Table of Contents
- Executive Summary
- Introduction
- Initial Fact Pattern
- Context: The Strategic Logic of Russian PMSC Operations in Syria
- Investigation Redux: New Videos Appear and with Them a New Mystery
- Syria’s Energy Protection Racket: Digging into Wagner Group Social Networks
- Conclusion: From War Crime to Internet Meme
- Appendix A: Research Methodology
- Appendix B: Breakdown of Reported Russian PMSC Areas of Operations and Projects as of June 2019
Appendix A: Research Methodology
Hybrid Forensics & Digital Data Mining Techniques
The first challenge in conducting research on the individuals affiliated with Russian PMSC’s is to identify a starting point. While open source researchers and journalists have anecdotally identified dozens of individuals suspected of fighting in Ukraine and Syria on behalf of the Russian state the Kremlin has consistently maintained that many of the Russian citizens identified in media and research reports are merely patriotic volunteers. Beyond a few well-known commanders of Russian operatives who have fought in Donbas and elsewhere little is known about how military orders are issued and executed on. The information published to date about one-off cases where Russian operatives reportedly affiliated with the Wagner Group, therefore, only delivers a partial, pixelated picture of how Russian PMSC’s operate.
It is next to impossible under these circumstances to evaluate how much influence the Russian state exerts over Russian PMSCs much less establish whether through direct or indirect third-party means the Kremlin maintains effective control over Russian PMSC operatives. The opacity is intentional. The more confusion over whether the “Wagner Group” consists of a few hundred ragtag volunteers who elected without any enticement from Russian state organs, or indeed, whether the so-called Wagner Group is an organized private enterprise comparable to Western PMSC’s such as Blackwater or its successor the Frontier Services Group the more difficult it is to attribute actions to actors and assign responsibility for misdeeds on the battlefield.
If we don’t know for sure who is fighting for whom and we only know where Russian PMSC operatives are suspected to have fought then the only real clues available are publicly available images, videos and text that places PMSC fighters somewhere in time and space on the battlefield. In this respect, the case of Hamdi Bouta’s videotaped killing at the al-Shaer gas plant in Syria in the late spring of 2017 presented our team with a unique opportunity to begin publicly asking and answering questions about the types of training, tools and equipment deployed by Russian PMSC’s in the field.
Our collaboration with the Dossier Center and C4ADS in examining EvroPolis account and contract information also allowed us to connect the dots between Russian field operatives and the administrative architecture that supports them. In this way we were able to pursue two mutually revealing lines of inquiry: how to Russian PMSC’s do what they do when they are in the field and how are they paid to do what they do? To answer these questions, we set out to triangulate open source data about the business activities EvroPolis and other firms linked to Yevgeny Prigozhin, the titular chief executive of an array of Russian firms that support PMSC operations, against unstructured information contained in thousands of publicly available social media accounts of individual Russian PMSC operatives.
Triangulating Open Source Data
The data collected and analyzed for this report was drawn from a variety of open sources, including leaked data documenting the activities of EvroPolis LLC and related Russian companies in Syria acquired by the Dossier Center and shared with our team. A key document in this dataset detailed revenues and expenditures for EvroPolis LLC in 2017 and May-August 2018, which indicated revenue flows during those periods for the Jihar, Jazal, Mahr, and Shaer oil and gas fields, facilities, and proximate storage sites. International reporting about military operations involving Russian PMSC contingents at each of those sites in the Hayan Block has been extensive. Wherever possible we also cross-checked information contained in the Dossier dataset through a review of publicly available corporate registries, company filings, and corporate reports publicly released by EvroPolis LLC’s contractual partners Hayan Petroleum Company, Syrian Petroleum Company, and Ebla Petroleum Company and the foreign corporations who have participated in production sharing agreements and jointly won tenders from the Syrian government for energy sector exploration, development, and production.
We compared imagery from the Homs area captured by traditional media coverage of battles near Hayan Block energy infrastructure and social media from the Hayan Petroleum Company, Syrian Petroleum Company, Ebla Petroleum Company, and the social media accounts of EvroPolis employees and consultants indicated in Dossier Center data. An additional cross review of well-known Russian personalities who frequently cover and travel with Russian PMSC’s in Syria, including the pseudonymous “Ivan Siderenko” and Oleg Blokhin, a Russian war correspondent, and numerous Vkontakte community groups dedicated to coverage of the war also helped to support findings that Russian PMSC operators engaged in battle at Hayan Block sites managed under a partnership agreement between EvroPolis, Hayan Petroleum, Ebla Petroleum and the Syrian Petroleum Company, all of which are Syrian state backed entities.1
Scaling Up Social Network Analysis to Explore Organizational Membership & Structure
As noted in this report, Russian news outlets were among to identify Stanislav Dychko as one of the men pictured in the video of Bouta’s killing. Since information divined from Dychko’s Vkontakte social media account was used to identify him we reasoned that it was possible that other Vkontakte users in Dychko’s friends circle might provide clues about the identity of others in the video. But, because Dychko’s Vkontakte account was taken down soon after the media reports in November 2019 that suggested that was a dead trail. However, prior research for the first report in this series, Decoding the Wagner Group, allowed us to tap into a much larger dataset of Vkontakte accounts associated with verified Russian PMSC fighters that we had collected. We reasoned that it was possible that some of Dychko’s battlefield compatriots might have links to individuals in this dataset. In other words, we had to work our way backwards to Dychko’s likely friends circle by looking first for the haystack rather than the needle.
For this first step, our team relied heavily upon the work of the Conflict Intelligence Team and an OSINT researcher who uses the Twitter handle “NecroMancer” (@666_mancer). @666_mancer collected a data set of alleged employees of Russian military companies (especially the so-called Wagner Group) killed-in-action in eastern Ukraine and Syria. Heavily represented on his list were employees killed at the Battle of Khasham in the Euphrates River Valley south of Deir Ezzor. While the dataset contained a significant trove of useful information, the data entered was far from uniform and the dataset required significant cleaning.
On October 8, 2018, @666_mancer on Twitter posted two separate Excel spreadsheets titled “Gruz 200-Ukraine” (Cargo 200) and “Gruz 200-Syria” (Cargo 200). The “Gruz 200-Syria” dataset posting appeared nearly eight months to the day after news reports surfaced about a deadly clash between forces affiliated with the Wagner Group and U.S. Special Forces in early February 2018 near Deir Ezzor, Syria.2 The “Gruz 200-Syria” dataset purported to document the reported deaths of military operatives who were killed in action while fighting in Syria during the 2015-2018 period. While the data entered was not always consistently formatted or input, a six-month long manual review of each of the associated Vkontakte and Odnoklassniki accounts for the 300 plus individuals listed conducted by Russian linguists on our team corroborated much of the information indicated in the “Gruz 200-Syria” dataset (Dataset A).
After our manual review, we narrowed our focus to entries where an individual Vkontakte account was associated with a person reported as killed in action (KIA) in Syria, then cleaned and updated that dataset (Dataset B-Wagner KIA Syria), eliminating duplicate entries and entries where the information could not be verified. While this dataset is not necessarily representative of all Russian PMSC operators or military contractors reported or actually killed in Syria in the 2015-2018 timeframe, we found that there were sufficient visual and textual indicators in the social media data that we could be reasonably confident that many of the individuals listed had served in the Russian armed forces and likely fought and died in Syria.
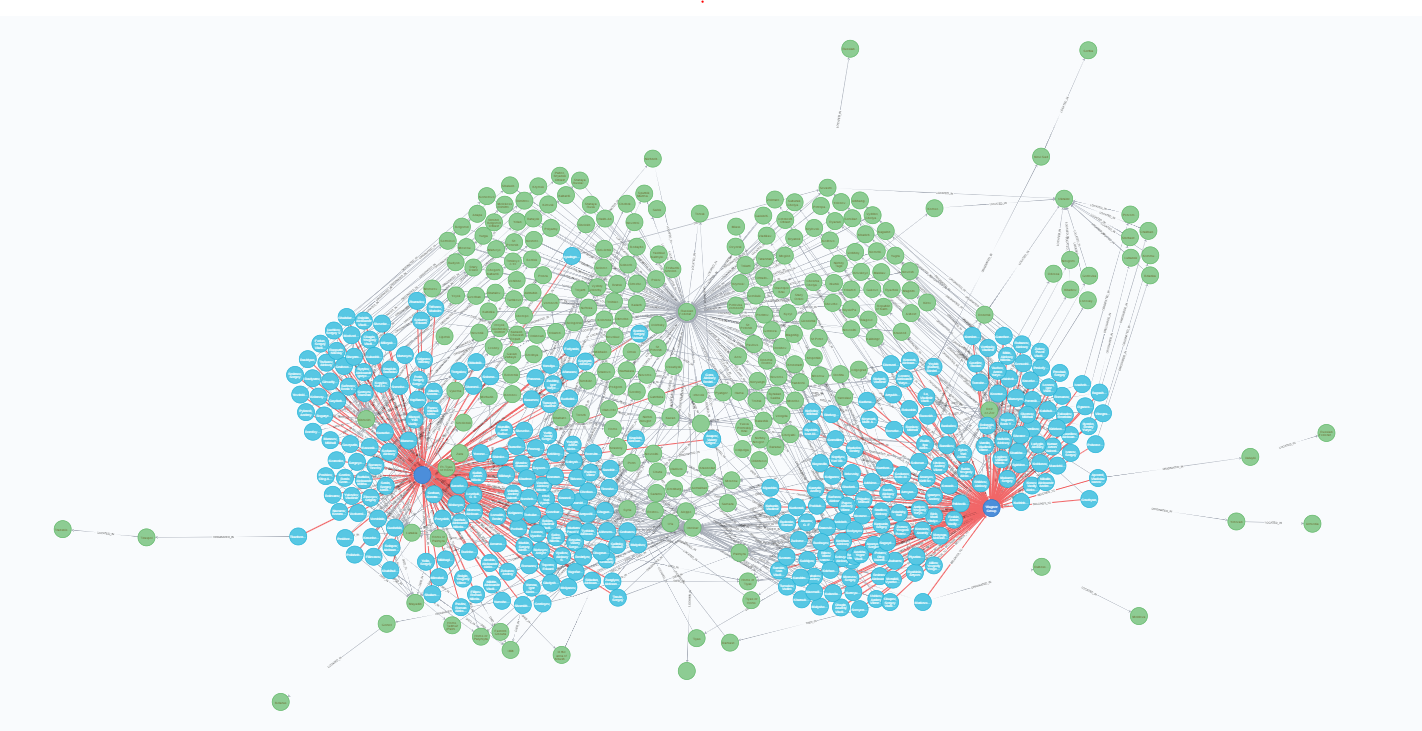
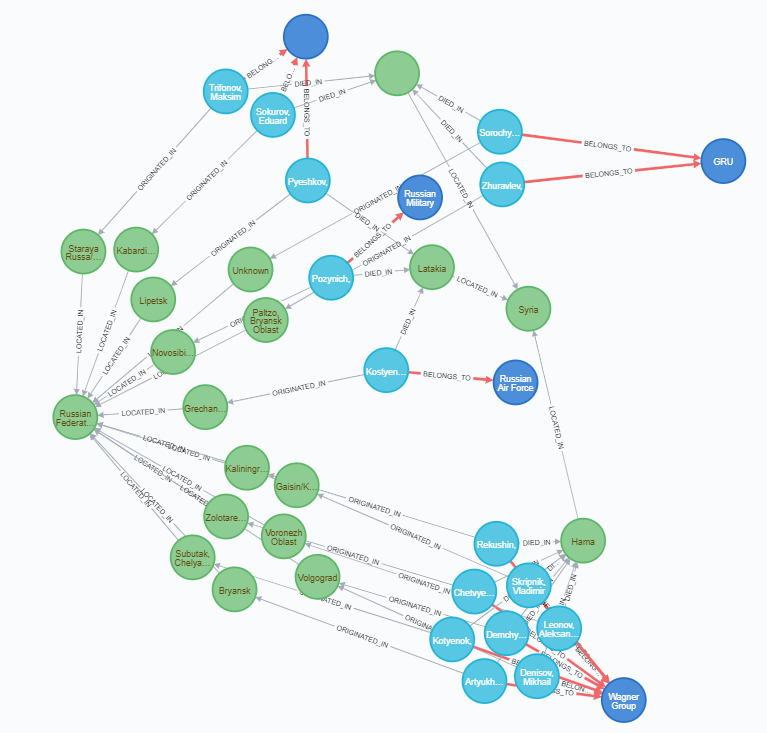
This finding raised our curiosity about whether and to what extent there were existing social ties between the individuals whose names and Vkontakte accounts appeared in the KIA Syria dataset. As can be seen below in Figures A-1 and A-2, a crude analysis using Neo4J, a popular Java language graph database management system, indicated that there is a great deal of connectivity between many of the individuals in the dataset. Common profile data such as membership in thematic community groups known on VK as “clubs,” place of residence, school provided a sort of crude sorting mechanism for more precise segmentation of demographic data that allowed us to begin to estimate the median age of PMSC operators
This initial finding led us to theorize that it might be possible to focus in closer on the constellation of Vkontakte friends and followers linked to those in this dataset who—like those in the KIA data—openly displayed attributes and affiliations consistent with service in the Russian military and time spent in either Donbas, Ukraine or Syria or both, where Russian PMSC operators have been known to operate. After refining our methodology further through a series of reviews data contained in a set of several thousand Vkontakte user accounts associated with a Vkontakte microblog that tracks Russian mercenary affairs, we determined that it is indeed possible to identify smaller subsets of individuals who claimed to have fought in Donbas or Syria or both and who openly advertised their friendship ties.
The graph below (Figure A-3) represents data culled from that review that indicated a network of close first-degree friendship ties between Rusich commander Alexey Milchakov and several individuals who appeared to have posted photos with geocoordinates indicating their presence in the vicinity of the Hayan Block in Homs, Syria during the spring of 2016 and spring/summer of 2017 when forces loyal to Bashar al-Assad conducted major offensives to retake critical energy infrastructure.
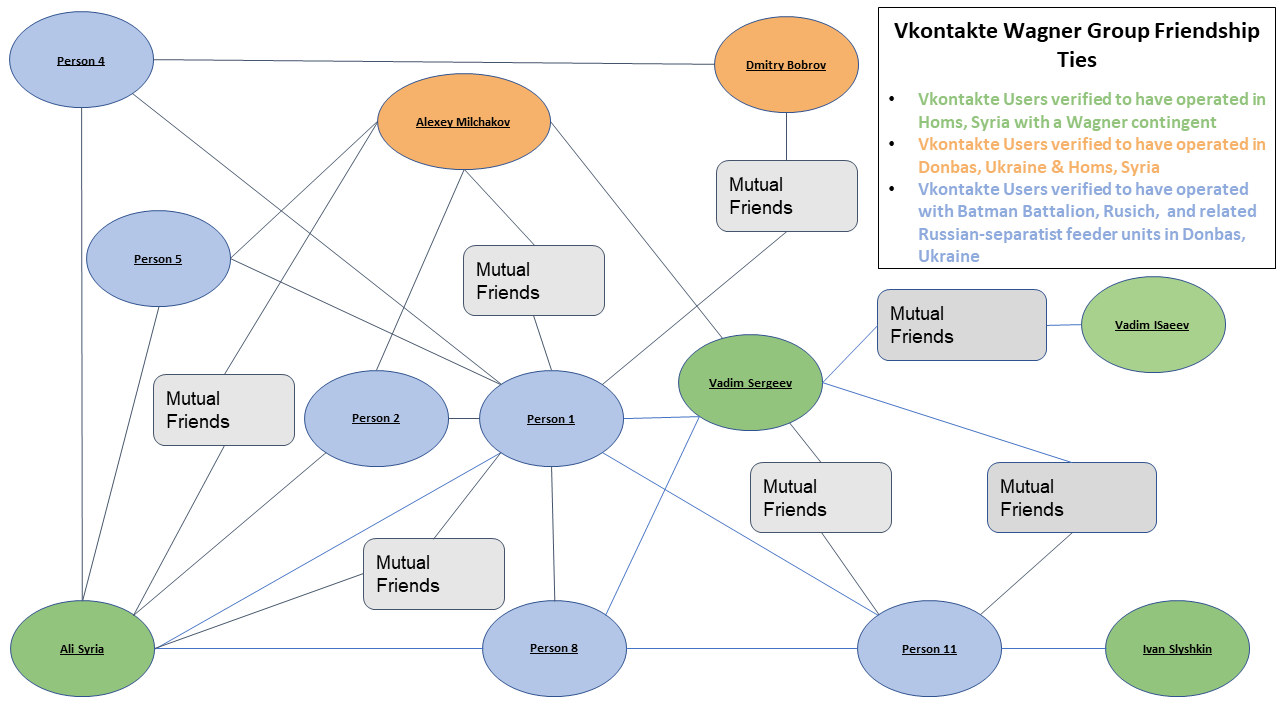
Figure A-3 Graph visualization of Vkontakte friendship network between Russian operatives who expressed interest in Wagner Group operations and whose location, image, text and/or video data indicated they fought in Donbas, Ukraine and/or Homs, Syria during the 2014-2017 timeframe. Lines between nodes indicate VK users listed each other as friends. Key individuals identified in the report as having fought in Ukraine and Syria such as Vadim Isaeev (green node, middle right) have many mutual friends in common listed on Vkontakte.
Citations
- Twitter apparently suspended the account for the Twitter user known @IvanSiderenko1 sometime in 2019, but the social media personality associated with this handle became well known for the hundreds of watermarked posts stamped with “IvanSiderenko” that appeared to depict scenes from the various battles for Palmyra and al-Shaer that took place from 2014 to 2019. As of May 5, 2020, Ivan Siderenko’s coverage of Tiger Force/ 5th Assault Corps activities in the vicinity of the Hayan Block and Palmyra was still available for public viewing on YouTube: source. Oleg Blokhin continues to be associated with Russian efforts to influence the narrative surrounding the activities of the “Wagner Group” in Syria, and he maintains a an active YouTube account (source) and Facebook account (source; archived version: source).
- Twitter user @666_mancer posted a Google Spreadsheet titled “Gruz 200-Syria” online: source.
