Introduction
Cyberspace—the newest domain of conflict—is among the most prominent forums of conflict in the twenty-first century. Increasingly nation-states utilize cyber and information capability in pursuit of foreign policy and national security objectives. This report focuses on two nation-states that are leading the charge in this respect: China and Russia.
While Russia seeks to destabilize the global system for its own advantage, China’s goal is to maintain the current system and replace the United States as the global hegemon. To that end, China and Russia are pursuing robust cyber capabilities to advance their respective geopolitical, economic, and security interests. Moreover, Chinese and Russian state-run enterprises use tools ranging from cyber espionage to weaponizing information in an effort to undermine the efficacy of democracy and, in general, western interests around the world.
Figure 1: U.S. Military Approach to Information1
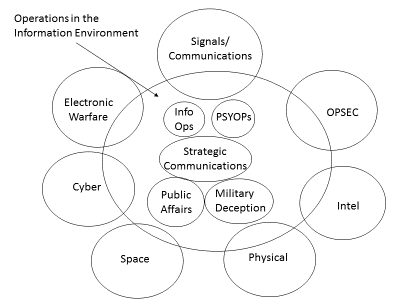
In this report, we offer an overview of Chinese and Russian cyber capabilities. We interpret these broadly to include both computer network, or cyber, capabilities and internet-enabled information and influence capabilities. Their view of the use of information to influence or “operations in the information environment” are different from the point of view of the United States, in particular the U.S. military. Although the U.S. Department of Defense seeks a more unified theory of how to influence other actors, the reality is that each community involved could be called a “cylinder of excellence.” Each group is very good at what they do, but the efforts are not integrated in the planning or execution stages of the operations. Figure 1 shows the relationship of the various actors who operate in the information environment.
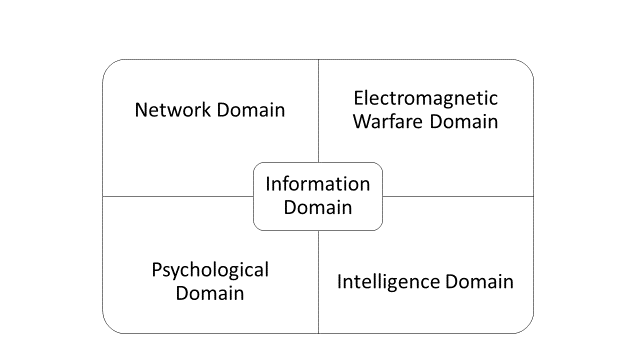
By contrast, Russia and China both have a more integrated view of the use of information. Russia’s approach is called “information confrontation”2 while the Chinese approach is one of “information dominance”3 Figure 2 illustrates the Russian integration of all elements of information while Figure 3 shows a Chinese military theorist’s conceptualization of the information domain.
Figure 2: The Russian Perspective on Information Competition4
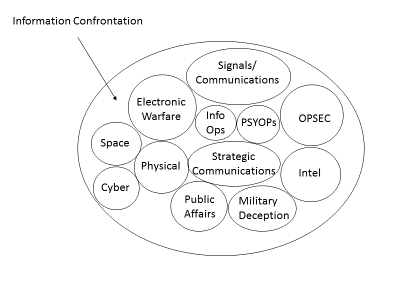
Figure 3: Chinese Military Theorist’s Conception of the Information Domain5
This report flows as follows: We start with an overview of Chinese and Russian cyber capabilities. Contained within each of these sections is an overview of key state and non-state actors, as well as overviews of known operations and capabilities. We then provide an analysis of how these capabilities are or could be used in the future in Latin America and the Caribbean. While the focus of the analysis is on applications in Latin America and the Caribbean, the information about Chinese and Russian capabilities is also applicable to operations that they may undertake in other regions.
Citations
- Chart is the original work of G. Alexander Crowther, Ph.D.
- “Information Confrontation over Ukraine,” Cybernautika, February 27, 2014.
- Dean Cheng, “Cyber Dragon: Inside China’s Information Warfare and Cyber Operations,”(Keynote address, Heritage Foundation, Washington, D.C., March 20,2017).
- Chart is the original work of G. Alexander Crowther, Ph.D.
- Figure 3. “China and Cybersecurity” (Figure 8.2 in Chapter 8), Oxford University Press (Oxford, UK, April 2015)
