Going Inside the Cyber Analyst’s Brain
How a new tool could make cyber analysts less burned out, and more effective.
In October 2016, I met Rebecca at the Grace Hopper Celebration, the world’s largest gathering of women in technology. She walked up to ask me some questions after my talk about using behavioral biometrics for authentication on mobile devices. At the time, Rebecca was a graduate student working on her master’s degree in computer science with a focus on cyber security. She was eager to start her career, and was getting ready to apply for summer internships. I became an informal mentor to her. Over the next few months, we exchanged LinkedIn messages and had a few phone calls. The following summer, Rebecca started an internship as Level 1 (L1) analyst at a Security Operations Center (SOC) for a technology company.
I immediately felt sympathetic: Working at a SOC is incredibly tedious – but the L1 job takes the cake for the most mundane role. The L1 team has “eyes-on-glass” 24-hours-a-day and seven-days-a-week. L1 analysts monitor a dashboard that displays security alerts streamed from the firewalls, intrusion detection systems, and other security appliances deployed within an organization’s network. When they see a high-priority alarm that may be linked to a security incident, it’s their job to act. Typically, they follow clear instructions to respond to the simple straight-forward alerts. For the more complex alerts, they ask for assistance from the L2 or L3 teams.
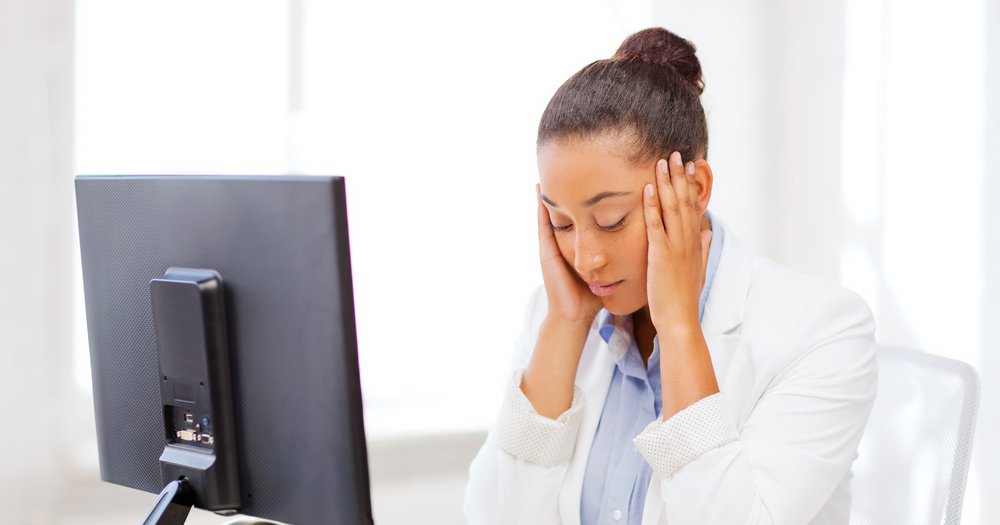
Unsurprisingly, Rebecca quickly got bored with the monotony of her role. By the end of her three-month internship, which felt more like a year, she told me that she had lost her passion for cyber security.
Even though the L2 and L3 teams have much more challenging and dynamic jobs – they’re the ones who get called to investigate a cyber attack when L1 analysts have no clear instructions on how to act – these teams have high turnover, too. That may be because they’re stressed out, due to a shortage of personnel, and an overload of alarms to respond to immediately. This high attrition rate is a problem for companies who want to protect themselves from attacks. As soon as an analyst gets trained and becomes productive, which may take up to two years, he or she is ready to leave.
In other words, analysts are burning out before they’ve begun. They pay with their sanity, and the company pays in time and money. They are ready to leave within one to three years due to burnout and lack of a clear career path, according to research. This suggests that companies are not getting a return on their investment for hiring new analysts, and that the analysts are not growing to their full potential with their companies.
My team at Accenture is building technology to change this equation for employers and employees. Our goal: make the L1, L2 and L3 roles more rewarding and efficient by creating a cognitive incident response tool. You can think of it as a way to distill multiple stories about how different people respond to different alerts and breaches, using a shared vocabulary and defining an easy-to-follow workflow. As a resource that gathers best practices for how to respond to different incidents, it’s a tool for sharing knowledge from senior to more junior staffers. And by laying out a defined workflow, the tool allows companies to automate some of those mundane L1 tasks, like the security alerts Rebecca spent her days responding to. This, we hope, will improve the job satisfaction of L1 analysts by making their tasks less mechanic and freeing up time for responding to alerts that require more complex cognitive abilities. Our second goal: is to reduce the stress and cognitive load for L2s and L3s by making their training and on-boarding process faster and easier, and standardizing a more efficient incident response process.
Since a security analyst can get overloaded with alerts that may be irrelevant or at least lacking context for the incident being investigated, we hope this tool will offer a way for them to see more quickly what’s worth reacting to, and what’s just noise.
The exciting thing about our tool is that it can capture the knowledge of experienced security analysts and code them into a semantic graph, which adds a layer of semantics (meaning) on top of the interrelated security events and IT infrastructure. It's basically a way of telling security stories, developing narratives that connect the dots between events and providing contextual scaffolding. The analysts can even annotate the graph to document their thought process when analyzing a cyber incident.
Then, junior analysts can look at those annotations to understand the cognitive processes that the more senior analysts followed to resolve the incident. We hope this will help them learn security analytics skills faster.
What’s more, the annotations are machine-readable, so our tool can use them to reconstruct how an incident was resolved and how long it took the analyst to come to that resolution. Equipped with that information, it can recommend how to investigate similar incidents in the future based on the process that has yielded a resolution in the shortest time.
If only I could’ve shared this tool with Rebecca, the disillusioned cybersecurity graduate. While it may be too late to persuade her to rejoin the security workforce as an analyst, I do think it could help young people like her more quickly realize how exciting security roles can be, and the value that security analysts can bring to an organization, especially when they can learn from everyone who came before them.