist describing typical career paths and entry points into the cybersecurity job market. Observers might hear that most experts cut their teeth in government; experts are recruited into the private sector from capture the flag competitions (CTFs);14 computer science graduates do (or do not) make good hackers. Most of these observations are based on intuition or anecdotes. The data to indicate which entry points, training programs, or hiring strategies are most effective—or even most common—is extremely limited.
The data that exists is most often drawn from job postings, which shapes the data itself. For example, a job posting may require years of work experience and a graduate degree, but an employer may not be able to find (or afford) someone with those qualifications, and may hire someone more junior with the expectation of training them. Thus accountings of requirements in job postings probably inflate the characteristics of workers in the field. However, job posting data remains the best proxy available for insight into what employers are seeking, and there are certainly notable points in the data. Among the key takeaways: 84 percent of job postings in the industry list a bachelor’s degree as a minimum qualification, and 83 percent of job postings in cybersecurity require at least three years of work experience.15 Requirements like this are increasingly facing criticism as unattainable, unrealistic, or unnecessary.16 Or, as some have said more bluntly, “There is no cyber talent crunch; you’re just hiring wrong.”17
The data to indicate which entry points, training programs, or hiring strategies are most effective—or even most common—is extremely limited.
Of course, hiring requirements are not inherently bad. They allow hiring managers to focus in on a pool mostly likely to meet their needs. But are these requirements actually effective filters in cybersecurity? Setting aside the work experience requirement for a moment, the requirement for a degree creates problems both in terms of the number of graduates available and the applicability of the degrees to cybersecurity jobs.
As a question of numbers alone, there simply are not enough graduates to fill available jobs, particularly when recalling that the estimated global cybersecurity labor shortage currently is close to 3 million unfilled jobs.18 U.S. post-secondary institutions were expected to confer just over 1.8 million bachelor’s degrees total—in all disciplines—in academic year 2017-2018.19 There is little in the way of data to indicate of how many students in a graduating class are likely to seek jobs in cybersecurity, but as a point of comparison, in academic year 2015-2016,20 64,405 bachelor’s degrees were awarded in computer and information sciences in the United States.21 Even allowing for the fact that some 35 percent of U.S. cybersecurity employees come from other fields of study,22 it is still quite clear that an adequate supply of graduates simply will not exist if current hiring requirements remain unchanged.
Not only will the supply of graduates be unavailable in terms of total numbers, experts are raising questions about whether or not a bachelor’s degree really does make an employee more effective in the workplace. Across industries, researchers have documented “degree inflation,” employers seeking candidates who hold degrees for positions that have traditionally been filled by workers without one.23 President of Opportunity@Work Byron Auguste highlights an example of this trend among administrative assistants. “When only 20 percent of administrative assistants have a bachelor’s degree but almost two-thirds of new job postings for admins require a B.A. to be considered, such practices make college degrees more of an arbitrary barrier than an inclusive bridge to middle-class work.”24 Information technology disciplines are coming to a similar realization, increasingly recognizing the presence of “middle-skill” jobs25— jobs that “require more education and training than a high school diploma but less than a four-year college degree.”26
In cybersecurity, as in many other fields, hiring managers would benefit from asking whether a four-year degree is necessary for a given position, or whether on-the-job learning, career technical education through a community college, or other training options may be a better fit. Apprenti—an organization that works with industry partners to build apprenticeships and has led a U.S. Department of Labor-funded effort to expand apprenticeship in information technology—worked with their clients to determine what roles required a bachelor's degree. Of their mid-tier work roles (the overarching category that includes cybersecurity roles), they found that some 40 percent can be effectively filled by workers without a bachelor’s degree.27
There is a strong argument that workers with diverse educational backgrounds, rather than a workforce comprised exclusively of graduates of four-year degree programs in STEM, are particularly well equipped for the challenges in cybersecurity.28 Not all users of cybersecurity products approach security products and systems from the same starting point, so why should product designers? Rather, a workforce with a mix of degrees, informal education, and other experiences better represents the diverse population likely to use those products.
This is not to devalue a four-year degree (or any degree) in career development, nor to suggest that career and technical education (CTE) is the right answer in all cases. Some positions do require a bachelor’s degree—or master’s or doctoral degree. In some cases, a degree may ensure better long-term outcomes than CTE for an employee who seeks to advance to positions, particularly in management, that benefit from exposure to general education requirements.
Research shows a good economic case for incorporating a bachelor’s degree as part of a long-term career. One review of studies showed a lifetime average present-value earnings benefit of $423,800 for those with a four-year degree.29 Douglas Webber of Temple University found that “the typical college graduate will earn roughly $900,000 more than the typical high school graduate over their working life,” but he strongly cautions that this is just an average.30 For an individual pursuing work in cybersecurity, this suggests that earning a degree at some point in their career makes sense, at least from a statistical standpoint. From an industry perspective, requiring that degree in all cases—and particularly for entry-level jobs—creates problems.
Notably, only 23 percent of cybersecurity industry experts feel that educational programs are graduating students with the skills needed to be useful in the workplace. In surveys, experts indicate a preference for hands-on experience and certifications over a bachelor’s degree.31 This would seem to contradict the widespread minimum requirement of a bachelor’s degree. Why require a degree if experience is considered more valuable? Some experts have attributed this seeming inconsistency to a lack of communication between subject matter experts initiating the hiring process and the human resources professionals actually posting the jobs. The researchers who conducted this particular survey suggest, “This contradiction indicates that a degree is more of a signal of general competence than an indicator of directly relevant cybersecurity skills.”32 Thus the degree becomes a means for signaling skills that are harder to quantify and demonstrate, like collegiality and perseverance. Regardless of the rationale that drives it, the degree requirement appears to be more of a default than a deliberate strategic choice, and warrants more explicit examination.
What, then, is the anticipated career pathway into the cybersecurity industry? As it currently stands, the typical requirement for four-year degrees and work experience means that the cybersecurity community is limiting their hiring search to college graduates, but providing no path for newly-minted graduates to get the experience needed to enter the field.
Security Clearances and Jobs in U.S. Government
The intelligence community and military offer some of the few entry points to cybersecurity career paths, but dependence on these pathways means that problems with the security clearance process have an outsized impact on the workforce.
There is anecdotal indication that some employers do hire entry-level professionals at a meaningful scale, particularly in federal government agencies and larger corporations that can afford their own internal training programs. On a systemic level, this model raises two questions. First, to what extent are these internal (and largely proprietary) trainings contributing to the overall workforce? Without adequate data on the size and retention rates of these workforces, it is hard to observe the impact of this pathway into the industry. Second, absent outside incentives, why would employers continue to bear the cost of internal training programs when employees may complete training and then leave for more lucrative positions with employers that elect to spend more on salaries and less on training?
Insofar as entry-level jobs can be found in the federal government, more than 10 percent of cybersecurity job postings require a security clearance.33 Ten percent may not seem like an overwhelming portion of the market, but given that government training appears to be one of the few truly entry-level pathways into work in cybersecurity, bottlenecks here are particularly problematic. Because human capital is flowing in through government to feed not just public sector national security jobs, but the whole of the cybersecurity ecosystem, when potential new hires are deterred by the clearance process and encounter a cybersecurity job market with limited or unattainable alternative entry points, they are liable to seek out not just other employers, but other industries entirely. In this way, troubled hiring practices in national security roles have an outsized impact on the rest of the cybersecurity community.
Security clearances are a necessary part of national security work, but the current process is unduly slow34 and would benefit from even the most basic reforms.35 According to Senator Mark Warner, Vice Chairman of the Senate Select Committee on Intelligence:
The U.S. government requires a well-functioning system for granting security clearances to make sure we have a workforce who can be trusted with our nation’s secrets. But the current system, born in the wake of World War II, when classified documents lived on paper and Telex, is simply too time-consuming, too expensive and too complex.36
Even Director of National Intelligence Dan Coats has proclaimed that “The process is broken. It needs to be reformed.”37
Author's Note
How does military and intelligence training impact the workforce?
There is an interesting related question on whether limited retention in federal positions has a larger systemic benefit, behaving like a subsidy to the cybersecurity industry in the form of workforce development. Government invests in training talent that then moves on to private sector employment after a relatively short time in government. This is no doubt frustrating for government hiring managers, but does feed the larger community. An excellent area for future research would be to study this flow of talent to learn what percentage of the overall U.S. cybersecurity workforce is receiving its training from the military and intelligence communities. Furthermore, what are the costs of this to the federal government? What are the economic benefits to the rest of the cybersecurity community? What would comparable education cost if conducted outside of government?
Where the cybersecurity workforce is concerned, the long timeline of the security clearance process sets up several very harmful dynamics. First, as reporting from the Government Accountability Office (GAO) suggests, prospective employees may simply choose to avoid government service to avoid the wait times and uncertainty inherent in the process.38 Second, this encourages contracting firms to lure cleared civilian and military employees away from their public sector jobs rather than pay to clear employees themselves. Third, the clearance cost and timeline discourages movement and interaction between private and public sector by making it hard for experts to transition in and out of cleared jobs over the course of their careers.
The realities of national security work are such that eliminating the necessity for security clearances will almost certainly never be possible. Security clearance reform, however, is a reasonable target. Advocates suggest that government agencies can move away from periodic reinvestigations and towards continuing evaluation, “a process to review the background of clearance holders and individuals in sensitive positions at any time during the eligibility period.”39 Such monitoring is predominantly automated and occurs in real time. By monitoring records on an ongoing basis, a police arrest or other indication of worrisome circumstances is likely to come to light before a scheduled reinvestigation. In fact, certain parts of the Department of Defense and the Office of the Director of National Intelligence are already developing continuing evaluation programs.40 Such practices could improve and expedite hiring, alleviating the bottleneck to accessing many cybersecurity jobs.
The Future of Cybersecurity Jobs
Technological advancements will not fix the workforce gap. Rather, emerging technologies will change the nature of cybersecurity work and requirements for the workforce.
To further complicate the meaning of “cybersecurity jobs,” savvy members of the cybersecurity ecosystem must also consider not just what these jobs are now, but what they will be in five, 10, and 20 years. The widely held belief is that automation will change at least some aspects of cybersecurity jobs. Those tasks and audits that can be done by an artificial intelligence (AI) program may decrease the overall quantity of work to be done, which some speculate will bring welcome relief for the often overtaxed workforce.41
Others point out that the introduction of these tools will also herald the advent of new AI-enabled threats, not to mention new targets.42 This suggests that the overall workforce demand will not lessen so much it will as shift from one specialty to another. Future employees would need to be well versed in AI and machine learning tools. A survey by the Ponemon Institute suggests that many practitioners predict that “automation will increase the need to hire people with more advanced skills,”43 making it even harder to meet the workforce needs of the cybersecurity industry. While technology may change the requirements for the workforce, it will not fundamentally change the challenge of connecting educational pathways with jobs that require experience on very specific tools.
The current system of cybersecurity education is inadequate for job seekers and employers, and without efforts targeted at broadening and realigning how we teach and hire cybersecurity skills, there is little reason to expect improvement. The barriers new employees must overcome to enter the field and gain their first years of experience push the cybersecurity community towards a tendency to hire experienced employees out of the public sector or competing firms,44 which discourages employers from funding workforce training when that training is quite likely to ultimately benefit a competitor when the employee is eventually poached. Full of self-defeating paradoxes, hiring assumptions determined by habit rather than intention, and spotty coordination between educators and employers, the cybersecurity community’s current strategy for workforce development desperately needs a redesign.
Citations
- For the purposes of this discussion, “information security” and “cybersecurity” are used interchangeably, with the acknowledgement that different discourse communities within the field often understand them to imply differences. This report endeavors to reflect the studies and reference material cited herein, and so generally has opted to use the same terminology used those materials, despite the variance in language that it has created throughout this document. For example, the study that informs this count of professionals uses the term “information security,” which is reflected here.
- Robert Ayoub, The 2011 (ISC)2 Global Information Security Workforce Study, (ISC)2 and Frost and Sullivan. 2011, 7, source.
- Michael Suby and Frank Dickson, The 2015 (ISC)2 Global Information Security Workforce Study, (ISC)2, Booz Allen Hamilton, NRI Secure, Cyber 360, and Frost and Sullivan, 2015, 3, source.
- 2017 Global Information Security Workforce Study: Benchmarking Workforce Capacity and Response to Cyber Risk, Center for Cyber Safety and Education, (ISC)2, Booz Allen Hamilton, Alta Associates, and Frost and Sullivan, 2017, source.
- (ISC)2 Cybersecurity Workforce Study, 2018: Cybersecurity Professionals Focus on Developing New Skills as Workforce Gap Widens, (ISC)2, 2018, source.
- William Newhouse, Stephanie Keith, Benjamin Scribner, and Greg Witte, National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework, National Institute of Standards and Technology, U.S. Department of Commerce, August 2017, source.
- Ibid. 25, source.
- Job Market Intelligence: Cybersecurity Jobs, 2015, Burning Glass Technologies Research, 2015, 3, source.
- For a closer look at issues unique to cybersecurity in the financial sector, see: William A. Carter and Denise E. Zheng, The Evolution of Cybersecurity Requirements for the U.S. Financial Industry, Center for Strategic and International Studies, July 2015, source.
- Katrina Brooker, “Goldman in Ventureland,” Bloomberg, July 28, 2015, source.
- Portia Crowe and Matt Turner, “JPMORGAN: 'We are a technology company,'” Business Insider, February 23, 2016, source.
- (ISC)2 “Global Cybersecurity Workforce Shortage to Reach 1.8 Million as Threats Loom Larger and Stakes Rise Higher,” news release, June 7, 2017, (ISC)2, accessed September 12, 2018, source.
- “Cybersecurity Supply and Demand Heat Map,” CyberSeek, source.
- A style of competition common at conferences and in training programs that encourages participants to demonstrate skills in a simulated environment.
- Job Market Intelligence: Cybersecurity Jobs, 2015, Burning Glass Technologies Research, 2015, 3, source.
- For a particularly colorful demonstration of such criticism, see Ming Chow’s Hall of Shame. The Senior Lecturer in Computer Science at Tufts University has compiled some of the more egregious examples of impractical requirements in cybersecurity job postings, viewable at source . Ming Y. Chow, “Hall of Shame Job Postings and Recruiting,” August 16, 2017.
- Robert Walker, “There Is No Cyber Talent Crunch; You’re Just Hiring Wrong,” Tripwire, June 5, 2017, source.
- (ISC)2 Cybersecurity Workforce Study, 2018: Cybersecurity Professionals Focus on Developing New Skills as Workforce Gap Widens, (ISC)2, 2018, source.
- “Table 318.10. Degrees conferred by postsecondary institutions, by level of degree and sex of student: Selected years, 1869-70 through 2025-26,” The National Center for Education Statistics, March 2016, source.
- 2015-2016 is the most recent year available through the National Center for Education Statistics as of writing.
- “Table 325.35. Degrees in computer and information sciences conferred by postsecondary institutions, by level of degree and sex of student: 1970-71 through 2015-16,” The National Center for Education Statistics, November, 2017, source.
- 2017 Global Information Security Workforce Study: Benchmarking Workforce Capacity and Response to Cyber Risk, Center for Cyber Safety and Education, (ISC)2, Booz Allen Hamilton, Alta Associates, and Frost and Sullivan, 2017, 5, source.
- Joseph B. Fuller and Manjari Raman, Dismissed by Degrees: How Degree Inflation is Undermining U.S. Competitiveness and Hurting America’s Middle Class, Accenture, Grads of Life, Harvard Business School, October 2017, 4, source.
- Byron Auguste, “Skills And Tomorrow's Jobs Report: The Usual Suspects,” Forbes, July 5, 2018, source.
- Steve Lohr, “A New Kind of Tech Job Emphasizes Skills, Not a College Degree,” The New York Times, June 28, 2017, source.
- Jennifer Burrowes, Alexis Young, Dan Restuccia, Joseph Fuller, and Manjari Raman, Bridge the Gap: Rebuilding America’s Middle Skills, Accenture, Burning Glass, and Harvard Business School, November November 2014, 4, source.
- Carlson, Jennifer. “Critical Success Factors for a Cybersecurity Apprenticeship Program.” Presentation, Pre-Conference Seminar at National Institute for Cybersecurity Education Annual Conference and Expo, Dayton, Ohio, 2017.
- Marc van Zadelhoff, “Cybersecurity Has a Serious Talent Shortage. Here’s How to Fix it,” May 04, 2017, source.
- Clive Belfield and Thomas Bailey, The Labor Market Returns to Sub-Baccalaureate College: A Review, Center for Analysis of Postsecondary Education and Employment, March 2017, source.
- Douglas Webber, “Is College Worth It? Going Beyond Averages,” Third Way, September 18, 2018, source.
- Hacking the Skills Shortage: A Study of the international shortage in cybersecurity skills, McAfee and Center for Strategic and International Studies, July 27, 2016, 13, source.
- Ibid. 13.
- Job Market Intelligence: Cybersecurity Jobs, 2015, Burning Glass Technologies Research, 2015, 3, source.
- Aaron Gregg, “Delays in federal background checks leave more than 700,000 people in limbo,” The Washington Post, August 27, 2017, source.
- Security Clearance Reform: Testimony before the Senate Select Committee on Intelligence, 115th Congress (2018), (statement of David J. Berteau, President and CEO of the Professional Services Council), source.
- Mark Warner, “We Need Revolution, Not Just Evolution in Security Clearances,” The Cipher Brief, February 2, 2018, source.
- Judy Woodruff, “White House security clearance process ’broken,’ says top Trump intelligence official,” PBS Newshour, February 13, 2018, source.
- Personnel Security Clearances: Additional Actions Needed to Ensure Quality, Address Timelines, and Reduce Investigation Backlog, U.S. Government Accountability Office (GAO), December 12, 2017, source.
- Personnel Security Clearances: Plans Needed to Fully Implement and Oversee Continuous Evaluation of Clearance Holders, U.S. Government Accountability Office, November 21, 2017, 2, source.
- Jason Miller, “DoD to bring more employees with ‘critical positions’ under continuous evaluation,” The Federal News Radio, September 21, 2017, source.; Nicole Ogrysko, “ODNI developing comprehensive continuous evaluation capabilities for agencies in 2018,” Federal News Radio, November 17, 2017, source.
- Martin Giles, “Cybersecurity’s insidious new threat: workforce stress,” MIT Technology Review, August 7, 2018, source.
- Roman V. Yampolskiy, “AI is the future of Cybersecurity, for Better and for Worse,” Harvard Business Review, May 8, 2017, source.
- “Staffing the IT Security Function in the Age of Automation,” The Ponemon Institute sponsored by DomainTools, May 2018, source.
- Matthew Goldstein, “Private Sector Pay Lures F.B.I.’s Hacking Experts,” New York Times, July 21, 2015, source.; Rachel King, “MasterCard Sues Nike and Its Former CISO Over Poaching,” The Wall Street Journal, January 12, 2015, source.; Simone Petrella, “NIST Cybersecurity Workforce RFI,” CyberVista, August 1, 2017. 3, source.
