Table of Contents
- Introduction
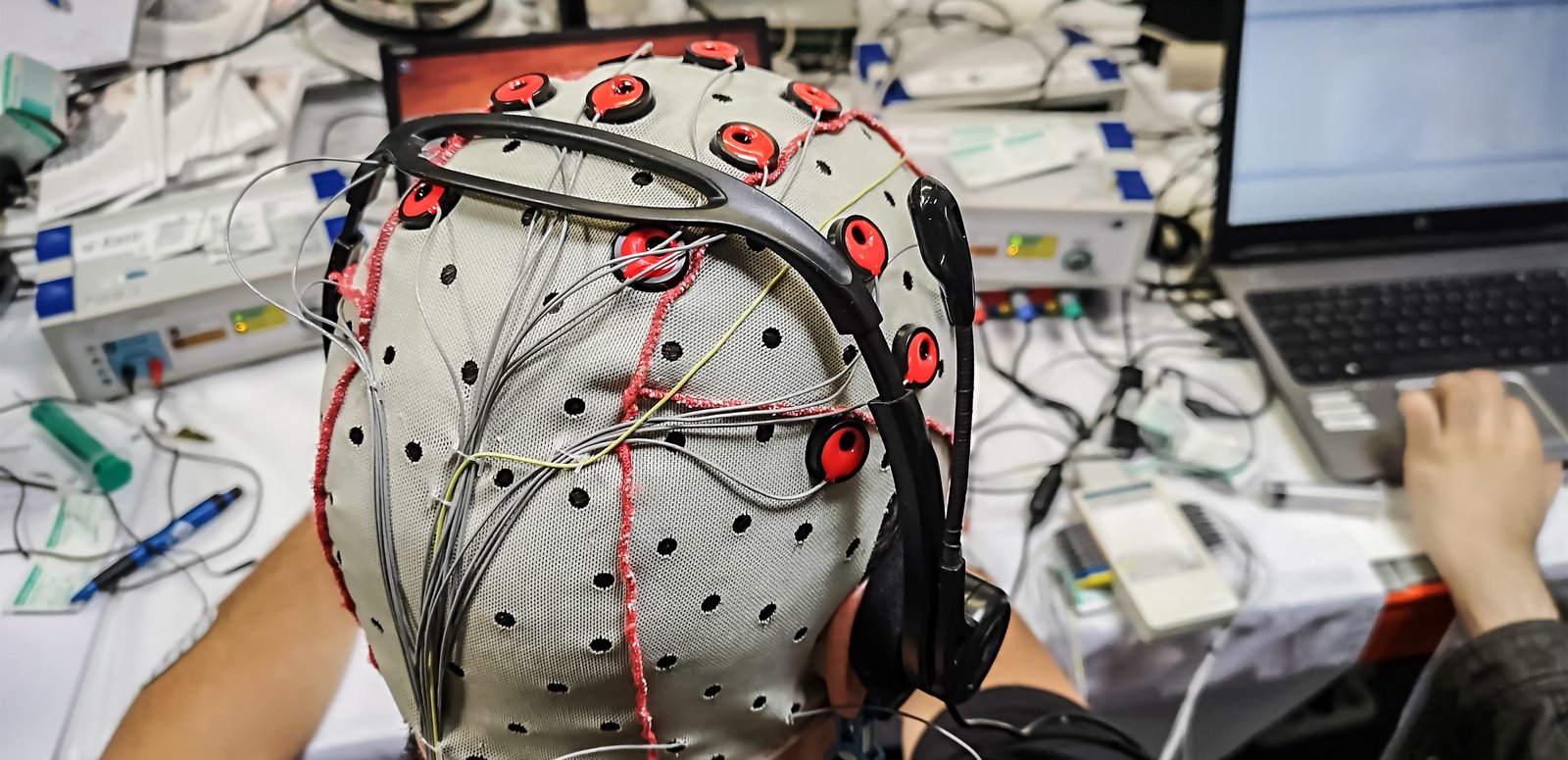
- Brain-Computer Interfaces: Fundamentals and Applications in Commercial and Medical Contexts
- Privacy and Security Challenges
- Current Legislative Landscape and Proposed Regulatory Approaches
- Proposed Approaches for Data Protection
- The Path Forward: Balancing Security, Ethics, and Regulation
Proposed Approaches for Data Protection
As brain-computer interface (BCI) technology continues to evolve, so too do the challenges of ensuring security, privacy, and accountability in its development and deployment. With federal regulatory uncertainty limiting oversight, this responsibility is increasingly shifting to states and industry leaders. However, without uniform standards, this fragmented approach risks inconsistencies in enforcement, loopholes in security, and inadequate consumer protections. Addressing these gaps requires a multi-faceted approach that prioritizes security at every stage of BCI development, holds manufacturers accountable for unsafe products, and ensures that regulatory solutions remain adaptable as the technology advances. Industry-driven best practices also play a crucial role in mitigating risks where formal regulation may be absent. Collaboration between policymakers, technologists, and consumer advocates will be essential to ensuring that BCI technology can evolve without exposing users to excessive privacy or security threats.
Building Security into BCI Development: Secure By Design
One of the most pressing risks associated with BCIs is the potential for security vulnerabilities due to poor software design and inadequate cybersecurity measures. Historically, many software and hardware developers have prioritized getting products quickly to markets over ensuring security, resulting in devices that lack critical protections against data breaches, manipulation, and unauthorized access.
The secure-by-design approach aims to address this by integrating security features at the earliest stages of development rather than as an afterthought.1 Secure-by-design advocates for integrating security into BCI technology from the initial design phase to the final product, ensuring that user security and privacy are prioritized throughout the entire lifecycle. The Cybersecurity and Infrastructure Security Agency (CISA) has championed this approach as part of its broader initiative to enhance cybersecurity across various sectors. Secure-by-design entails implementing security controls early in development, conducting thorough risk assessments, and continuously monitoring and updating security measures as technology evolves.
As noted earlier, unsecured-by-design products could expose users to unauthorized neural data collection, cyberattacks that manipulate brain signals, and misuse of biometric insights. Without proper safeguards, these devices could become a new vector for digital exploitation, making regulatory or industry-driven intervention critical. Security vulnerabilities should be mitigated before products reach consumers by enforcing mandatory encryption standards and requiring rigorous security testing before release.
“Security vulnerabilities should be mitigated before products reach consumers by enforcing mandatory encryption standards and requiring rigorous security testing.”
While some companies already implement basic security practices, the reality is that many BCI developers still operate with minimal oversight. Industry-wide adoption of secure-by-design principles could reduce security risks while providing a framework for best practices that states could incorporate into legislation.
For BCIs, this means that developers must consider potential security threats from the outset, designing systems that are resilient to attacks and protect user data from unauthorized access or manipulation. In practical terms, this could involve designing BCI devices with built-in encryption for all neural data, secure authentication mechanisms to prevent unauthorized access, and regular updates to address new vulnerabilities. By embedding these security measures from the start, the risk of exploitation is significantly reduced, offering greater protection to users who entrust their most sensitive data—literally their thoughts—to these devices.
Accountability for Software Manufacturers
One of the critical issues in the current technological landscape is the lack of accountability for manufacturers that release products with vulnerabilities.2 This gap in responsibility often leads to consumers being unwittingly exposed to significant risks, as many products enter the market without adequate security measures. As noted by CISA, “We have allowed a system where the cybersecurity burden is placed disproportionately on the shoulders of consumers…away from the producers of the technology,” highlighting the urgent need for a new model that ensures the safety and integrity of this technology.3
To address this need, legislation and regulations should establish clear liability for manufacturers and developers who fail to secure their products adequately. If a BCI device is released with easily exploitable vulnerabilities, the manufacturer should be held legally responsible for any harm that results from those flaws. This liability would act as a powerful incentive for companies to invest in rigorous security testing and validation processes before releasing their products to the public. As privacy and internet policy scholar Jim Dempsey suggests in a 2024 paper, a “rules-based floor” should be established as a minimum legal standard of care for software, which would focus on specific product features or behaviors that need to be included or avoided.4 Additionally, Dempsey advocates for a “process-based safe harbor” that shields developers from liability for hard-to-detect flaws, provided they adhere to recognized secure development practices.
Furthermore, liability should not only apply to the initial release of the product but also extend to ongoing support. Dempsey emphasizes this ongoing responsibility, suggesting that manufacturers must provide timely security updates and patches to address newly discovered vulnerabilities. Failure to do so should result in penalties or legal action, ensuring that companies remain vigilant in maintaining the security of their products over time. This approach balances the need for robust legal standards with the flexibility necessary to accommodate the complexities of software development, ultimately promoting a more secure technological environment.
Comprehensive Legislation
Consumers have the right to know how their data is being protected and what measures are in place to safeguard their privacy and security. Legislation should, therefore, grant consumers access to detailed information about the security practices of BCI devices and software. This transparency would provide consumers with the knowledge necessary to assess the risks associated with those products, empowering them to make informed decisions about their use. Additionally, the law should establish clear avenues for consumers to seek recourse if security breaches harm them. This could include the right to take legal action against manufacturers who fail to protect their data and access to compensation or support services in the event of a breach. By providing these rights, the legislation would help ensure that consumers are not left vulnerable or unsupported in the face of security failures.
Under the second Trump administration, it is likely that federal priorities will shift away from direct BCI regulation, placing greater responsibility on state governments to address neural data privacy, cybersecurity, and commercial oversight. Traditionally, there has been an expectation that emerging technologies would be addressed at the federal level, but as national agencies deprioritize consumer privacy regulations, protections will likely need to be enacted by the states.
“As national agencies deprioritize consumer privacy regulations, protections will likely need to be enacted by the states.”
This shift reinforces the fragmented nature of U.S. technology regulation. Without federal action, different states may implement conflicting standards, making compliance complex for businesses operating across multiple jurisdictions. While some states might enact strict neural data privacy laws, others could take a more permissive approach, allowing industry-led self-regulation to dictate standards.
The lack of federal coordination raises concerns about enforcement inconsistencies and potential loopholes in state laws that could be exploited by companies handling neural data. Without federal coordination, BCIs could become subject to widely varying standards depending on where a consumer is located. This creates an uneven playing field for businesses and increases the risk that companies will exploit regulatory gaps to bypass stricter privacy protections. State efforts would benefit from greater cross-state collaboration to establish shared principles for neural data protection. While federal legislation may not be viable, multi-state agreements could help create consistency in how BCIs are governed, ensuring that security and privacy protections apply regardless of jurisdiction.
Citations
- “Secure by Design,” Cybersecurity and Infrastructure Security Agency, U.S. Department of Homeland Security, source.
- Eduard Kovacs, “Medtronic Releases Patches for Cardiac Device Flaws Disclosed in 2018, 2019,” SecurityWeek, February 3, 2020, source.
- “Secure by Design,” Cybersecurity and Infrastructure Security Agency, U.S. Department of Homeland Security, source.
- Jim Dempsey, “Standards for Software Liability: Focus on the Product for Liability, Focus on the Process for Safe Harbor,” Lawfare, January 23, 2024, source.