Civilian Cyber Corps: A Model Law for States
Table of Contents
- Executive Summary
- Background
- Civilian Cyber Corps (C3s) to the Rescue
- Existing Legal Frameworks Governing Civilian Cyber Corps
- Key Issues Presented by Existing C3 Laws
- Conclusion
- Appendix 1. Civilian Cyber Corps Overview
- Appendix 2. Key Legal Provisions for State Civilian Cyber Corps (“C3”) Laws
- Appendix 3. Model Civilian Cyber Corps (C3) Law
Abstract
State and local government (“SLTTs”) and small and medium-sized businesses (“SMBs”) across the United States are routinely targeted by cyber criminals because SLTTs and SMBs manage critical infrastructure and deliver essential services. The societal impacts of those cyber attacks continue to increase exponentially while SLTTs and SMBs struggle to manage the proliferation of insecure software amid a significant cybersecurity workforce shortage. In the past several years, volunteer cybersecurity professionals have stepped in to fill the gap. Additionally, some state governments have established civilian cyber corps (“C3s”)—organizations to facilitate cyber volunteer services—similar to other civil defense organizations, like the Coast Guard Auxiliary and the Civil Air Patrol. More states are considering C3s to help address cyber workforce challenges, improve their cyber resiliency, and develop cyber emergency response capabilities. The laws that apply to C3s can help or hinder their effectiveness. This report examines the current state of C3s in the United States and the laws that govern them, providing key legal provisions and a model C3 law to guide states to build C3s on a solid legal foundation as a replicable, scalable solution to a large-scale societal problem.
Acknowledgments
The author thanks all of the individuals and organizations who contributed to and supported this research. This report would not have been possible without your contributions.
Editorial disclosure: The views expressed in this report are solely those of the author(s) and do not reflect the views of New America, its staff, fellows, funders, or board of directors.
Downloads
Executive Summary
Several states have established volunteer civilian cyber corps (C3s) to fill critical cybersecurity workforce gaps, strengthen the defenses of state and local government agencies, and enhance cyber emergency response capabilities. This report (1) explores the growing need for C3s in response to today’s escalating cybersecurity threats; (2) examines the development of C3s in the United States, as well as in Estonia, which serves as a more mature example; (3) analyzes key legal provisions and challenges in existing state C3 laws; and (4) offers a list of key legal provisions and a Model C3 Law to guide states in forming their own C3s.1
Using volunteers for cybersecurity services is necessary but raises certain legal issues. This report provides ways to address those issues by law so that states can focus on operational concerns related to developing and maintaining C3s.
Insecure software and a significant workforce shortage have contributed to a state of cyber insecurity across the public and private sectors in the U.S. In 2023, nearly 29,000 common vulnerabilities and exploits (CVEs)—weaknesses in software that a malicious actor can exploit—were recorded.2 Meanwhile, there aren’t enough cybersecurity professionals to help mitigate the risks posed by those CVEs. As of early 2024, around 470,000 cybersecurity job openings remain unfilled.3 The consequences of this problem are especially significant for state, local, tribal, and territorial governments (SLTTs) and small- and medium-sized businesses (SMBs), which operate critical infrastructure and provide essential services, such as electricity, sewerage and water treatment, healthcare, and education.4 SLTTs and SMBs require much more support than they currently receive to improve their cybersecurity posture and resilience.
Following the examples of other countries, like Estonia, Sweden, Switzerland, and others, the U.S. must take a whole-of-society approach to cybersecurity. An ecosystem of public and private organizations is emerging to support such an approach that includes university cybersecurity clinics like the UC Berkeley Cybersecurity Clinic; volunteer efforts coordinated by nonprofits like the CyberPeace Institute; and volunteer civilian cyber corps (C3s) formed by governments to augment their cyber workforce and bolster emergency response capabilities.5 The U.S. relies on the support of volunteers in other domains, such as the Civil Air Patrol, the Coast Guard Auxiliary, the Medical Reserve Corps, and Volunteer Firefighters, and the U.S. needs the support of volunteer C3s in the cyber domain.
Of those cyber volunteer initiatives, state government-led C3s present the best option for long-term, replicable, and scalable services to support SLTTs and SMBs through education and training, vulnerability and risk assessments, and post-incident recovery. State C3s can cost around $1 million annually, so only a few deployments can offset costs that SLTT and SMB entities would otherwise spend on third-party services. Although the U.S. government has explored the idea of a federal C3, several U.S. states have already led the way and established C3s over the past few years. Each state has developed its own legal framework—including statutes, contracts, memoranda of understanding (“MOUs”), and rules or guidance—to govern the C3. These frameworks help address and clarify issues such as the authority to operate, volunteer eligibility, funding, volunteer deployment, liability protections for volunteers, confidentiality obligations, and more. With legal issues addressed, states can shift their focus to operational issues, ensuring the delivery of cybersecurity services to those in need.
Citations
- Together with a model contract published in a recent C3 report by the law firm McDermott, Will, and Emery, LLP, states now have the foundations to establish a legal framework to govern C3s. See Mark E. Schreiber et al., Creating a Cyber Volunteer Force: Strategy and Options (Boston, MA: McDermott, Will, and Emery, LLP, 2023), 54–64, source.
- “Metrics: Published CVE Records,” CVE, accessed August 31, 2024, source.
- “Cybersecurity Supply/Demand Heat Map,” Cyber Seek, accessed June 16, 2024, source.
- See Cyrus R. Vance, Elizabeth Roper, and Justine Phillips, “Cybercriminals Have Small Town, USA, in Their Crosshairs: How to Fight Back,” The Hill, February 15, 2024, source.
- See UC Berkeley Cybersecurity Clinic, UC Berkeley Center for Long-Term Cybersecurity, accessed August 25, 2024, source; IU Cybersecurity Clinic, Indiana University, accessed August 25, 2024, source; “Cybersecurity for Social Impact,” CyberPeace Builders, accessed August 16, 2024, source; Casey Dolen, “Re-Envisioning State Cyber Response Capabilities: The Role of Volunteers in Strengthening our Systems,” National Governors Association (Washington, DC: June 16, 2022), source.
Background
In 2023, over 880,000 cyber crimes in the U.S. resulted in around $12.5 billion in losses, according to the FBI’s Internet Crimes Complaint Report.1 Ransomware attacks alone directly impacted at least 2,200 hospitals, schools, and governments across the U.S. that year.2 Those estimates almost certainly undercount the problem’s scope because it is likely that a number of cybersecurity incidents go unreported. In addition to financially motivated crimes, politically motivated cyber attacks also represent significant concerns. In early 2024, the Cybersecurity and Infrastructure Security Agency (CISA) reported that a foreign state-sponsored cyber actor was discovered to have maintained access to critical infrastructure systems across the U.S., in some cases, for as long as five years.3
While the cyber threat landscape continues to evolve rapidly, the number of cybersecurity professionals needed to defend against those threats has not kept pace. In mid-2024, cybersecurity job openings numbered around 470,000.4 By one estimate, the U.S. would need to train 40 percent of all people entering the workforce in cybersecurity over the next seven years to meet the growing cyber workforce gap.5 However, efforts to increase the size of the cybersecurity workforce, even if successful, are unlikely to be sufficient to meet that goal. In a 2023 congressional hearing, Representative Mike Gallagher (R-W.I.) remarked, “Since 2013… we have tried to address the civilian and military cyber workforce dilemma 45 times… And the country’s collective capabilities and readiness are, seemingly, no better off because of it.”6 In addition to the cybersecurity workforce shortage, software developers continue to develop insecure software, increasing the burden and potential vulnerability of under-resourced organizations who utilize the software.7 In 2023, nearly 29,000 common vulnerabilities and exploits (CVEs), which are weaknesses in software that can be exploited, were recorded.8
“By one estimate, the U.S. would need to train 40 percent of all people entering the workforce in cybersecurity over the next seven years to meet the growing cyber workforce gap.”
In the United States, those under-resourced organizations are often state, local, tribal, and territorial governments (SLTTs) and small- and medium-sized businesses (SMBs), which operate much of the country’s critical infrastructure and provide many essential services. For example, according to CISA, there are “approximately 153,000 public drinking water systems and more than 16,000 publicly owned wastewater treatment systems in the United States.”9 SLTTs and SMBs must navigate the same cyber threat landscape as the federal government and global corporations, but with far fewer resources.10 According to a 2023 report from NetDiligence, the average cost of cyber incidents for SMBs in the five years leading up to 2023 (excluding business interruption and certain other costs) was over $1 million.11
Examples from recent years highlight the total costs of cybersecurity incidents. For instance, a 2018 ransomware attack on the City of Atlanta, Georgia, resulted in costs estimated to be around $17 million.12 A 2019 ransomware attack on the City of Baltimore, Maryland, cost taxpayers over $18 million,13 and a 2022 ransomware attack on Suffolk County, New York, resulted in costs estimated as high as $25 million.14 More recently, a 2023 ransomware attack on Dallas County, Texas, resulted in around $8.6 million in costs for recovery efforts, including the purchase and installation of new devices and equipment; temporary staff; credit monitoring and identity theft protection services; call center support; forensic accounting; application and system recovery; and software licenses.15
In the private sector, according to one survey, 60 percent of companies go out of business within six months of a significant cyber attack.16 The same study notes that 30 percent of SMBs do not have a written information security incident response plan; 21 percent of SMBs do not have backup copies of data sufficient to restore systems following a cyber attack; and only 28 percent would survive beyond seven days after a ransomware attack taking their operations offline.17
To date, the U.S. has not taken adequate measures to defend SLTTs and SMBs against cyber attacks. However, a cyber volunteer ecosystem is emerging to fill the gap. In some states, universities have established cybersecurity clinics where professors and students work to improve the cyber resiliency of SLTTs and SMBs and train the next generation of cybersecurity professionals.18 Across the U.S., nonprofit organizations, like the Cyber Peace Institute and, recently, DEFCON’s Project Franklin, have created opportunities for cybersecurity professionals to volunteer to assist beneficiaries with cybersecurity needs.19
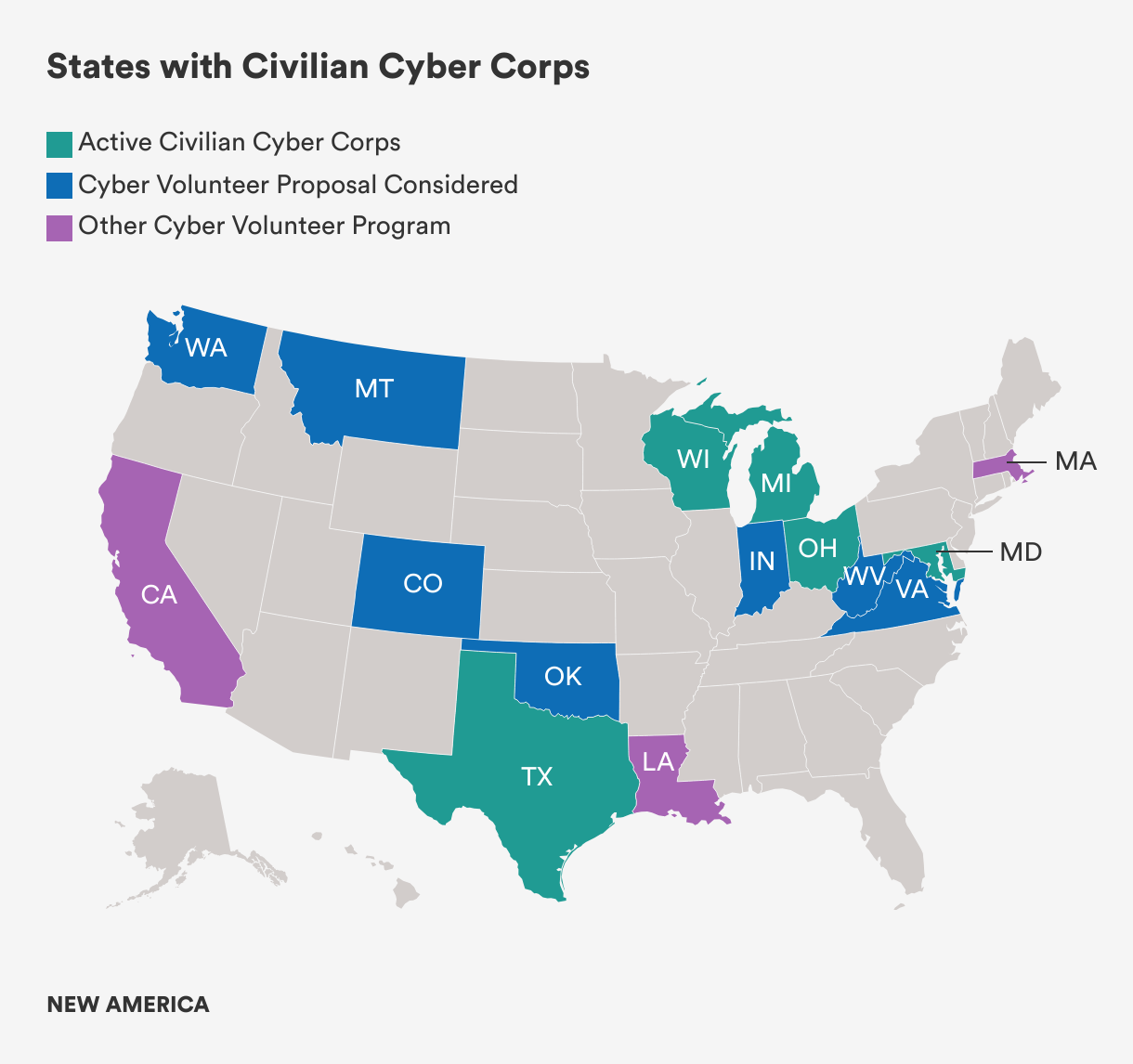
Government entities have also taken action. At the federal level, the U.S. Marine Corps established a Cyber Auxiliary to provide education and training to the Marine Corps. Meanwhile, state governments have established volunteer civilian cyber corps (C3s) to improve the resiliency of SLTT entities within their borders. Maryland, Michigan, Wisconsin, Ohio, and Texas have formed C3s to provide cybersecurity services to beneficiaries. Other states are considering this option as a replicable and scalable solution to help address cyber workforce challenges, improve cyber resiliency, and develop cyber emergency response capabilities accessible to local entities. Outside the United States, countries such as Estonia, Sweden, Switzerland, and others already take a whole-of-society approach to cybersecurity and utilize civilian cyber volunteers.
Citations
- FBI, Internet Crimes Complaint Report 2023 (Washington, DC: FBI, 2023), 3, source.
- Emsisoft Malware Lab, The State of Ransomware in the U.S.: Report and Statistics 2023 (Emsisoft: 2024), source.
- Cybersecurity and Infrastructure Security Agency, PRC State-Sponsored Actors Compromise and Maintain Persistent Access to U.S. Critical Infrastructure (Washington, DC: Cybersecurity & Infrastructure Security Agency, 2024), source.
- Cyber Seek, “Cybersecurity Supply/Demand Heat Map,” source.
- Nick Merrill, “The Cybersecurity Workforce Has an Immigration Problem,” Tech Policy Press, August 9, 2024, source.
- Mike Gallagher, “Cyberspace Operations: Conflict in the 21st Century,” Hearing before the House Armed Services Committee, Cyber, Information Technologies, and Innovation Subcommittee, March 30, 2023, 23:19, source.
- See Christian Vasquez, “Easterly: Cybersecurity Is a Software Quality Problem” CyberScoop, August 9, 2024, source.
- CVE, “Metrics: Published CVE Records,” source.
- “Water & Wastewater Systems,” CISA, accessed August 25, 2024, source.
- Natasha Cohen and Peter Warren Singer, The Need for C3: A Proposal for a United States Cybersecurity Civilian Corps (Washington, DC: New America, 2018), source.
- NetDiligence, Cyber Claims Study 2023 Report (NetDiligence, 2024), 17, source.
- Stephen Deere, “Confidential Report: Atlanta’s Cyber Attack Could Cost Taxpayers $17 Million,” Atlanta Journal-Constitution, August 1, 2018, source.
- Adam Bednar, “Cost of Baltimore Ransomware Attack So Far: $18 Million,” Daily Record, June 4, 2019, source.
- Alan J., “Ransomware Recovery Effort Cost Suffolk County $25.7 Million, Prompting Investigation,” Cyber Express, July 22, 2024, source.
- “Data Security Breach Reports,” Attorney General of Texas, accessed Aug. 19, 2024, source.
- Joe Galvin, “60 Percent of Small Businesses Fold within 6 Months of a Cyber Attack. Here’s How to Protect Yourself,” Inc. Magazine, May 7, 2018, source.
- Cybercatch, “Small- and Medium-Sized Businesses Ransomware Survey 2022,” (Cybercatch, 2022), 3, source.
- “What is a Clinic?,” Consortium of Cybersecurity Clinics, accessed August 16, 2024, source.
- See “Cybersecurity for Social Impact,” CyberPeace Builders, accessed August 16, 2024, source; and see Jake Braun, “DEF CON 32 – Jake Braun – DEF CON Franklin Project,” August 10, 2024, YouTube (video), source.
Civilian Cyber Corps (C3s) to the Rescue
What Are C3s?
Although not a panacea, civilian cyber corps (C3s) are part of the solution to the national cyber insecurity problem. A C3 is a group of volunteer cybersecurity professionals who provide preventive and reactive cybersecurity services to beneficiaries. A C3 can be organized and can operate under the authority of a government, nonprofit, or for-profit entity, or under a consortium of organizations.
“Although not a panacea, civilian cyber corps (C3s) are part of the solution to the national cyber insecurity problem….Cyber volunteerism is a strength of the system, not a bug.”
The services cyber volunteers provide typically include: (1) education and training; (2) vulnerability and risk assessments; (3) on-call expertise, incident response, and recovery efforts.1 C3s are similar to volunteer organizations in other domains, such as the Civil Air Patrol, Coast Guard Auxiliary, Medical Reserve Corps, and volunteer firefighters. Cyber volunteerism is a strength of the system, not a bug, and we should ask why cyber volunteer organizations have not yet received more support. The cost of failing to significantly expand the support for cyber volunteer organizations in the United States is too high to ignore.
An Overview of C3s in the U.S. and Estonia
C3s in the U.S.
Volunteers have been essential to defending cyberspace since the early days of the internet. In 1990, the Forum of Incident Response and Security Teams, Inc. (FIRST) was formed as a nonprofit comprised of public and private sector members to improve collaboration between incident response teams and security researchers to more efficiently respond to cybersecurity incidents. Since then, volunteers have successfully defended organizations and individuals against cyber threats, including through various information sharing and analysis centers (ISACs); the DNS Operations, Analysis, and Research Center (DNS-OARC); and NSP-Security (NSP-SEC), to name a few. In fact, in 2007, when Russian cyber attacks impacted broad swathes of the country of Estonia, volunteers from NSP-SEC were called on to help stop the attackers.2
The earliest example in the United States of a government-led C3 was the National Emergency Technology Guard (NET Guard), established by the Homeland Security Act of 2002.3 NET Guard emerged after the terrorist attacks of September 11, 2001, when “companies told [Senator (D-O.R.)] Wyden they wanted to help New York City…and there was no system for using their volunteers.” Intended to be a national group of volunteers with expertise to support cybersecurity incident response, NET Guard ultimately failed due to lack of funding, prioritization, and other issues.4
Recently, however, the U.S. government has revisited the concept of a federal C3. In 2019, the U.S. Marine Corps created its own Cyber Auxiliary, a group of civilian volunteers working to help boost the Marine Corps’ cyberspace readiness. In 2022, Congress included a requirement for assessing the feasibility of maintaining a federal C3 in the National Defense Authorization Act (NDAA) for Fiscal Year 2023 and included provisions granting authority for the Secretary of the Army to establish a pilot C3 program in the NDAA for Fiscal Year 2024. To date, however, it appears that no federal assessment was completed, and no concrete actions have been taken toward launching a pilot program.5 While the federal government continues to explore a national C3, Congress could support state-level C3s by allocating funds to CISA, which could either be distributed directly to state C3s or used to develop resources supporting their operations. The federal government can also play an essential role in the volunteer ecosystem by providing training, coordinating efforts, and facilitating data collection and information sharing among stakeholders, as CISA has done with the High-Risk Communities Portal.6 Further, continued federal investment in the National Guard’s cybersecurity capabilities is critical. The National Guard is well-positioned to assist state and local entities with cybersecurity efforts and it already does so in a number of states, even those with established C3s.7
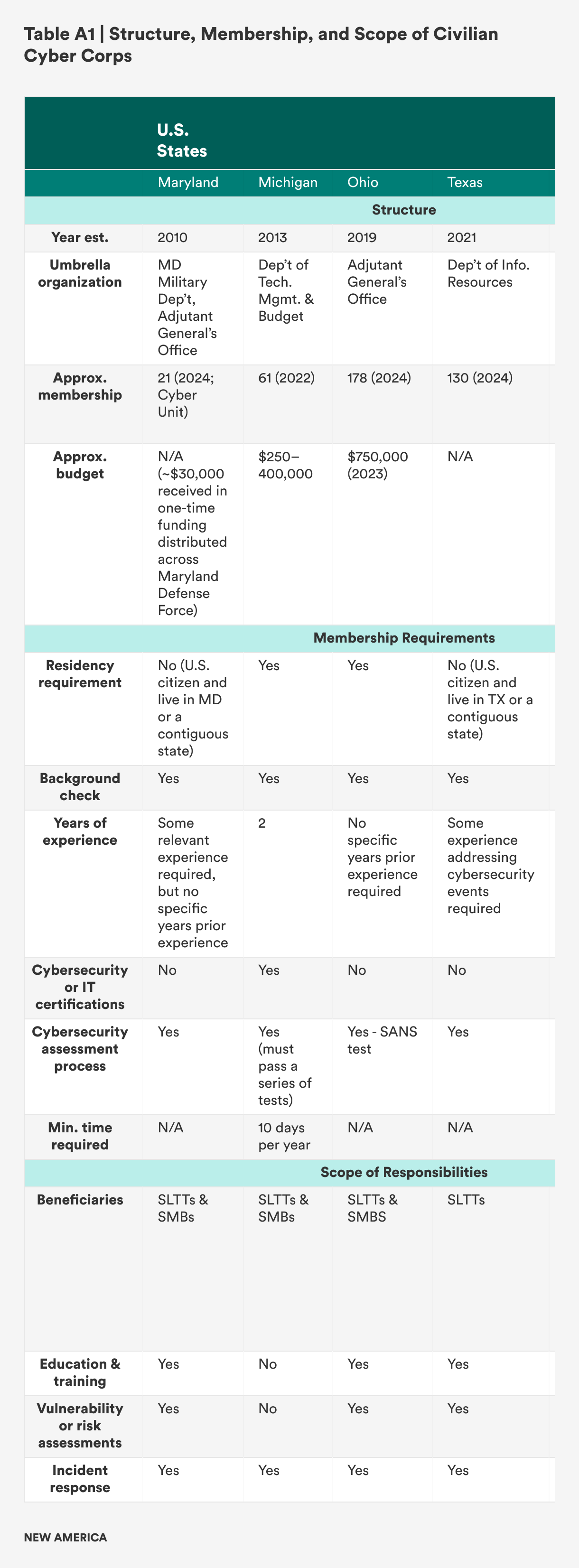
While federal action has stalled, states have established C3s (see Appendix 1). First, in 2010, Maryland established a Cyber Security Unit (CYSEC) within the Maryland Defense Force, a volunteer force that supports the state’s National Guard and emergency management agency. Then, in 2013, Michigan established the Michigan Cyber Civilian Corps (MiC3) “to provide mutual aid to all levels of government, education, and business organizations in the State of Michigan in the event of a critical cyber incident.”8 In 2014, Wisconsin utilized funding from the U.S. Department of Homeland Security (DHS) to establish a volunteer Cyber Response Team (CRT). In 2019, Ohio formed the Ohio Cyber Reserve (OhCR) to engage in (1) outreach, training, and education (including for K–12 education efforts); (2) security assessments to reduce vulnerabilities and increase resiliency; and (3) response to cyber incidents at eligible governmental and critical infrastructure entities. Most recently, in 2021, Texas established the Texas Volunteer Incident Response Team (VIRT) to support state and local government entities in response to critical cybersecurity incidents.

Courtesy of the Wisconsin Department of Emergency Management, used with permission.
Other states have organized cyber volunteers and similar initiatives as well. Oklahoma is in the process of developing the Oklahoma Civilian Cyber Corps (OKC3), a public grant-funded initiative to establish a dedicated volunteer team to provide incident response assistance to public entities in the state. In Massachusetts, in addition to existing cybersecurity programs such as the Municipal Cyber Association, the state is developing security operations centers and cyber ranges at various colleges and universities to improve local cyber resiliency and promote diversity in the cybersecurity workforce. California maintains a Cybersecurity Integration Center comprised of personnel from various state agencies and tasked with sharing threat intelligence and providing incident response services. Several other U.S. states, including Colorado, Hawaii, Indiana, Montana, South Carolina, Washington, West Virginia, and Virginia have considered establishing C3s.9
To date, the utilization of existing state-level C3s varies widely. At least one has yet to be activated for incident response, while others consistently support beneficiaries in responding to cybersecurity incidents. The Ohio Cyber Reserve provides examples of how states utilize these organizations. It has delivered statewide cybersecurity training and education, such as seminars to help school districts harden their IT networks and cybersecurity audits of municipalities.10 Additionally, it helped develop online cybersecurity resources for Ohio residents and supported the Ohio Cyber Range Institute, a training facility, to develop and execute a pilot exercise.11
The Ohio Cyber Reserve has also provided incident response services on a number of occasions. In June 2024, the City of Cleveland fell victim to a ransomware attack that required some City services to be taken offline and led to the closure of City Hall. In that case, the Ohio Cyber Reserve assisted the FBI in responding to the incident and helping restore city services.12 The next month, following a ransomware attack on the City of Columbus that resulted in the theft of residents’ personal information and the disruption of city services, Columbus engaged the Ohio Cyber Reserve, which assisted with incident response efforts and provided recommendations to help mitigate the risk of similar attacks in the future.
C3s in Other Countries: An Example from Estonia
Outside of the United States, countries such as Estonia, Sweden, Switzerland, and others utilize C3s as part of a whole-of-society approach to defend against cyber threats. Estonia’s C3 has been studied more in-depth than others and often serves as a model for other jurisdictions.13 Estonia provides a useful case study for U.S. states seeking to establish C3s and develop C3 statutes because Estonia has codified its C3 in national laws and maintained the C3 for over a decade.
Beginning in 2009, following widespread Russian cyber attacks on its critical infrastructure, Estonia formed the Cyber Defence Unit (CDU) within the country’s Defense League, a volunteer national defense organization within Estonia’s military structure. The CDU’s mission is “to protect Estonia’s high-tech way of life, including protection of information infrastructure and supporting broader objectives of national defense.”14 Its objectives include: (1) developing cooperation among qualified volunteer IT specialists; (2) increasing cybersecurity knowledge and awareness, especially relating to critical infrastructure; (3) creating a network to facilitate public-private partnerships to enhance preparedness in operations during a crisis; (4) information security education and training; and (5) participating in international cybersecurity training events.
The CDU’s staff consists of both paid employees and volunteers who support military or cyber civil defense efforts to ensure continuity of critical infrastructure and essential services or to counteract threats.15 Because the CDU is part of the Estonian Defence League, its legal status and other matters are addressed under laws governing the Defence League, including the Constitution of the Republic of Estonia, the Peacetime National Defence Act, the Wartime National Defence Act, and the Estonian Defence League Act.
The Benefits & Challenges of C3s
Benefits
Utilizing volunteers to provide cybersecurity services presents several benefits to a diverse range of stakeholders, including state and federal governments, cyber volunteers and their employers, those who benefit from the volunteer services, and the general public.
First, cyber volunteers can reduce the costs of cybersecurity incidents to governments and taxpayers. States currently spend significant taxpayer funds to recover from cybersecurity incidents. As an example, in 2023, New York State responded to 57 cybersecurity incidents across the state that cost over $775 million.16 Cyber volunteers will help to reduce those costs directly by providing services that state, local, tribal, and territorial governments (SLTTs) and small- and medium-sized business (SMBs) currently pay third parties to provide and, indirectly, by helping to reduce the likelihood and severity of cybersecurity incidents. States with C3s, like Ohio and Wisconsin for example, have deployed them to provide incident response services in situations that would otherwise require the support of third-party service providers. While more data collected from state C3s will help to better calculate the savings they generate—estimated to be around $1 million annually—just a few deployments could justify the cost of a C3.
“In 2023, New York State responded to 57 cybersecurity incidents across the state that cost over $775 million.”
Second, C3s can improve a state’s cyber resiliency by delivering education and training to beneficiaries and identifying vulnerabilities, risks, and remediation recommendations for them. The National Guard has made efforts to fill that role in some states, but as of March 2024, counted only around 2,000 Guardsmen trained in cybersecurity.17 There are over 33 million small businesses in the U.S.,18 so to provide outreach to just 10 percent of small businesses (let alone medium-sized businesses or SLTT entities) would require each of the Guardsman trained in cybersecurity to engage with 1,650 businesses. C3s can augment work the National Guard already does in some states by providing cybersecurity education and training to increase the cybersecurity posture of SLTT and SMB entities. C3s can also conduct assessments, provide remediation recommendations, and in some cases, assist with implementation of those remedial measures, to reduce the potential attack surface cyber attackers have available to target.
Third, C3s are a resource to provide support in the event of a cyber emergency. Following the terrorist attacks of September 11, 2001, companies reported being unable to effectively deploy volunteers to assist recovery efforts due to a lack of coordination.19 A similar issue arose a decade later during Hurricane Sandy, when over 900 people from the New York start-up community volunteered to provide IT assistance to help those impacted in New York City and along the East Coast but could not contribute because of a lack of coordination.20 To avoid the problems of coordination, and given the widespread threats to critical infrastructure and essential services, it is important to organize cyber volunteers through a formal entity like a C3 before a disaster occurs. Volunteers will be necessary to mitigate harm and decrease recovery times for SLTTs and SMBs in the event of a large-scale cyber attack. Maintaining C3s will allow states to have volunteer structures ready to provide assistance as soon as an emergency arises.
Fourth, C3s can grow and enhance a state’s cybersecurity workforce, while working to fill the workforce gap faced by SLTTs and SMBs. Although some states count a significant number of cybersecurity professionals among their residents, SLTT entities struggle to compete with private-sector employers to hire them. The workforce shortage is especially significant for small and rural municipalities with smaller populations and limited budgets for recruiting cyber talent. Volunteers can fill a critical gap in those locations. Once volunteers have been recruited to join a C3, states provide training and, in some cases, access to free or discounted cybersecurity certifications. These measures not only enhance volunteers’ skill sets, but also allow them to utilize these newly acquired skills for the benefit of their employers. In fact, according to Newsweek, several leading U.S. cyber executives have expressed interest in the possibility of a “cyber reserve.”21 This could also be useful to recruit more professionals into a state’s cyber workforce. The Ohio Cyber Reserve highlights benefits such as training, education, and leadership opportunities as benefits of joining.22 Ohio Cyber Reserve members train with the Ohio National Guard on a state-of-the-art cyber range, and that infrastructure is also used to educate and train university students and others.
Lastly, C3s provide the intangible benefits of community building and civic engagement. Speaking at the DEF CON 32 hacking conference, former White House Acting Principal Deputy National Cyber Director Jake Braun noted, “This is a community of people that is deeply interested in civil society and democracy…and giving back to their community.”23 In line with this observation, the Ohio Cyber Reserve promotes networking opportunities, mentorship, awards, and community support and recognition as benefits of membership.24 In a field with a workforce shortage and high burn-out rates, the opportunity to network, gain professional skills, learn from mentors and peers, and help the local community is an important draw of C3s. Taken together, these intangible benefits will help states to retain an adequate cybersecurity workforce and may even attract new and emerging talent to the cybersecurity field.
Challenges
C3s also present several challenges for these stakeholders, which must be addressed in the legal framework governing the entity. This section explains some of the key legal issues that arise when states look to use the services of civilian cyber volunteers. Appendix 2 provides a list of key legal provisions that should be included in C3 laws to address those issues, while Appendix 3 incorporates the key legal provisions in a Model C3 Law that states can use to develop their own C3 laws.
First, securing the necessary funding to form and maintain a C3 can be a challenge for states. Based on existing C3s, the amount required for minimum efficient operating levels is around $1 million annually. States like Wisconsin and Oklahoma have utilized federal DHS grants to form C3s, while others—like Maryland, Ohio, and Texas—have relied on state budgets. As part of the proposal for a state C3, legislatures may need to propose a funding source. Federal grants, like the State and Local Cybersecurity Grant program administered by CISA may help, but without further congressional action, that funding will soon cease.25 To scale this solution and support it over the long term, states must identify ongoing funding sources.
Second, states must develop and implement a legal framework to establish clear roles and responsibilities, allocate liability, ensure confidentiality, and establish rules for collaboration with other entities (including other states’ C3s), among other concerns. A statement issued by Virginia’s Governor vetoing a bill that would have required an assessment of the feasibility of a state C3, highlighted “continued financial obligations, background checks, liability protections, and ongoing recruitment” as well as potential conflicts with the National Guard’s duties as issues to be addressed before forming a C3.26 Other states considering developing C3s will have similar concerns, but because of differing legal, political, and cultural environments, what works in one state may not be directly transferable to another. A related issue arises from the use of cyber volunteers with respect to collaboration across entities within a state, between states, or with the federal government. Those engagements are typically carried out under MOUs that specify the scope of responsibilities. A similar structure can be utilized for C3s, but this issue should also be addressed in the relevant C3 law to make clear that MOUs should be used for this purpose.
Third, states may find it difficult to identify, recruit, and vet volunteers and employers, especially SMBs. This is one of the challenges highlighted by Virginia’s Governor after vetoing a bill to assess the feasibility of a C3 in Virginia. Given the shortage of cybersecurity professionals, it may be difficult, especially in certain states or regions with lower populations, to recruit sufficient personnel who meet the states’ required qualifications. Requirements that are too stringent could also prevent talented cybersecurity professionals from being able to provide support. In addition, some volunteers may be concerned about the risk that hackers target them or their employers because of their volunteer work.27 It is important to draft C3 requirements in a way that accounts for the varying backgrounds and qualifications of potential volunteers. In addition, states have found several creative solutions to vet potential volunteers. Wisconsin’s Cyber Response Team prefers applicants who are members of InfraGard—a partnership between the FBI and the private sector designed to protect critical infrastructure sectors—because those applicants will have completed a federal background check.28
A fourth challenge presented by C3s is that of raising awareness about the existence of and services offered by the C3 so that beneficiaries can meaningfully engage them for support. When C3s are formed, potential beneficiaries will not know the C3’s services are available to them, and governments may have difficulty identifying beneficiaries or establishing a realistic scope of services.29 It will be incumbent on C3s to market their offerings to potential beneficiaries and to provide easy means for those in need of these services to engage them. Existing C3s have identified this as an early challenge, but one that can be overcome through outreach and preventive services, such as education, training, and vulnerability and risk assessments. For example, the Ohio Cyber Reserve engages in proactive outreach to beneficiaries and education and training for K–12 schools. The Wisconsin Cyber Response Team proactively engages with beneficiaries to educate them about the Cyber Response Team’s services.

Courtesy of Wisconsin Emergency Management, used with permission.
A fifth challenge involves understanding the interaction between cyber insurance carriers and C3s during cybersecurity incident response. A reliable estimate of the number of local governments across the U.S. with cyber insurance coverage is not available, but as of 2023, only 53 percent of small businesses have cyber insurance coverage.30 For SLTTs and SMBs that do not have cyber insurance coverage, C3s can help to make coverage more accessible by providing education, training, risk and vulnerability assessments, and remediation support, which insurers will review as part of the application process. For SLTTs and SMBs that do have cyber insurance, their insurers will offer a panel of service providers for pre-incident risk assessments and incident response, including law firms, digital forensics and incident response firms, public relations agencies, call centers, credit monitoring services, data recovery and restoration companies, and ransomware negotiators. However, even for those organizations that have insurance, C3s can provide education, training, and risk and vulnerability assessments that insurance does not cover. Further, those organizations may still need C3 support in the event of a cybersecurity incident where the costs are below the organizations’ retention limits or are likely to exceed their aggregate policy coverage, or in cases where coverage is excluded. C3s should proactively engage with and educate cyber insurance carriers and beneficiaries about the C3s’ services to align on the circumstances under which C3s can be most effectively utilized.
Lastly, the nature, length, and timing of deployments could present challenges. Volunteers deployed for extended engagements may have other personal or professional conflicts. If volunteers are not regularly utilized or provided opportunities for engagement through the C3, volunteer participation is likely to wane and future recruitment might become more difficult. Because C3s are volunteer-driven, those concerns cannot be overlooked, and C3s will need to develop enough capacity to account for times when volunteers are not available. C3s will also need to regularly meet and train to sustain engagement and readiness.
Citations
- See Cohen and Singer, The Need for C3, source.
- Jason Healey, “Ukrainian Cyber War Confirms the Lesson: Cyber Power Requires Soft Power,” Council on Foreign Relations (blog), April 4, 2023, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 3, source.
- “Wyden Releases Hold After FEMA Announces NET Guard Pilot Program,” U.S. Senate, June 19, 2008, source.
- “Open/Closed: Hearing Title to Receive Testimony on the Posture of the Department of the Army in Review of the Defense Authorization Request for Fiscal Year 2025 and the Future Years Defense Program,” U.S. Senate Committee on Armed Services, Apr. 18, 2024, 02:17:00, video, source.
- “High Risk Communities,” CISA, accessed Aug. 31, 2024, source.
- Skylar Rispens, “National Guard Ready to Assist States with Cyber Response, Say Officials,” StateScoop, Mar. 20, 2024, source.
- “About MiC3,” Department of Technology, Management & Budget, accessed August 25, 2024, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 32, source.
- Cynthia Brumfield, “Civilian Cyber Reserves Gaining Steam at the Federal and State Levels,” CSO Online, January 24, 2024, source.
- Dolen, “Re-Envisioning State Cyber Response Capabilities,” source.
- Nate Castele, “‘Cyber Incident’ Closes Cleveland City Hall for Public Business Thursday and Friday; City in Contact with FBI and Ohio Cyber Reserve,” Signal Cleveland, June 12, 2024, source.
- Maggie Smith et al., “Taking the Elf Off the Shelf: Why the U.S. Should Consider a Civilian Cyber Defense,” Lawfare Institute, July 6, 2022, source.
- Estonian Defence League’s Cyber Unit, Estonian Defense League [KAITSELIIT], source.
- Eneken Tikk, “Civil Defence and Cyber Security: A Contemporary European Perspective,” in National Cyber Emergencies: The Return to Civil Defense, ed. Greg Austin (New York: Routledge, 2020), 86.
- James Rundle, “New York State Debuts First Cybersecurity Strategy,” Wall Street Journal, August 9, 2023, source.
- Rispens, “National Guard Ready to Assist States,” source.
- Office of Advocacy, “Frequently Asked Questions about Small Business, 2023,” U.S. Small Business Administration, March 7, 2023, source.
- U.S. Senate, “Wyden Releases Hold After FEMA Announces NET Guard Pilot Program,” source.
- Monica Ruiz, “Is Estonia’s Approach to Cyber Defense Feasible in the United States?,” War on the Rocks (blog), January 9, 2018, source.
- Shaun Waterman, “Ukraine Scrambles to Draft Cyber Law, Legalizing Its Volunteer Hacker Army,” Newsweek, March 13, 2023, source.
- “Join OhCR,” Ohio Cyber Reserve, accessed August 17, 2024, source.
- Jake Braun, “DEF CON 32 – Jake Braun – DEF CON Franklin Project,” August 10, 2024, at 12:29, video, source.
- Ohio Cyber Reserve, “Join OhCR,” source.
- Colin Wood, “States Urge Congress Not to Claw Back Cybersecurity Grant Funding,” State Scoop, June 4, 2024, source.
- 2024 Session Governor’s Veto, HB651, Virginia’s Legislative Information System, accessed August 25, 2024, source.
- Mehul Srivastava, “Cyber Security Researchers Become Target of Criminal Hackers,” Financial Times, August 17, 2023, source.
- See Wisconsin Cyber Response Team, Wisconsin Emergency Management, accessed August 17, 2024, source.
- Schreiber et al., Creating a Cyber Volunteer Force, 10–11, source.
- Hiscox Cyber Readiness Report 2023 US Small Business Focus, Hiscox, 2023, 7, source.
Existing Legal Frameworks Governing Civilian Cyber Corps
For C3s in the United States and abroad, the existing legal frameworks generally include: (1) a statute; (2) contracts or MOUs between the state and beneficiaries and between the state and volunteers; and (3) rules and guidance for programs. The contractual component has been written about elsewhere,1 so this report focuses on the statutes governing C3s. Of the five existing state C3s, all but Wisconsin have governing statutes—laws enacted for the specific purpose of governing the activities of the C3.
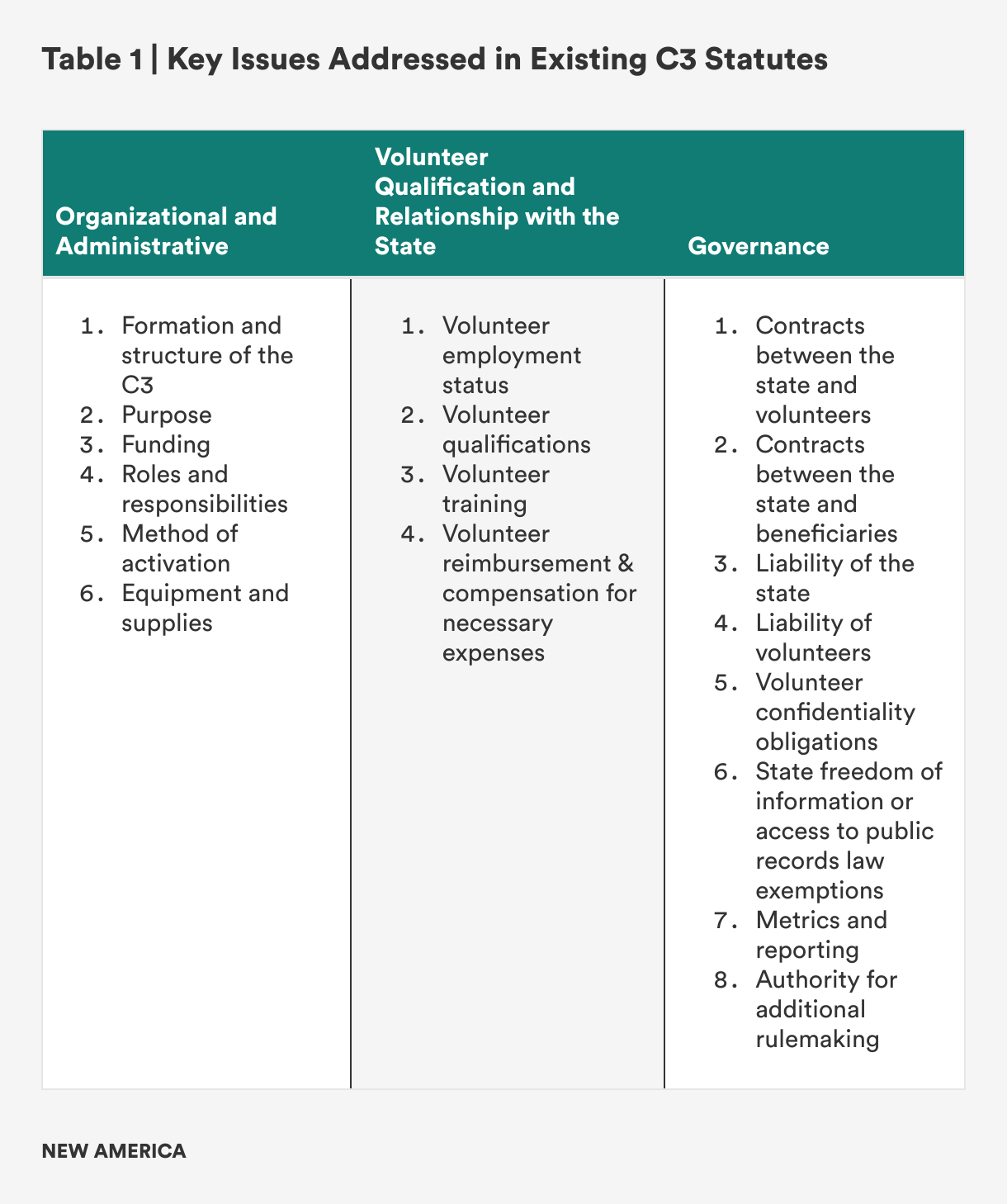
Enacting legislation specific to C3s helps lay the foundation for their success by establishing clear rules of the road and legal protections for all stakeholders involved. Without a specific statute, key legal issues like roles and responsibilities, liability, and confidentiality will be governed by existing state and federal laws, which could limit C3s’ activities or result in unintended outcomes. As a result, states like Oklahoma, Indiana, and Virginia, who are actively considering C3s, continue to carefully consider the gaps in existing laws that may not adequately support the effective use of volunteer cybersecurity professionals. Key issues addressed in existing C3 statutes fall into three broad issue categories, with sub-issues under each, as described in Table 1 below.
Citations
- Schreiber et al., Creating a Cyber Volunteer Force, 10–11, source.
Key Issues Presented by Existing C3 Laws
There is no one-size-fits-all model for C3 statutes because of the different legal, political, and cultural environments across states. Nevertheless, several key issues should be addressed in each state C3 statute regardless of the differing factors between states (with modifications made to suit a particular state). This section sets out key challenges presented by some of the key legal provisions in existing C3 statutes or that are not addressed in existing statutes.1 Without adequately addressing the key legal issues, C3s will not be able to achieve their potential or might see only limited utilization that will in turn result in difficulties in recruitment and retention of volunteers.
A foundational step will be establishing the C3’s authority to operate, which must be taken while carefully considering a particular state’s legal, political, and cultural environments. On the one hand, a C3 can be established under a state civilian department responsible for technology—as in the cases of Michigan and Texas—or homeland security or emergency management, as is the case in Wisconsin. This structure can help to ensure cyber volunteers are closely connected with other state IT or emergency management personnel and processes. It also keeps cybersecurity in the civilian domain and could mean the C3’s leadership are more likely to have IT or cybersecurity experience; a dilemma currently facing U.S. armed services is that cybersecurity experience is generally not required to lead cybersecurity personnel.2 On the other hand, 18 states and Puerto Rico have active state defense forces under 32 U.S.C. § 109, and a C3 can operate under the authority of the state defense force, as in the cases of Maryland and Ohio.3 For states that have an active defense force, a C3 under that structure can take advantage of existing funding, regulations, and operational processes intended for volunteers. In either case, providing authority to operate is the cornerstone to establish an effective C3. This issue is addressed in Section 3 of Appendix 3.
Next, clearly defining the purpose of the C3 and the criteria for its deployment are key issues because they will determine potential beneficiaries and the circumstances under which the C3 is utilized. For instance, the Ohio Cyber Reserve’s mission expressly includes support for small- and medium-sized businesses (SMBs), while the Texas Volunteer Incident Response Team’s mission is expressly limited to state, local, tribal, and territorial government entities (SLTTs). Because SMBs might operate critical infrastructure, like water utilities or healthcare facilities, a C3 with no authority to provide services to SMBs could not assist a privately owned water utility impacted by a cybersecurity incident. However, determining which SMBs are eligible for assistance and under what circumstances, while also avoiding creating a moral hazard where SMBs underinvest in cybersecurity, can be difficult. The same moral hazard problem can arise with respect to SLTT entities. The purpose should also help to outline the scope of activities of the C3 from other stakeholders involved in cybersecurity incident response, such as the National Guard, FBI, CISA, or state police. These issues can be further clarified in MOUs but are addressed in Sections 3 and 4 of Appendix 3.
C3 laws must also define the criteria for deploying volunteers. If the process to deploy the C3 is too restrictive, the C3 will not be effectively utilized. If the process to deploy the C3 is too permissive, it could lead beneficiaries to underinvest in cybersecurity because of an overreliance on the C3 (the moral hazard problem), or it could strain the resources of the C3. When Michigan’s C3 was initially formed, members could only be deployed during a state of emergency and could only provide services to SLTT entities. The state recognized those criteria were too restrictive and limited use of the C3 as a resource, so when Michigan later codified the C3, the legislature loosened the deployment criteria so that the State Chief Information Security Officers could deploy volunteers to assist SLTT and SMB entities.4 In contrast, under the Texas C3 law, the Texas Volunteer Incident Response Team can be activated only at the request of a participating entity if: (1) the Governor declares a state of disaster caused by a cybersecurity event; or (2) a cybersecurity event impacts multiple participating entities.5 As a consequence, the Texas Volunteer Incident Response Team is far less likely to be deployed for incident response—even during cybersecurity events where the Volunteer Incident Response Team’s assistance may have proved useful—than other state C3s with more permissive deployment criteria. Section 10 of Appendix 3 addresses this issue, drawing on lessons learned from cases like those of Michigan and Texas.
The interaction between C3 laws and state procurement laws is also an important issue to be addressed. The funding and procurement challenges faced by the U.S. Cyber Command—which largely relies on the Army, Airforce, Navy, and Marines to meet those needs—demonstrate the importance of agile procurement (and sufficient funding) for cyber forces.6 C3s that are part of an existing state defense force, like the Maryland Cyber Unit and the Ohio Cyber Reserve, can take advantage of existing equipment, facilities, and procurement processes designed for the military, providing adequate resourcing to equip and train the C3.7 While those processes may or may not be optimal for the C3, they provide useful procurement infrastructure that is already used to support cyber defense. Additionally, defense forces likely already have access to at least some cybersecurity tools, like network scanners and application testing software. C3s established under information technology or emergency management organizations are less likely to have adequate processes to procure equipment and supplies. The responsibilities of IT and emergency management entities may not encompass statewide cybersecurity incident response and their funding is more likely to vary as a result of political changes. As a consequence, if C3 laws do not appropriately address the procurement of equipment and supplies, procurement of appropriate equipment and supplies may require navigating complex, bureaucratic processes that prevent or delay C3s from obtaining the tools they require. C3 laws must provide flexibility for C3s to obtain appropriate software, equipment, and facilities to provide services to beneficiaries (as shown in Section 13 of Appendix 3), which could even include exceptions to existing state procurement laws.
Liability is another key legal issue that arises from the use of a C3. Some existing state C3 laws address the liability of the state, all address the liability of volunteers, but those provisions do not need to reinvent the wheel. The Volunteer Protection Act of 1997, a federal law designed to provide liability protection to volunteers—including those volunteering on behalf of a state—provides, in part, that no volunteer performing services for a nonprofit or a government entity will be liable for harm caused by their act or omission if: (1) the volunteer was acting within the scope of his or her duties; (2) the volunteer was authorized by the entity to perform the services; and (3) the harm was not caused by willful or criminal misconduct, gross negligence, reckless misconduct, or a conscious, flagrant indifference to the rights or safety of the individual harmed.8 That means that, even in Wisconsin, which does not have a C3 law, volunteers are afforded some liability protections while performing services for the state’s Cyber Response Team. Existing state C3 laws do not address the Volunteer Protection Act but should incorporate and build on the existing federal law to further address concerns with respect to the potential liability of volunteers. Liability is addressed in Section 9 of Appendix 3.
Further, C3 laws should address the confidentiality of volunteers’ personal information. Given the nature of their work, it is possible that volunteers or their employers could themselves become targets of malicious actors because of their service. To mitigate that risk, C3 laws should expressly provide for the confidentiality of volunteers’ personal information and provide an exemption of volunteers’ personal information from disclosure under state freedom of information or access to public records laws. That protection should be provided to all cyber volunteers, who can then determine whether they want to make their volunteer work known publicly. Currently, only the Texas C3 law expressly provides for the confidentiality of volunteers’ personal information, while Wisconsin provides an exemption for personal information of applicants to the program.9 Doing so can assist states with recruiting and retaining volunteers who may be concerned about disclosure of their participation and personal identifying information. Section 11 of Appendix 3 provides model provisions to protect the confidentiality of volunteers’ personal information.
Lastly, a streamlined approach to data collection and metrics reporting would be useful to demonstrate the value of C3s and identify opportunities for improvement. Existing C3 laws, however, fail to adequately address requirements for data collection and reporting in their frameworks. As corporate cybersecurity departments typically report metrics to management to demonstrate the maturity of the cybersecurity program and its value to the organization, C3s should also report metrics for similar reasons. A data collection and metrics reporting provision could direct the department overseeing the C3 to collect data demonstrating the program’s utilization, effectiveness, and areas for improvement. Existing state C3s collect data on their operations, but often, the data collected vary by state; they are not standardized or centralized in a way that would facilitate comparison and information sharing across state C3s. Standardizing C3 data and sharing it with relevant stakeholders will allow for better decision making when determining which activities are best suited to the scope of duties of state C3s and which might be better suited to other organizations in the cyber volunteer ecosystem. Performance metrics will also help provide benchmarking across state C3s and to make the case for additional funding by clearly demonstrating the C3’s value. This issue does not need to be completely resolved by statute but should be addressed as shown in Section 15 of Appendix 3.
Citations
- Appendix 2 sets out a complete list of key legal provisions to be included in C3 statutes to address the challenges identified in this section.
- See Dr. Erica Lonergan & RADM (Ret.) Mark Montgomery, “United States Cyber Force: A Defensive Imperative,” Foundation for Defense of Democracies, March 2024, source.
- In addition to Puerto Rico, the 18 states that have active state defense forces include Alaska, California, Georgia, Indiana, Louisiana, Maryland, Michigan, Mississippi, New Mexico, New York, Ohio, Oregon, South Carolina, Tennessee, Texas, Vermont, Virginia, and Washington (Florida has a civilian defense force that is not authorized under 32 U.S.C. § 109). See “Join the State Defense Force,” StateDefenseForce.com, accessed August 14, 2024, source.
- Jenni Bergal, “Michigan Governor Signs Volunteer Cyber Corps Bill,” Government Technology, October 31, 2017, source.
- Texas Government Code Annotated § 2054.52005(a), source.
- See Lonergan and Montgomery, “United States Cyber Force,” source.
- See Oh. Rev. Code § 5922.03, source.
- See 42 U.S.C. § 14503, source.
- Texas Government Code Annotated § 2054.52010, source. Other laws may apply in Texas or other states to further limit the potential disclosure of volunteers’ personal information.
Conclusion
C3s could prove critical in addressing new and evolving cyber threats. As more states seek to bolster their cybersecurity efforts despite insecure software and technology and an ongoing cyber workforce shortage, the C3 model offers an avenue to work toward cyber resilience. In addition to outlining the landscape of existing C3s and related legal frameworks, this report concludes with a roadmap with key legal provisions (see Appendix 2) and a template for creating a C3 statute suited to an individual state’s context, challenges, and opportunities (see Appendix 3). As cyber attacks continue to rise and threaten important infrastructure like state, local, tribal, and territorial (SLTT) governments and small and medium-sized businesses, C3s are a critical tool to help ensure our nation’s security.
Appendix 1. Civilian Cyber Corps Overview
Appendix 2. Key Legal Provisions for State Civilian Cyber Corps (“C3”) Laws
The legal provisions below are intended for consideration by states when drafting legislation to establish and govern a volunteer state-led civilian cyber corps (C3s). Each provision listed below includes additional information to explain the importance of the provision and, in some cases, additional considerations that may be relevant. These provisions are intended to be referred to as a checklist in drafting civilian cyber corps legislation, while Appendix 3 incorporates these key legal provisions into a Model C3 Law.1
- Establish the C3 and the authority under which it will operate. For the 18 states and Puerto Rico that have an active state defense force under 32 U.S.C. § 109, the civilian cyber corps can operate under the authority of the state defense force. In other states, the C3s can operate under the relevant department responsible for IT, homeland security, or emergency management. In all cases, the individuals responsible for overseeing the organization should be required to have cybersecurity experience.
- Define the purpose and mission of the C3. The purpose of the C3 should be flexible enough that the C3 can provide services to SMBs, even if SMBs are not routine beneficiaries. In the event of a significant regional or national cybersecurity event, support may be required from volunteers to help mitigate impacts to SMBs that manage critical infrastructure or operate essential services.
- Set up civilian cyber corps contracts. The state must enter into written agreements with volunteers and beneficiaries, which can be separate agreements or a tripartite agreement between the parties.
- Between volunteers and the state. The C3 statute should require the relevant department to enter into an agreement with each volunteer that addresses certain requirements, such as the scope of volunteer activities, consent to a background check, confidentiality, conflicts of interest, the employment relationship between the parties, reimbursement of expenses, and the conditions of continued membership (e.g., compliance with applicable law and policies).
- Between beneficiaries and the state. The statute should require the relevant department to enter into agreements with beneficiaries that address the scope of the civilian cyber corps’ services, consent and authorization for volunteers to provide services, confidentiality, a release and waiver of liability, indemnification of the state and of volunteers for damages incurred while providing services within the defined scope of work, and protection of the beneficiaries’ intellectual property.
- Determine volunteer qualifications and recruitment. The needs of a C3 different volunteer qualifications may change over time, so the C3 statute should authorize the responsible department to establish qualifications for civilian cyber corps members. The statute may set out minimum requirements, such as the requirement for U.S. citizenship or lawful permanent residency, that volunteers complete a background check, and that volunteers agree to abide by contract terms specified by the state. Given the number of hackers-turned-cybersecurity professionals, a criminal history might not be immediately disqualifying, but instead might require additional vetting or it might limit the types of activities in which a volunteer can participate. Further, the C3 statute should provide authority for the creation of rules to address the disclosure of potential conflicts of interest and situations where such a conflict might disqualify a volunteer from certain activities.
- Develop volunteer training. The responsible department should be required to develop appropriate training for volunteers and to ensure each volunteer participates in training at least annually.
- Procure civilian cyber corps equipment and facilities. Providing explicit authority for the civilian cyber corps to procure equipment and facilities, or certain exemptions from existing procurement laws, will help to avoid inadequate procurement processes.
- Plan for deployment of volunteers. The circumstances under which the volunteers can be deployed should be clearly defined but flexible. If the requirements for deployment are too restrictive, the C3 will not be underutilized, while if requirements are too permissive, the C3 could be over-utilized, creating an inability to provide adequate services to all beneficiaries or underinvestment in their own cybersecurity programs by beneficiaries. Regardless of where the ultimate authority rests, the statute should provide for delegation of that authority to a lower managerial level to determine when to activate the civilian cyber corps subject to other program criteria specified.
- Define the relationship of volunteers with the state and beneficiaries. The statute should expressly state the relationship of volunteers with the state and beneficiaries, and it should disclaim any employment, agency, or independent contractor relationship between the volunteer and the state and beneficiaries as a result of participation in the program.
- Establish liability protections.
- For volunteers. The statute should expressly state that volunteers are authorized by the state to conduct the activities permitted under the statute and are subject to the protections for volunteers under the Volunteer Protection Act of 1997 while acting within the scope of their services and while in compliance with laws, regulations, contracts, and policies governing the C3.
- For the state. The statute should disclaim liability of the state to beneficiaries for services rendered by a volunteer. It should also disclaim liability of the state to volunteers for injuries or damage to property incurred by a volunteer while performing services.
- Ensure confidentiality. Confidential information, including trade secrets, business plans, and cybersecurity plans and practices disclosed by beneficiaries should be exempt from disclosure under state freedom of information, access to public records, or equivalent laws. Additionally, volunteers’ personal information should be exempt from state freedom of information or access to public records laws because of the possibility that volunteers or their employers could become subject to cyber attacks because of the nature of the volunteer work.
- Determine volunteer compensation. Volunteers may incur necessary expenses, such as mileage or parking fees, in order to provide services to beneficiaries, for example, if volunteers need access to the servers of a beneficiary at a rural facility. The C3 statute should authorize the department to reimburse volunteers for reasonable, actual expenses incurred.
- Address volunteer resignation or refusal to serve. Volunteers should be able to refuse an assignment, and the C3 statute should expressly permit them to do so. However, C3 statutes can include a minimum amount of training or number of assignments that volunteers must complete each year in order to maintain membership. Volunteers should also be able to resign from the program at any time as their personal and professional circumstances change.
- Facilitate collaboration with other entities. C3s will need to collaborate with other state and federal entities responsible for cybersecurity incident response, including police, the National Guard, FBI, and CISA, and others. While various factors might dictate which entity begins or leads a particular engagement, a statute might require that a liaison be designated to facilitate coordination with those other entities.
- [Optional] Create an Advisory Council. It will be beneficial for states to establish an advisory council to support the responsible department to develop operational rules and guidance for the C3, especially where the responsible department has expertise in another domain, like emergency management, IT, or military defense, and does not have expertise in cybersecurity. Although it will be ideal to have someone with cybersecurity expertise to lead the C3, that may not be possible, so an advisory council that includes cybersecurity experts can provide appropriate guidance to the relevant department. An advisory council may not be necessary in all states, because some states already have a similar structure that can also provide guidance to the C3 and other states may have sufficient in-house expertise that an advisory council is not required.
- Institute authority for additional rules and guidance. Tactical matters, such as specific qualifications of volunteers and equipment to be used, should be left to the discretion of the responsible department. It is important to leave flexibility for the responsible department to enact rules and guidance to address those matters. C3 statutes should also set a requirement to collect and share operational metrics. While this issue of evaluation is not currently addressed in many C3 statutes, it should be addressed and should allow for the responsible department to develop detailed requirements for data collection and reporting of metrics under the statute.
Citations
- Together with the key contractual legal provisions and the model contract published by the law firm McDermott, Will & Emery, LLP, states have the key parts of a C3 legal framework that can be utilized to make the work of forming a C3 more efficient. See Schreiber et al., Creating a Cyber Volunteer Force, 54–64, source.
Appendix 3. Model Civilian Cyber Corps (C3) Law
This Model Civilian Cyber Corps (C3) Law incorporates the key legal provisions from Appendix 2 into statutory language that states can use as a template to draft their own C3 law. The statutory language should be adapted as needed to conform to the legal statutes of a particular state. Brackets ([]) are used in this Model C3 Law to indicate: (1) where information will need to be completed as applicable to each state; and (2) where language might differ depending on whether a C3 is part of a state military defense force or another state department or agency.
Table of Contents
Section 1. Title
Section 2. Definitions
Section 3. Creation of Civilian Cyber Corps and Purpose
Section 4. Relationship with other Entities
Section 5. Recruiting and Qualifications of Volunteers; Relationship with the State
Section 6. Contract with Volunteers
Section 7. Contract with Beneficiaries
Section 8. Volunteer Training
Section 9. Civil Liability
Section 10. Volunteer Deployment
Section 11. Confidential Information
Section 12. Volunteer Expense Reimbursement
Section 13. Volunteer Equipment and Facilities
Section 14. Civilian Cyber Corps Advisory Council
Section 15. Additional Rulemaking Authority
Section 1. Title
This Act shall be known and may be cited as the [State] Civilian Cyber Corps (C3) Law.
Section 2. Definitions
As used in this Act, the following terms shall have these meanings:
- “Civilian Cyber Corps” means the volunteer-based cybersecurity organization established under Section 3.
- “Beneficiary” means any of the following that meet the eligibility criteria established by the [department/Governor] to receive and request assistance from the Civilian Cyber Corps: (1) the state or any local government, or any of their departments, agencies, or political subdivisions, including an institution of higher education; and (2) any business identified by the [department/Governor] as operating critical infrastructure or key resources within the State.
- “Volunteer” means an individual who has entered into a volunteer agreement with the [department/State] to serve as a deployable volunteer in the Civilian Cyber Corps.
Section 3. Creation of Civilian Cyber Corps and Purpose
The [department/Governor] shall establish and maintain a Civilian Cyber Corps capable of being deployed to assist Beneficiaries to improve their resilience to, and ability to recover from, adverse cyber events. The Civilian Cyber Corps shall be known as the [State] Civilian Cyber Corps.
Section 4. Relationship with other Entities
- The Civilian Cyber Corps shall be part of the [department/[State] organized militia under the Adjutant General's Department]. The [department/Adjutant General] shall coordinate the provision of cybersecurity services to be performed by Civilian Cyber Corps Volunteers with other state and federal agencies and departments that may also provide cybersecurity services to Beneficiaries, including by, but not limited to, establishing roles and responsibilities responding to adverse cybersecurity events.
- Upon request by the governor of another state, the Governor may authorize the [department/Adjutant General], pursuant to a written agreement [or memorandum of understanding] and subject to the laws of this State and the United States, to deploy the Civilian Cyber Corps to assist the other state’s National Guard or civilian cyber corps with matters within the scope of services of the Civilian Cyber Corps. The [department / Adjutant General] shall develop rules for assistance to another state under this Section in consultation with the Advisory Council established under Section 14.
Section 5. Recruiting and Qualifications of Volunteers; Relationship with the State
- The [department/Adjutant General] shall be responsible for recruiting qualified volunteers to participate in the Civilian Cyber Corps. The [department/Adjutant General] shall prescribe eligibility criteria for participation as a volunteer member of the Civilian Cyber Corps, including, as appropriate, requirements to perform specific duties as a volunteer.
- Applicants for membership in the Civilian Cyber Corps shall be subject to an appropriate background check, in accordance with rules adopted by the [department/Adjutant General], before admittance into the Civilian Cyber Corps.
- A volunteer is not an agent, employee, or independent contractor of this State for any purpose and has no authority to obligate this State to a third party. [When called to state active duty by the Governor, Civilian Cyber Corps members shall function as civilian members of the [State] organized militia and shall be paid at the rates established by the Adjutant General.]
Section 6. Contract with Volunteers
The [department/Adjutant General] shall enter into a contract with each volunteer who meets the qualifications established by the [department/Adjutant General] and who the [department/Adjutant General] approves to join the Civilian Cyber Corps. At a minimum, the contract must address the following: consent to the background screening process, confidentiality of information obtained by the volunteer in the course of their service, conflicts of interest that may arise during membership, liability of the state relating to volunteers’ services, and an acknowledgement and an attestation that the volunteer will comply with such rules, policies, and guidelines as the [department/Adjutant General] may issue in order to maintain membership.
Section 7. Contract with Beneficiaries
- The [department/Adjutant General] shall enter into a contract with each Beneficiary that is eligible to receive assistance from the Civilian Cyber Corps and that requests such assistance. At a minimum, the contract must address the following: confidentiality of information obtained from the Beneficiary, liability of the state and of volunteers relating volunteers’ services, indemnification for claims relating to assistance provided, obligations for data breach and notifications, if applicable, consent to permit volunteers to access the Beneficiary’s information systems and/or facilities as necessary for the purpose of providing the requested assistance, and protections for the Beneficiary’s intellectual property.
- Nothing in this Act prohibits the Beneficiary from entering into a contract with a Volunteer or modifies any pre-existing agreements between a Beneficiary and a Volunteer.
Section 8. Volunteer Training
The [department/Adjutant General] shall provide appropriate training to Civilian Cyber Corps members and shall require each member to participate in at least two (2) training or education events annually.
Section 9. Civil Liability
- A member of the Civilian Cyber Corps shall not be liable for harm caused by an act or omission of the volunteer as set forth in the Volunteer Protection Act 1997, 42 U.S.C. §§ 14501-14505.
- Except for willful or criminal misconduct, gross negligence, reckless misconduct, or a conscious or flagrant indifference to the rights or safety of the individual harmed, no volunteer acting within the scope of the volunteer’s services shall be liable for economic loss (as defined under 42 U.S.C. § 14505) incurred by a Beneficiary.
- Nothing in this Act shall restrict or limit the obligations or duties of a Beneficiary to make [data breach or other notifications], as applicable, under state or federal law, or as may otherwise be required of the Beneficiary.
Section 10. Volunteer Deployment
- The Governor, or the Governor’s designee, [or executive branch authority] may deploy volunteers in response to a request for assistance or through a standing order permitting the [department/Adjutant General] to establish criteria to determine[, in consultation with the Advisory Council,] when to deploy the Civilian Cyber Corps. The Governor [or executive branch authority] may issue an order to deploy the Civilian Cyber Corps in cases where the [designee/department/Adjutant General] has not done so pursuant to a standing order or other authority.
- A volunteer may only accept a deployment under this Act in writing. A volunteer may decline to accept a deployment for any reason.
Section 11. Confidential Information
- Information written, produced, collected, assembled, or maintained by the [department/Adjutant General], in consultation with the Advisory Council, that relates to the Civilian Cyber Corps’ services provided to Beneficiaries and that is designated and marked by the [department/Adjutant General] as [Highly Confidential] is confidential and is not subject to disclosure under [state freedom of information or access to public records law, or equivalent(s)].
- Information written, produced, collected, assembled, or maintained for, or disclosed to, the [department/Adjutant General] in connection with the deployment of the Civilian Cyber Corps is confidential and shall not be subject to disclosure under [state freedom of information or access to public records law, or equivalent(s)] solely because of the production, collection, assembly, or maintenance or disclosure by a Beneficiary to the [department/Adjutant General] for purposes of evaluating or receiving assistance from the Civilian Cyber Corps.
- Information written, produced, collected, assembled, or maintained by the [department/Adjutant General], a participating entity, the Advisory Council, or a volunteer in the implementation of this subchapter is confidential and not subject to disclosure under the [state freedom of information or access to public records law, or equivalent(s)] if the information:
- contains the postal address, city or county, email address, or phone number information for a volunteer; or
- identifies or provides a means of identifying a person who may, as a result of disclosure of the information, become a victim of a cybersecurity event.
Section 12. Volunteer Expense Reimbursement
[The department may provide compensation for actual and necessary expenses incurred for travel and subsistence by Civilian Cyber Corps members on a deployment at the discretion of the department.] / [The Adjutant General shall establish and may revise, in accordance with applicable [State law], the rates of pay for Civilian Cyber Corps members when called to state active duty.]
Section 13. Volunteer Equipment and Facilities
[Each year, the department shall propose a budget and request funds sufficient to operate the Civilian Cyber Corps. The department may also utilize such federal funding as may be available to support the Civilian Cyber Corps. The department shall allocate appropriate equipment and facilities for the operations of the Civilian Cyber Corps.] / [The Governor may requisition from the United States Department of Defense, for the use of the Civilian Cyber Corps, equipment that may be in the possession and can be furnished by the Department, and make available to the Civilian Cyber Corps the facilities of state armories and equipment and other state premises and property that may be available.]
Section 14. Civilian Cyber Corps Advisory Council
- The [department/Adjutant General] shall establish and lead a Civilian Cyber Corps Advisory Council that includes public and private sector leaders and cybersecurity practitioners to collaborate on matters concerning the maintenance and operation of the Civilian Cyber Corps.
- The Advisory Council shall be comprised of at least one (1) member of the [department / Adjutant General’s Office]; one (1) member from the public sector; and two (2) members of the private sector.
- The Advisory Council shall review and make non-binding recommendations to the [department/Adjutant General] regarding the policies and procedures used by the [department/Adjutant General] as set forth in this Act and with respect to any additional rules promulgated by the [department/Adjutant General] to implement this Act.]
Section 15. Additional Rulemaking Authority and Guidance
The [department/Adjutant General] shall consult with the Advisory Council to develop and issue additional rules and guidance as needed regarding the operations of the Civilian Cyber Corps, including, but not limited to, the following:
- The experience and qualifications necessary for applicants to become members of the Civilian Cyber Corps.
- Contract terms and conditions to be entered into with Volunteers and Beneficiaries.
- Appropriate training for members of the Civilian Cyber Corps.
- Equipment and facilities to be utilized by the Civilian Cyber Corps.
- Policies and procedures for the operation of the Civilian Cyber Corps.
- Requirements for a Beneficiary to receive assistance from the Civilian Cyber Corps.
- The process for a Beneficiary to request assistance from the Civilian Cyber Corps.
- Fees, if any, to be collected from Beneficiaries receiving incident response assistance, so long as the amount of fees collected does not exceed the [department's /Adjutant General’s] costs to provide the incident response assistance.
- The provision of assistance to the civilian cyber corps of another state.
- Any additional rules the [department / Adjutant General] considers necessary to implement this Act.
The rules, guidance and contract forms developed by the [department / Adjutant General] shall be made publicly available, except for those designated and marked by the [department / Adjutant General] as [Highly Confidential] pursuant to Section 11 of because their disclosure could diminish the cybersecurity posture of the State, the [department / Adjutant General’s Office], the Civilian Cyber Corps, or Beneficiaries.