Table of Contents
- Executive Summary
- Background
- Civilian Cyber Corps (C3s) to the Rescue
- Existing Legal Frameworks Governing Civilian Cyber Corps
- Key Issues Presented by Existing C3 Laws
- Conclusion
- Appendix 1. Civilian Cyber Corps Overview
- Appendix 2. Key Legal Provisions for State Civilian Cyber Corps (“C3”) Laws
- Appendix 3. Model Civilian Cyber Corps (C3) Law
Civilian Cyber Corps (C3s) to the Rescue
What Are C3s?
Although not a panacea, civilian cyber corps (C3s) are part of the solution to the national cyber insecurity problem. A C3 is a group of volunteer cybersecurity professionals who provide preventive and reactive cybersecurity services to beneficiaries. A C3 can be organized and can operate under the authority of a government, nonprofit, or for-profit entity, or under a consortium of organizations.
“Although not a panacea, civilian cyber corps (C3s) are part of the solution to the national cyber insecurity problem….Cyber volunteerism is a strength of the system, not a bug.”
The services cyber volunteers provide typically include: (1) education and training; (2) vulnerability and risk assessments; (3) on-call expertise, incident response, and recovery efforts.1 C3s are similar to volunteer organizations in other domains, such as the Civil Air Patrol, Coast Guard Auxiliary, Medical Reserve Corps, and volunteer firefighters. Cyber volunteerism is a strength of the system, not a bug, and we should ask why cyber volunteer organizations have not yet received more support. The cost of failing to significantly expand the support for cyber volunteer organizations in the United States is too high to ignore.
An Overview of C3s in the U.S. and Estonia
C3s in the U.S.
Volunteers have been essential to defending cyberspace since the early days of the internet. In 1990, the Forum of Incident Response and Security Teams, Inc. (FIRST) was formed as a nonprofit comprised of public and private sector members to improve collaboration between incident response teams and security researchers to more efficiently respond to cybersecurity incidents. Since then, volunteers have successfully defended organizations and individuals against cyber threats, including through various information sharing and analysis centers (ISACs); the DNS Operations, Analysis, and Research Center (DNS-OARC); and NSP-Security (NSP-SEC), to name a few. In fact, in 2007, when Russian cyber attacks impacted broad swathes of the country of Estonia, volunteers from NSP-SEC were called on to help stop the attackers.2
The earliest example in the United States of a government-led C3 was the National Emergency Technology Guard (NET Guard), established by the Homeland Security Act of 2002.3 NET Guard emerged after the terrorist attacks of September 11, 2001, when “companies told [Senator (D-O.R.)] Wyden they wanted to help New York City…and there was no system for using their volunteers.” Intended to be a national group of volunteers with expertise to support cybersecurity incident response, NET Guard ultimately failed due to lack of funding, prioritization, and other issues.4
Recently, however, the U.S. government has revisited the concept of a federal C3. In 2019, the U.S. Marine Corps created its own Cyber Auxiliary, a group of civilian volunteers working to help boost the Marine Corps’ cyberspace readiness. In 2022, Congress included a requirement for assessing the feasibility of maintaining a federal C3 in the National Defense Authorization Act (NDAA) for Fiscal Year 2023 and included provisions granting authority for the Secretary of the Army to establish a pilot C3 program in the NDAA for Fiscal Year 2024. To date, however, it appears that no federal assessment was completed, and no concrete actions have been taken toward launching a pilot program.5 While the federal government continues to explore a national C3, Congress could support state-level C3s by allocating funds to CISA, which could either be distributed directly to state C3s or used to develop resources supporting their operations. The federal government can also play an essential role in the volunteer ecosystem by providing training, coordinating efforts, and facilitating data collection and information sharing among stakeholders, as CISA has done with the High-Risk Communities Portal.6 Further, continued federal investment in the National Guard’s cybersecurity capabilities is critical. The National Guard is well-positioned to assist state and local entities with cybersecurity efforts and it already does so in a number of states, even those with established C3s.7
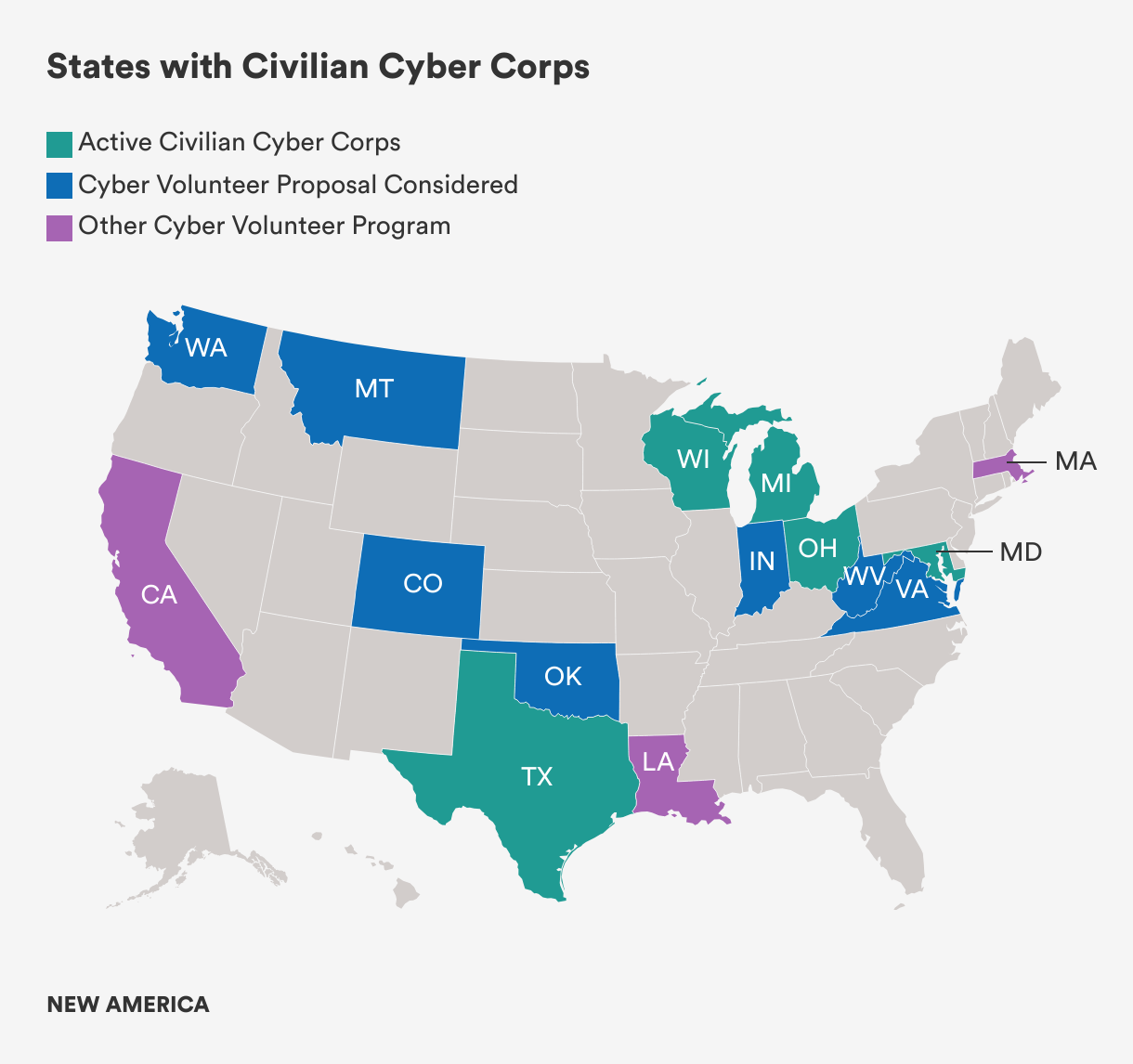
While federal action has stalled, states have established C3s (see Appendix 1). First, in 2010, Maryland established a Cyber Security Unit (CYSEC) within the Maryland Defense Force, a volunteer force that supports the state’s National Guard and emergency management agency. Then, in 2013, Michigan established the Michigan Cyber Civilian Corps (MiC3) “to provide mutual aid to all levels of government, education, and business organizations in the State of Michigan in the event of a critical cyber incident.”8 In 2014, Wisconsin utilized funding from the U.S. Department of Homeland Security (DHS) to establish a volunteer Cyber Response Team (CRT). In 2019, Ohio formed the Ohio Cyber Reserve (OhCR) to engage in (1) outreach, training, and education (including for K–12 education efforts); (2) security assessments to reduce vulnerabilities and increase resiliency; and (3) response to cyber incidents at eligible governmental and critical infrastructure entities. Most recently, in 2021, Texas established the Texas Volunteer Incident Response Team (VIRT) to support state and local government entities in response to critical cybersecurity incidents.

Courtesy of the Wisconsin Department of Emergency Management, used with permission.
Other states have organized cyber volunteers and similar initiatives as well. Oklahoma is in the process of developing the Oklahoma Civilian Cyber Corps (OKC3), a public grant-funded initiative to establish a dedicated volunteer team to provide incident response assistance to public entities in the state. In Massachusetts, in addition to existing cybersecurity programs such as the Municipal Cyber Association, the state is developing security operations centers and cyber ranges at various colleges and universities to improve local cyber resiliency and promote diversity in the cybersecurity workforce. California maintains a Cybersecurity Integration Center comprised of personnel from various state agencies and tasked with sharing threat intelligence and providing incident response services. Several other U.S. states, including Colorado, Hawaii, Indiana, Montana, South Carolina, Washington, West Virginia, and Virginia have considered establishing C3s.9
To date, the utilization of existing state-level C3s varies widely. At least one has yet to be activated for incident response, while others consistently support beneficiaries in responding to cybersecurity incidents. The Ohio Cyber Reserve provides examples of how states utilize these organizations. It has delivered statewide cybersecurity training and education, such as seminars to help school districts harden their IT networks and cybersecurity audits of municipalities.10 Additionally, it helped develop online cybersecurity resources for Ohio residents and supported the Ohio Cyber Range Institute, a training facility, to develop and execute a pilot exercise.11
The Ohio Cyber Reserve has also provided incident response services on a number of occasions. In June 2024, the City of Cleveland fell victim to a ransomware attack that required some City services to be taken offline and led to the closure of City Hall. In that case, the Ohio Cyber Reserve assisted the FBI in responding to the incident and helping restore city services.12 The next month, following a ransomware attack on the City of Columbus that resulted in the theft of residents’ personal information and the disruption of city services, Columbus engaged the Ohio Cyber Reserve, which assisted with incident response efforts and provided recommendations to help mitigate the risk of similar attacks in the future.
C3s in Other Countries: An Example from Estonia
Outside of the United States, countries such as Estonia, Sweden, Switzerland, and others utilize C3s as part of a whole-of-society approach to defend against cyber threats. Estonia’s C3 has been studied more in-depth than others and often serves as a model for other jurisdictions.13 Estonia provides a useful case study for U.S. states seeking to establish C3s and develop C3 statutes because Estonia has codified its C3 in national laws and maintained the C3 for over a decade.
Beginning in 2009, following widespread Russian cyber attacks on its critical infrastructure, Estonia formed the Cyber Defence Unit (CDU) within the country’s Defense League, a volunteer national defense organization within Estonia’s military structure. The CDU’s mission is “to protect Estonia’s high-tech way of life, including protection of information infrastructure and supporting broader objectives of national defense.”14 Its objectives include: (1) developing cooperation among qualified volunteer IT specialists; (2) increasing cybersecurity knowledge and awareness, especially relating to critical infrastructure; (3) creating a network to facilitate public-private partnerships to enhance preparedness in operations during a crisis; (4) information security education and training; and (5) participating in international cybersecurity training events.
The CDU’s staff consists of both paid employees and volunteers who support military or cyber civil defense efforts to ensure continuity of critical infrastructure and essential services or to counteract threats.15 Because the CDU is part of the Estonian Defence League, its legal status and other matters are addressed under laws governing the Defence League, including the Constitution of the Republic of Estonia, the Peacetime National Defence Act, the Wartime National Defence Act, and the Estonian Defence League Act.
The Benefits & Challenges of C3s
Benefits
Utilizing volunteers to provide cybersecurity services presents several benefits to a diverse range of stakeholders, including state and federal governments, cyber volunteers and their employers, those who benefit from the volunteer services, and the general public.
First, cyber volunteers can reduce the costs of cybersecurity incidents to governments and taxpayers. States currently spend significant taxpayer funds to recover from cybersecurity incidents. As an example, in 2023, New York State responded to 57 cybersecurity incidents across the state that cost over $775 million.16 Cyber volunteers will help to reduce those costs directly by providing services that state, local, tribal, and territorial governments (SLTTs) and small- and medium-sized business (SMBs) currently pay third parties to provide and, indirectly, by helping to reduce the likelihood and severity of cybersecurity incidents. States with C3s, like Ohio and Wisconsin for example, have deployed them to provide incident response services in situations that would otherwise require the support of third-party service providers. While more data collected from state C3s will help to better calculate the savings they generate—estimated to be around $1 million annually—just a few deployments could justify the cost of a C3.
“In 2023, New York State responded to 57 cybersecurity incidents across the state that cost over $775 million.”
Second, C3s can improve a state’s cyber resiliency by delivering education and training to beneficiaries and identifying vulnerabilities, risks, and remediation recommendations for them. The National Guard has made efforts to fill that role in some states, but as of March 2024, counted only around 2,000 Guardsmen trained in cybersecurity.17 There are over 33 million small businesses in the U.S.,18 so to provide outreach to just 10 percent of small businesses (let alone medium-sized businesses or SLTT entities) would require each of the Guardsman trained in cybersecurity to engage with 1,650 businesses. C3s can augment work the National Guard already does in some states by providing cybersecurity education and training to increase the cybersecurity posture of SLTT and SMB entities. C3s can also conduct assessments, provide remediation recommendations, and in some cases, assist with implementation of those remedial measures, to reduce the potential attack surface cyber attackers have available to target.
Third, C3s are a resource to provide support in the event of a cyber emergency. Following the terrorist attacks of September 11, 2001, companies reported being unable to effectively deploy volunteers to assist recovery efforts due to a lack of coordination.19 A similar issue arose a decade later during Hurricane Sandy, when over 900 people from the New York start-up community volunteered to provide IT assistance to help those impacted in New York City and along the East Coast but could not contribute because of a lack of coordination.20 To avoid the problems of coordination, and given the widespread threats to critical infrastructure and essential services, it is important to organize cyber volunteers through a formal entity like a C3 before a disaster occurs. Volunteers will be necessary to mitigate harm and decrease recovery times for SLTTs and SMBs in the event of a large-scale cyber attack. Maintaining C3s will allow states to have volunteer structures ready to provide assistance as soon as an emergency arises.
Fourth, C3s can grow and enhance a state’s cybersecurity workforce, while working to fill the workforce gap faced by SLTTs and SMBs. Although some states count a significant number of cybersecurity professionals among their residents, SLTT entities struggle to compete with private-sector employers to hire them. The workforce shortage is especially significant for small and rural municipalities with smaller populations and limited budgets for recruiting cyber talent. Volunteers can fill a critical gap in those locations. Once volunteers have been recruited to join a C3, states provide training and, in some cases, access to free or discounted cybersecurity certifications. These measures not only enhance volunteers’ skill sets, but also allow them to utilize these newly acquired skills for the benefit of their employers. In fact, according to Newsweek, several leading U.S. cyber executives have expressed interest in the possibility of a “cyber reserve.”21 This could also be useful to recruit more professionals into a state’s cyber workforce. The Ohio Cyber Reserve highlights benefits such as training, education, and leadership opportunities as benefits of joining.22 Ohio Cyber Reserve members train with the Ohio National Guard on a state-of-the-art cyber range, and that infrastructure is also used to educate and train university students and others.
Lastly, C3s provide the intangible benefits of community building and civic engagement. Speaking at the DEF CON 32 hacking conference, former White House Acting Principal Deputy National Cyber Director Jake Braun noted, “This is a community of people that is deeply interested in civil society and democracy…and giving back to their community.”23 In line with this observation, the Ohio Cyber Reserve promotes networking opportunities, mentorship, awards, and community support and recognition as benefits of membership.24 In a field with a workforce shortage and high burn-out rates, the opportunity to network, gain professional skills, learn from mentors and peers, and help the local community is an important draw of C3s. Taken together, these intangible benefits will help states to retain an adequate cybersecurity workforce and may even attract new and emerging talent to the cybersecurity field.
Challenges
C3s also present several challenges for these stakeholders, which must be addressed in the legal framework governing the entity. This section explains some of the key legal issues that arise when states look to use the services of civilian cyber volunteers. Appendix 2 provides a list of key legal provisions that should be included in C3 laws to address those issues, while Appendix 3 incorporates the key legal provisions in a Model C3 Law that states can use to develop their own C3 laws.
First, securing the necessary funding to form and maintain a C3 can be a challenge for states. Based on existing C3s, the amount required for minimum efficient operating levels is around $1 million annually. States like Wisconsin and Oklahoma have utilized federal DHS grants to form C3s, while others—like Maryland, Ohio, and Texas—have relied on state budgets. As part of the proposal for a state C3, legislatures may need to propose a funding source. Federal grants, like the State and Local Cybersecurity Grant program administered by CISA may help, but without further congressional action, that funding will soon cease.25 To scale this solution and support it over the long term, states must identify ongoing funding sources.
Second, states must develop and implement a legal framework to establish clear roles and responsibilities, allocate liability, ensure confidentiality, and establish rules for collaboration with other entities (including other states’ C3s), among other concerns. A statement issued by Virginia’s Governor vetoing a bill that would have required an assessment of the feasibility of a state C3, highlighted “continued financial obligations, background checks, liability protections, and ongoing recruitment” as well as potential conflicts with the National Guard’s duties as issues to be addressed before forming a C3.26 Other states considering developing C3s will have similar concerns, but because of differing legal, political, and cultural environments, what works in one state may not be directly transferable to another. A related issue arises from the use of cyber volunteers with respect to collaboration across entities within a state, between states, or with the federal government. Those engagements are typically carried out under MOUs that specify the scope of responsibilities. A similar structure can be utilized for C3s, but this issue should also be addressed in the relevant C3 law to make clear that MOUs should be used for this purpose.
Third, states may find it difficult to identify, recruit, and vet volunteers and employers, especially SMBs. This is one of the challenges highlighted by Virginia’s Governor after vetoing a bill to assess the feasibility of a C3 in Virginia. Given the shortage of cybersecurity professionals, it may be difficult, especially in certain states or regions with lower populations, to recruit sufficient personnel who meet the states’ required qualifications. Requirements that are too stringent could also prevent talented cybersecurity professionals from being able to provide support. In addition, some volunteers may be concerned about the risk that hackers target them or their employers because of their volunteer work.27 It is important to draft C3 requirements in a way that accounts for the varying backgrounds and qualifications of potential volunteers. In addition, states have found several creative solutions to vet potential volunteers. Wisconsin’s Cyber Response Team prefers applicants who are members of InfraGard—a partnership between the FBI and the private sector designed to protect critical infrastructure sectors—because those applicants will have completed a federal background check.28
A fourth challenge presented by C3s is that of raising awareness about the existence of and services offered by the C3 so that beneficiaries can meaningfully engage them for support. When C3s are formed, potential beneficiaries will not know the C3’s services are available to them, and governments may have difficulty identifying beneficiaries or establishing a realistic scope of services.29 It will be incumbent on C3s to market their offerings to potential beneficiaries and to provide easy means for those in need of these services to engage them. Existing C3s have identified this as an early challenge, but one that can be overcome through outreach and preventive services, such as education, training, and vulnerability and risk assessments. For example, the Ohio Cyber Reserve engages in proactive outreach to beneficiaries and education and training for K–12 schools. The Wisconsin Cyber Response Team proactively engages with beneficiaries to educate them about the Cyber Response Team’s services.

Courtesy of Wisconsin Emergency Management, used with permission.
A fifth challenge involves understanding the interaction between cyber insurance carriers and C3s during cybersecurity incident response. A reliable estimate of the number of local governments across the U.S. with cyber insurance coverage is not available, but as of 2023, only 53 percent of small businesses have cyber insurance coverage.30 For SLTTs and SMBs that do not have cyber insurance coverage, C3s can help to make coverage more accessible by providing education, training, risk and vulnerability assessments, and remediation support, which insurers will review as part of the application process. For SLTTs and SMBs that do have cyber insurance, their insurers will offer a panel of service providers for pre-incident risk assessments and incident response, including law firms, digital forensics and incident response firms, public relations agencies, call centers, credit monitoring services, data recovery and restoration companies, and ransomware negotiators. However, even for those organizations that have insurance, C3s can provide education, training, and risk and vulnerability assessments that insurance does not cover. Further, those organizations may still need C3 support in the event of a cybersecurity incident where the costs are below the organizations’ retention limits or are likely to exceed their aggregate policy coverage, or in cases where coverage is excluded. C3s should proactively engage with and educate cyber insurance carriers and beneficiaries about the C3s’ services to align on the circumstances under which C3s can be most effectively utilized.
Lastly, the nature, length, and timing of deployments could present challenges. Volunteers deployed for extended engagements may have other personal or professional conflicts. If volunteers are not regularly utilized or provided opportunities for engagement through the C3, volunteer participation is likely to wane and future recruitment might become more difficult. Because C3s are volunteer-driven, those concerns cannot be overlooked, and C3s will need to develop enough capacity to account for times when volunteers are not available. C3s will also need to regularly meet and train to sustain engagement and readiness.
Citations
- See Cohen and Singer, The Need for C3, source.
- Jason Healey, “Ukrainian Cyber War Confirms the Lesson: Cyber Power Requires Soft Power,” Council on Foreign Relations (blog), April 4, 2023, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 3, source.
- “Wyden Releases Hold After FEMA Announces NET Guard Pilot Program,” U.S. Senate, June 19, 2008, source.
- “Open/Closed: Hearing Title to Receive Testimony on the Posture of the Department of the Army in Review of the Defense Authorization Request for Fiscal Year 2025 and the Future Years Defense Program,” U.S. Senate Committee on Armed Services, Apr. 18, 2024, 02:17:00, video, source.
- “High Risk Communities,” CISA, accessed Aug. 31, 2024, source.
- Skylar Rispens, “National Guard Ready to Assist States with Cyber Response, Say Officials,” StateScoop, Mar. 20, 2024, source.
- “About MiC3,” Department of Technology, Management & Budget, accessed August 25, 2024, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 32, source.
- Cynthia Brumfield, “Civilian Cyber Reserves Gaining Steam at the Federal and State Levels,” CSO Online, January 24, 2024, source.
- Dolen, “Re-Envisioning State Cyber Response Capabilities,” source.
- Nate Castele, “‘Cyber Incident’ Closes Cleveland City Hall for Public Business Thursday and Friday; City in Contact with FBI and Ohio Cyber Reserve,” Signal Cleveland, June 12, 2024, source.
- Maggie Smith et al., “Taking the Elf Off the Shelf: Why the U.S. Should Consider a Civilian Cyber Defense,” Lawfare Institute, July 6, 2022, source.
- Estonian Defence League’s Cyber Unit, Estonian Defense League [KAITSELIIT], source.
- Eneken Tikk, “Civil Defence and Cyber Security: A Contemporary European Perspective,” in National Cyber Emergencies: The Return to Civil Defense, ed. Greg Austin (New York: Routledge, 2020), 86.
- James Rundle, “New York State Debuts First Cybersecurity Strategy,” Wall Street Journal, August 9, 2023, source.
- Rispens, “National Guard Ready to Assist States,” source.
- Office of Advocacy, “Frequently Asked Questions about Small Business, 2023,” U.S. Small Business Administration, March 7, 2023, source.
- U.S. Senate, “Wyden Releases Hold After FEMA Announces NET Guard Pilot Program,” source.
- Monica Ruiz, “Is Estonia’s Approach to Cyber Defense Feasible in the United States?,” War on the Rocks (blog), January 9, 2018, source.
- Shaun Waterman, “Ukraine Scrambles to Draft Cyber Law, Legalizing Its Volunteer Hacker Army,” Newsweek, March 13, 2023, source.
- “Join OhCR,” Ohio Cyber Reserve, accessed August 17, 2024, source.
- Jake Braun, “DEF CON 32 – Jake Braun – DEF CON Franklin Project,” August 10, 2024, at 12:29, video, source.
- Ohio Cyber Reserve, “Join OhCR,” source.
- Colin Wood, “States Urge Congress Not to Claw Back Cybersecurity Grant Funding,” State Scoop, June 4, 2024, source.
- 2024 Session Governor’s Veto, HB651, Virginia’s Legislative Information System, accessed August 25, 2024, source.
- Mehul Srivastava, “Cyber Security Researchers Become Target of Criminal Hackers,” Financial Times, August 17, 2023, source.
- See Wisconsin Cyber Response Team, Wisconsin Emergency Management, accessed August 17, 2024, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 10–11, source.
- Hiscox Cyber Readiness Report 2023 US Small Business Focus, Hiscox, 2023, 7, source.